The Clop ransomware group has exploited critical vulnerabilities (CVE-2024-50623 and CVE-2024-55956) in Cleo’s managed file transfer software, leading to unauthorized access and data exfiltration. Imperva has observed over 1 million attempts to exploit these vulnerabilities across various industries, particularly targeting the Financial Services and Government sectors. Affected: Cleo, Financial Services, Government
Keypoints :
- Clop ransomware group exploited vulnerabilities in Cleo software.
- CVE-2024-50623 allows unrestricted file uploads and downloads, leading to potential remote code execution.
- CVE-2024-55956 permits unauthenticated users to execute arbitrary commands on the system.
- Over 1 million incidents of attempted exploitation were monitored, targeting nearly 10,000 sites in 60 countries.
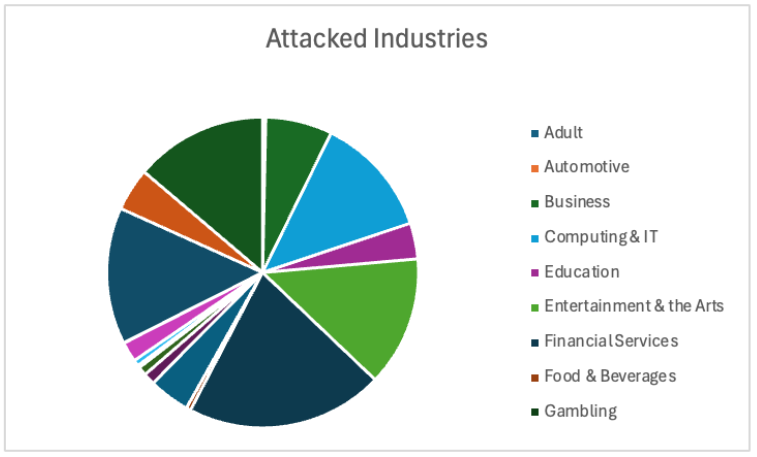
- Primary targets included the Financial Services and Government sectors.
- Attacks involved writing files to the target system and executing PowerShell scripts for further exploitation.
- Clop ransomware also exfiltrates sensitive data before encrypting files, adding an extortion component.
- Proactive vulnerability management and timely patching are essential to mitigate risks.
MITRE Techniques :
- T1071.001 – Application Layer Protocol: Attackers used PowerShell scripts to communicate with external IP addresses.
- T1203 – Exploitation for Client Execution: Exploited CVE-2024-50623 for unrestricted file uploads.
- T1059.001 – Command and Scripting Interpreter: Utilized PowerShell for executing commands on the system.
- T1070.001 – Indicator Removal on Host: Attackers deleted JAR files to avoid detection.
- T1486 – Data Encrypted for Impact: Clop ransomware encrypted files and demanded ransom for decryption keys.
Indicator of Compromise :
- [IP Address] 103[.]140[.]62[.]43
- [IP Address] 146[.]190[.]133[.]67
- [IP Address] 162[.]240[.]110[.]250
- [IP Address] 213[.]136[.]77[.]58
- Check the article for all found IoCs.
Full Story: https://www.imperva.com/blog/imperva-protects-against-the-exploited-cves-in-the-cleo-data-theft-attacks/