Hashing is a crucial process in information security, transforming input data into fixed-size strings called hash values, which are irreversible and help ensure data integrity, authentication, and password security. It supports various applications like digital signatures, blockchain, and secure password storage. Affected: Information Security, Digital Signatures, Password Storage, Blockchain
Keypoints :
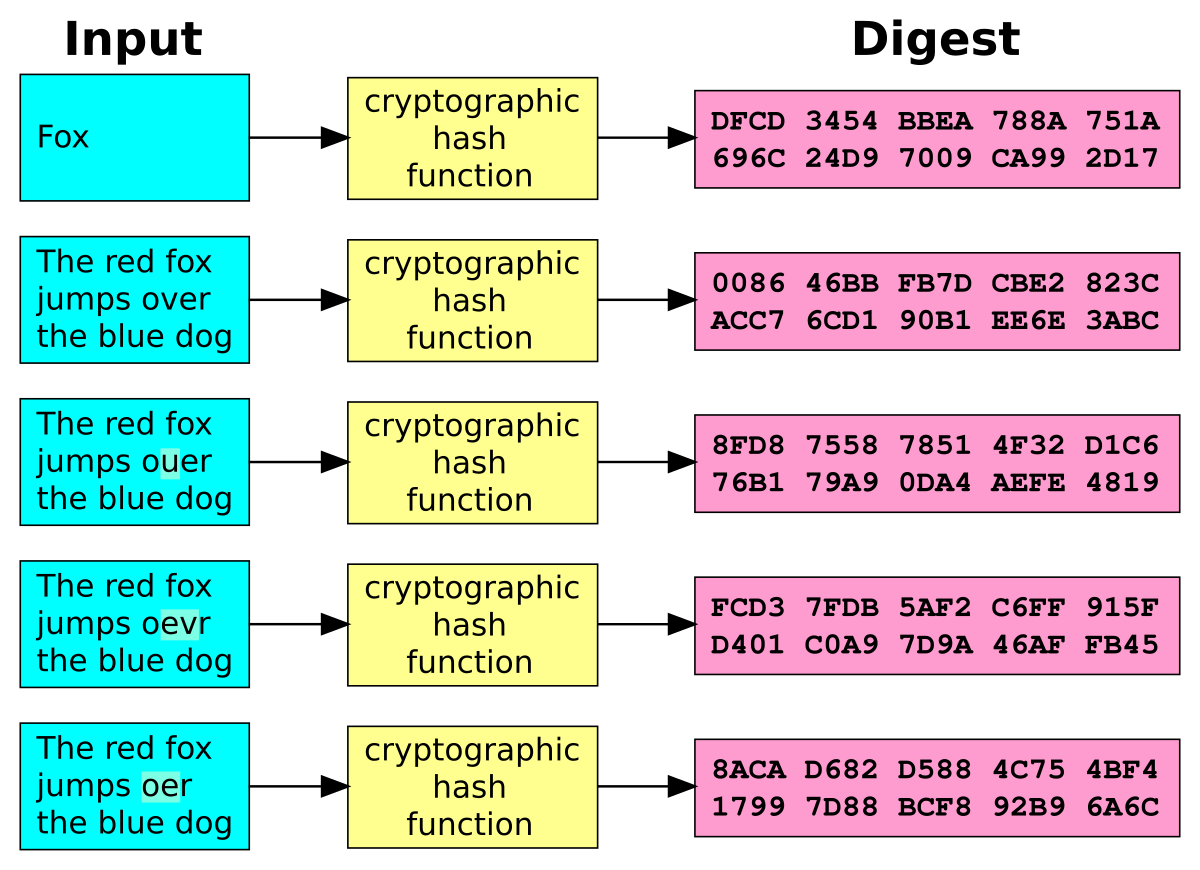
- Hashing converts any input into a fixed-size string called a hash value, which is a one-way function.
- It is important for integrity verification, digital signatures, password storage, and secure blockchain transactions.
- Common hashing algorithms include MD5, SHA-1, SHA-2, SHA-3, and BLAKE2.
- Hash functions must be deterministic, fast to compute, resistant to collisions, and able to withstand pre-image attacks.
- Salt is used in password hashing to mitigate rainbow table attacks by adding randomness to input before hashing.
- SHA is a family of secure hashing algorithms designed by the NSA and recommended for secure applications.
- Advanced hashing techniques include bcrypt and Argon2, both designed for secure password storage.
- Attacks on hash functions include collision attacks, pre-image attacks, and rainbow table attacks; countermeasures involve using salts and strong hash functions.