In this blog entry, we explore the tactics employed by the Black Basta and Cactus ransomware groups to compromise systems and exfiltrate sensitive information. They leveraged social engineering, remote access tools, and the BackConnect malware to establish persistent control over infected machines. Mitigating damages, businesses must adopt enhanced security protocols. Affected: Black Basta, Cactus, North America, Europe, Manufacturing, Financial and Investment Consulting, Real Estate
Keypoints :
- Black Basta and Cactus ransomware groups used BackConnect malware for persistent control and data exfiltration.
- Social engineering tactics included impersonating IT support via Microsoft Teams and Quick Assist.
- They utilized OneDrive and commercial cloud storage to distribute malicious files.
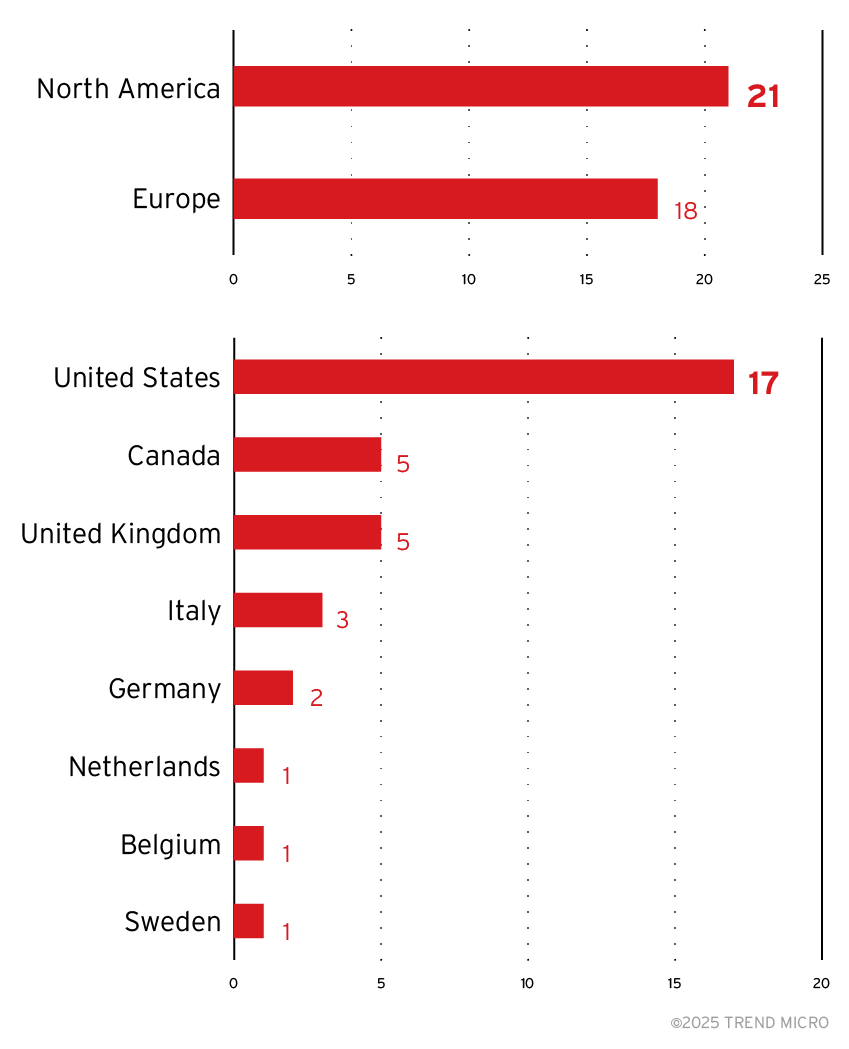
- The attacks were predominantly observed in North America and Europe, with the US being the hardest hit.
- In 2023, Black Basta reportedly extorted over 7 million from victims.
- Manufacturing sector faced the highest number of attacks, followed by Financial and Investment Consulting and Real Estate.
- Attacks were characterized by email bombing and social engineering to gain initial access.
- Malicious files were often concatenated and extracted to introduce BackConnect malware.
- Trend Micro provides insights on improving security against such ransomware threats.
MITRE Techniques :
- T1499 – Endpoint Denial of Service: Attackers used Quick Assist to manipulate users into providing unauthorized access.
- T1071.001 – Application Layer Protocol: Abuse of Microsoft Teams for impersonation and data exfiltration.
- T1140 – Network Sniffing: The attackers leveraged backdoor remote control through BackConnect malware.
- T1070.004 – Indicator Removal on Host: Utilized OneDrive to retain crime-related materials with hidden configurations.
- T1082 – System Information Discovery: Extracted user credentials and sensitive information post-infiltration.
Indicator of Compromise :
- [IP Address] 38.180.25[.]3
- [IP Address] 45.8.157[.]199
- [IP Address] 5.181.3[.]164
- [Domain] pumpkinrab[.]com
- [URL] hxxps://sfu11[.]s3[.]us-east-2[.]amazonaws[.]com/js/kb052117-01[.]bpx
Full Story: https://www.trendmicro.com/en_us/research/25/b/black-basta-cactus-ransomware-backconnect.html