Wiz Research discovered a publicly accessible ClickHouse database belonging to DeepSeek, exposing over a million lines of sensitive information, including chat history and API secrets. The database was secured promptly after disclosure. This incident highlights the security risks associated with rapidly adopted AI technologies. Affected: DeepSeek
Keypoints :
- Wiz Research identified a publicly accessible ClickHouse database linked to DeepSeek.
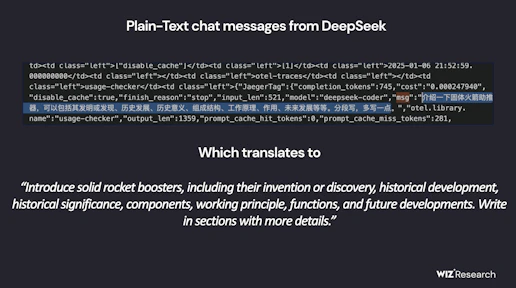
- The database contained over a million lines of sensitive log streams and internal data.
- DeepSeek is a Chinese AI startup known for its DeepSeek-R1 reasoning model.
- The database was accessible without authentication, raising significant security concerns.
- Wiz Research disclosed the issue to DeepSeek, which secured the exposure promptly.
- The incident underscores the importance of security in AI technologies.
- Rapid adoption of AI services often leads to overlooked security measures.
- Security teams must collaborate with AI engineers to protect sensitive data.
MITRE Techniques :
- TA0001 – Initial Access: Exploiting a publicly accessible database without authentication.
- TA0002 – Execution: Executing arbitrary SQL queries via the ClickHouse HTTP interface.
- TA0003 – Persistence: Potential for privilege escalation through database access.
Indicator of Compromise :
- [url] oauth2callback.deepseek.com:9000
- [url] dev.deepseek.com:9000
- [others ioc] ClickHouse database
- [others ioc] log_stream table
- Check the article for all found IoCs.
Full Research: https://www.wiz.io/blog/wiz-research-uncovers-exposed-deepseek-database-leak