XE Group, a long-standing cybercriminal organization, has shifted its focus from credit card skimming to sophisticated targeted information theft using newly discovered vulnerabilities. Their operations underscore their adaptability and persistent threat to supply chains in the manufacturing and distribution sectors. Affected: Manufacturing and Distribution sectors, VeraCore software, Supply Chains
Keypoints :
- XE Group has been active since at least 2013, initially focusing on credit card skimming and password theft.
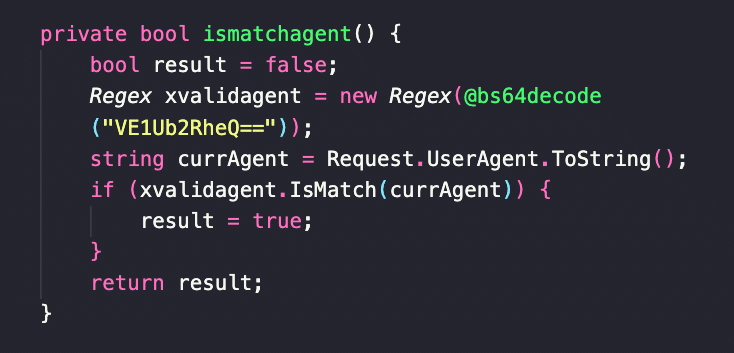
- The group exploited a previously undocumented vulnerability in VeraCore software for SQL Injection attacks.
- XE Group’s operations have transitioned to information theft, targeting supply chains starting in 2024.
- The group maintains long-term access to compromised systems with reactivated webshells.
- XE Group demonstrates advanced tactics, including the exploitation of zero-day vulnerabilities.
- Recently discovered webshell variants indicate evolving techniques in data exfiltration and persistence.
MITRE Techniques :
- T1190: Exploit Public-Facing Application – XE Group exploited SQL Injection vulnerabilities in their attacks.
- T1059: Command and Scripting Interpreter: PowerShell – PowerShell scripts were used to execute payloads and maintain access.
Indicator of Compromise :
- [MD5] 57abb73b7844f2308d9c62954e6e8b7f
- [SHA1] 032dd95a1299f37aaa76318945e030eb7da94da9
- [SHA256] 680b7e8ec8204975c5026bcbaf70f7e9620eacdd7bf72e5476d17266b4a7d316
- [IP Address] 171.227.250.249
- [IP Address] 222.253.102.94
Full Story: https://intezer.com/blog/research/xe-group-exploiting-zero-days/