Cybercriminals are leveraging fake CAPTCHA systems to deliver malware, particularly targeting cryptocurrency communities through Telegram. This sophisticated tactic involves hijacking discussions on X platform and using deceptive bots to execute malicious scripts. Affected: X platform, Telegram
Keypoints :
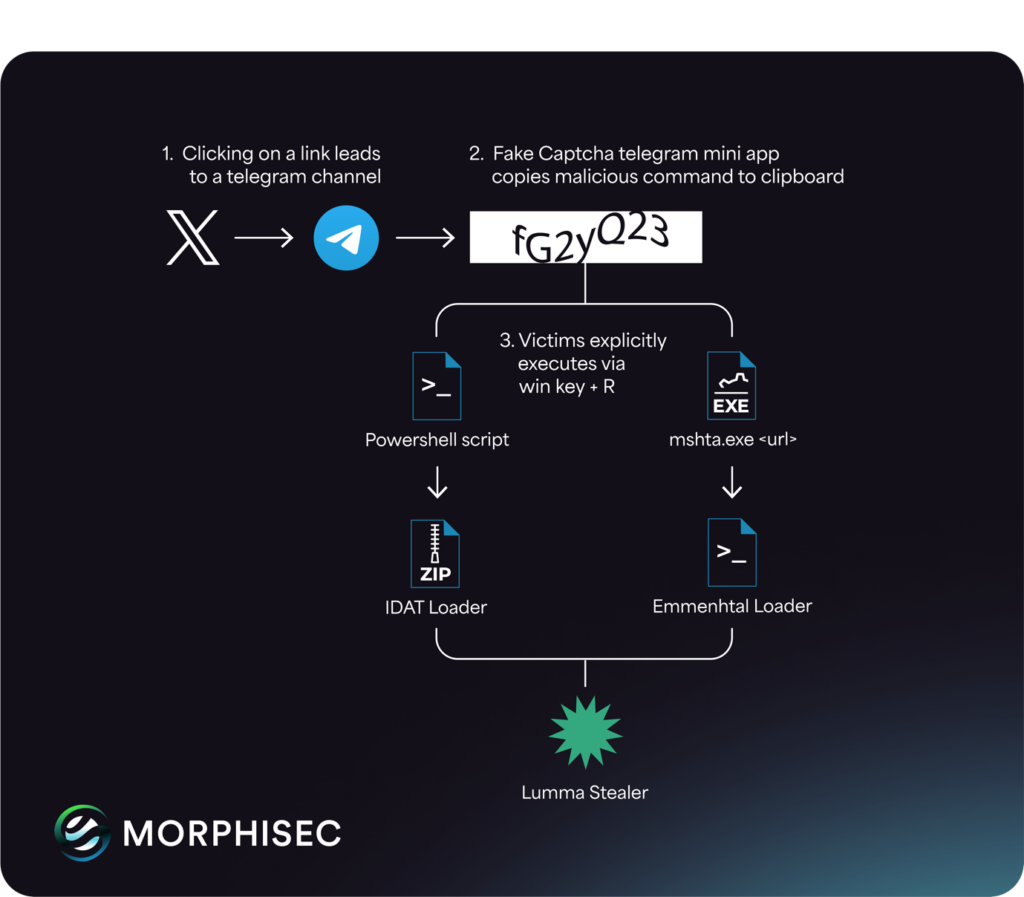
- Cybercriminals have evolved from basic fake URL-based CAPTCHAs to more sophisticated Telegram-based approaches.
- The campaign primarily targets cryptocurrency communities, deceiving users into executing malicious scripts.
- Attackers hijack threads on the X platform to lure victims into Telegram channels.
- Victims are prompted to complete a CAPTCHA verification using a fake bot mimicking a legitimate service.
- The Lumma Stealer malware is delivered through multiple loaders, including IDAT and Emmenthal Loaders.
MITRE Techniques :
- T1071.001 – Application Layer Protocol: Attackers use Telegram for command and control communications.
- T1071.001 – Application Layer Protocol: Fake CAPTCHA verification mimics legitimate user validation processes.
- T1203 – Exploitation for Client Execution: Victims are tricked into executing malicious scripts.
- T1204.002 – User Execution: Users are deceived into executing commands copied to their clipboard.
- T1059.001 – PowerShell: Malicious PowerShell scripts are executed to deliver the Lumma Stealer payload.
Indicator of Compromise :
- [domain] truecoders[.]cyou
- [domain] byteguard[.]cyou
- [domain] rainstorm[.]cyou
- [domain] codecrafters[.]cyou
- [domain] stem-clasping[.]kliplaxupoi[.]shop
- Check the article for all found IoCs.
Full Research: https://www.infostealers.com/article/captcha-chaos-from-x-threads-to-telegram/