The Earth Minotaur threat group has reactivated the MOONSHINE exploit kit, presenting a multiplatform threat to both Android and Windows systems. The updated kit is more sophisticated than before, supporting a multitude of exploits and has been linked to numerous indicators of compromise (IoCs), including domains and malicious IP addresses. Affected: Android devices, Windows computers, instant messaging applications, organizations monitoring network security
Keypoints :
- Earth Minotaur threat group revived the MOONSHINE exploit kit, initially discovered in 2019.
- The updated MOONSHINE kit had over 55 servers in 2024.
- MOONSHINE targets vulnerabilities in Android’s instant messaging apps and Chromium-based browsers on Windows.
- DarkNimbus, the backdoor delivered by MOONSHINE, has two variants affecting Android and Windows devices.
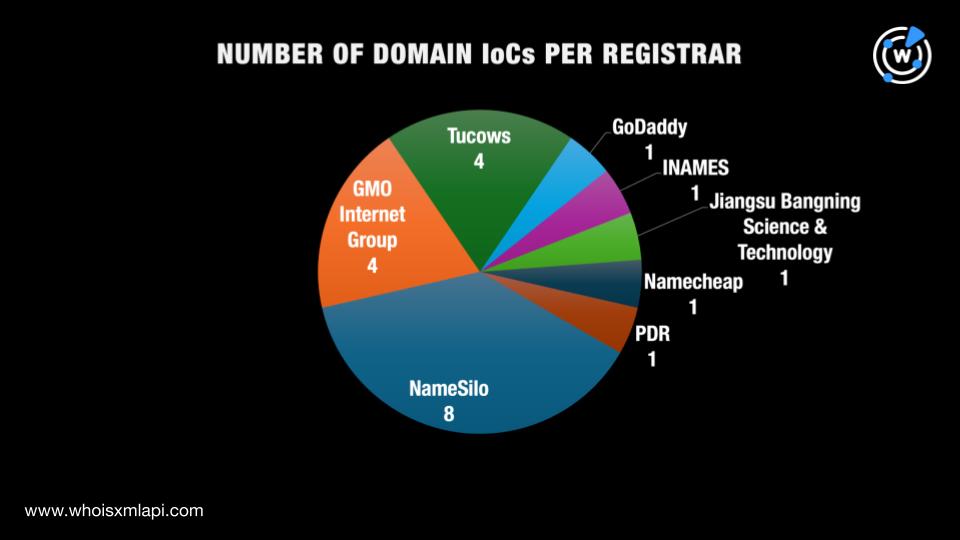
- Researchers identified 53 IoCs associated with the attack, including 44 domains and nine IP addresses.
- WHOIS and DNS queries have revealed further details about these IoCs.
- Additional artifacts connected to the threat were identified, including email-connected domains and historical WHOIS records.
- Research findings can be downloaded from the company’s website.
MITRE Techniques :
- TA0011: Initial Access – The Earth Minotaur group utilized the MOONSHINE exploit kit to gain access to systems via vulnerabilities in Android instant messaging apps.
- TA0002: Execution – The DarkNimbus backdoor was executed upon successful exploitation.
- TA0003: Persistence – The backdoor facilitates persistent access on Android and Windows devices.
- TA0004: Credential Access – Potential for credential harvesting via compromised applications.
- TA0005: Discovery – IoCs tracking revealed extensive DNS queries and domain resolutions.
Indicator of Compromise :
- [Domain] tibetonline[.]info
- [Domain] ansec[.]com
- [Domain] cloudvn[.]info
- [Domain] symantke[.]com
- [IP Address] 103[.]255[.]179[.]186
Full Story: https://circleid.com/posts/the-moonshine-exploit-kit-and-the-darknimbus-backdoor-in-the-dns-spotlight