The study highlights a surge in macOS infostealers targeting users across various sectors. Notably, the Atomic, Poseidon, and Cthulhu stealers are prevalent, employing advanced techniques to collect sensitive information, leading to significant risks for data breaches and financial losses. It emphasizes the importance of proactive security measures and utilizes detection tools like Cortex XDR to combat these threats. Affected: macOS users, organizations, financial sector, technology sector
Keypoints :
- An increase in macOS infostealers identified in 2024, with a 101% rise between last two quarters.
- Infostealers are capable of stealing a wide range of sensitive information, leading to data breaches.
- Three main macOS infostealers discussed: Atomic Stealer, Poseidon Stealer, Cthulhu Stealer.
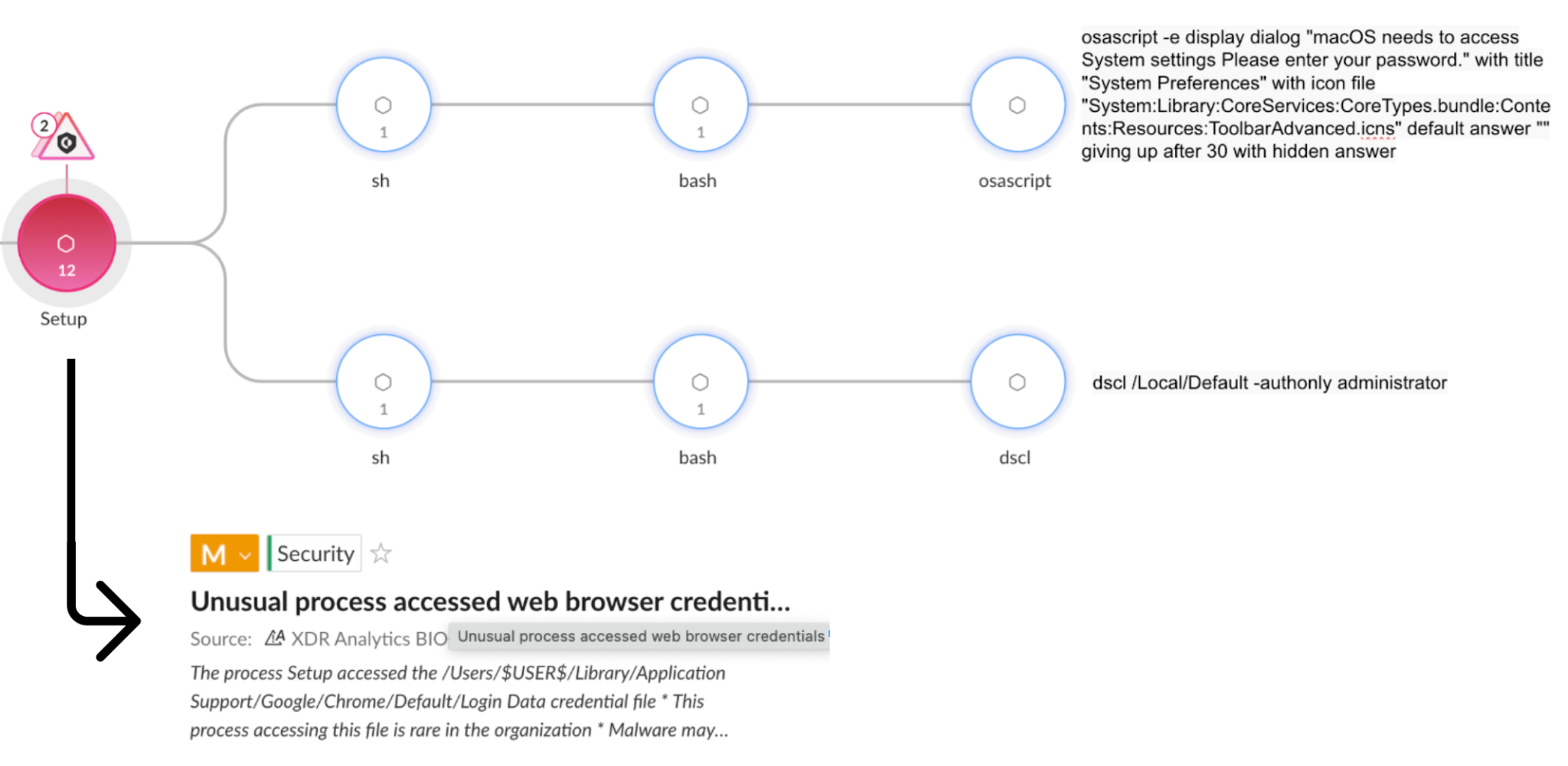
- Infostealers often exploit the AppleScript framework for execution and social engineering attacks.
- Cortex XDR and XSIAM provide protection against these threats through advanced detection capabilities.
- Recommended actions include multi-layered defense strategies and the use of telemetry data for detection.
MITRE Techniques :
- Tactics: Credential Access (TA0006), Techniques: Collection (TA0009) – Infostealers collect sensitive information such as passwords and financial details.
- Tactics: Initial Access (TA0001), Techniques: Phishing (T1566) – Poseidon Stealer spreads via malicious spam emails.
- Tactics: Execution (TA0002), Techniques: Command and Scripting Interpreter (T1059) – Usage of AppleScript for executing malicious activities.
Indicator of Compromise :
- SHA256: 599e6358503a0569d998f09ccfbdeaa629d8910f410e26df0ffbd68112e77b05
- SHA256: 9f4f286e5e40b252512540cc186727abfb0ad15a76f91855b1e72efb006b854c
- SHA256: 2d232bd6a6b6140a06b3cf59343e3e2113235adcf3fb93e78fa3746d9679cfc3
- IP Address: 94.142.138[.]177
- IP Address: 194.59.183[.]241
Full Story: https://unit42.paloaltonetworks.com/macos-stealers-growing/