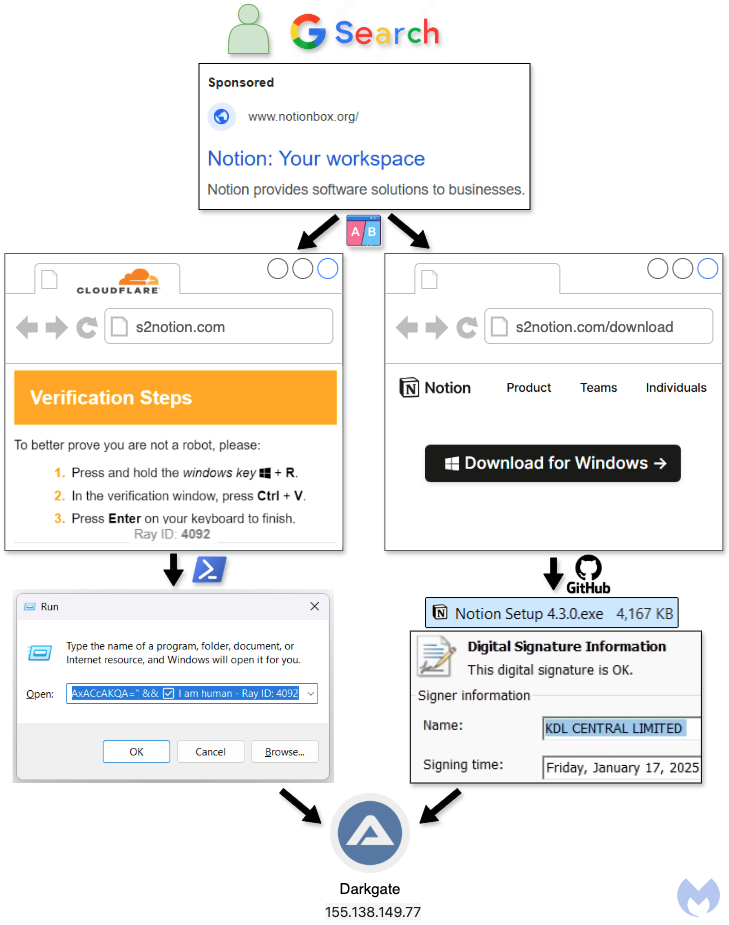
This article discusses recent malware campaigns utilizing the “ClickFix” technique, which misleads users into executing malicious code through fake CAPTCHA pages. The campaigns have targeted brands like Notion, employing both ClickFix and traditional file download methods to deliver the DarkGate malware loader. Affected: Notion
Keypoints :
- Numerous malware campaigns have emerged using the “ClickFix” technique.
- ClickFix involves fake CAPTCHA pages where users are tricked into executing code.
- Malicious Google ads have been increasingly used for ClickFix attacks.
- A recent campaign targeted the Notion brand, employing two delivery techniques.
- The first delivery method involved PowerShell code execution through a fake verification page.
- The second delivery method involved a malicious executable disguised as a Notion installer.
- Both methods ultimately delivered the DarkGate malware loader.
- Malwarebytes detects the payloads as Trojan.Dropper and Backdoor.DarkGate.
MITRE Techniques :
- T1071.001 – Application Layer Protocol: The malware uses PowerShell to communicate with its command and control server.
- T1203 – Exploitation for Client Execution: Users are tricked into executing malicious code via social engineering tactics.
- T1059.001 – Command and Scripting Interpreter: PowerShell is used to run commands that download and execute the malware.
- T1070.001 – Indicator Removal on Host: The obfuscation of HTML source code is used to hide malicious activities.
Indicator of Compromise :
- [domain] notionbox[.]org
- [url] s2notion[.]com/in.php?action=1
- [url] s2notion[.]com/in.php?action=2
- [file hash] 6b6676267c70fbeb3257f0bb9bce1587f0bdec621238eb32dd9f84b2bcd7e3ea4fe8bbc88d7a8cc0eec24bd74951f1f00b5127e3899ae53de8dabd6ff417e6db
- [url] raw[.]githubusercontent[.]com/herawtisabela1992/check/refs/heads/main/920836164_x64.exe
- Check the article for all found IoCs.
Full Research: https://www.malwarebytes.com/blog/cybercrime/2025/01/clickfix-vs-traditional-download-in-new-darkgate-campaign