The article discusses two campaigns by a new threat group named Silent Lynx, targeting government entities in Kyrgyzstan, particularly the National Bank and Ministry of Finance. The campaigns involve sophisticated phishing attacks using malicious ISO files and C++ loaders, along with Golang implants for reverse shells. The group employs Telegram for command and control and data exfiltration. Affected: Kyrgyzstan, Turkmenistan
Keypoints :
- Silent Lynx targets government entities in Kyrgyzstan and Turkmenistan.
- The group uses phishing emails with malicious attachments to initiate attacks.
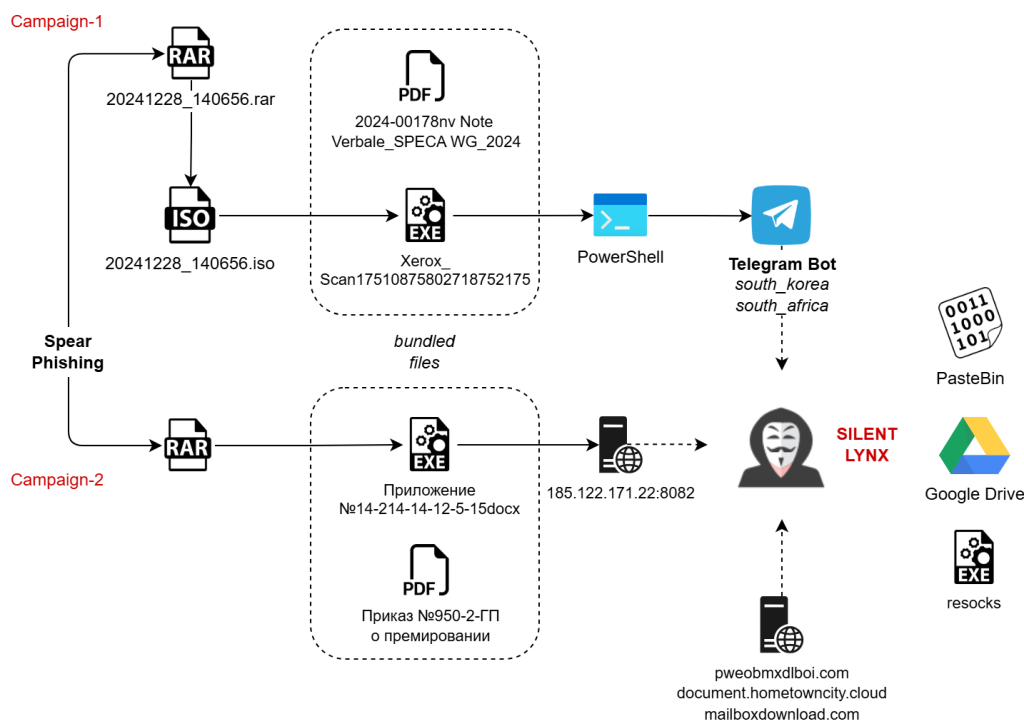
- Campaign 1 involves a malicious ISO file containing a C++ loader and PowerShell script.
- Campaign 2 uses a password-protected RAR file with a malicious Golang executable.
- Decoy documents are crafted to appear legitimate, reducing suspicion.
- Telegram bots are utilized for command execution and data exfiltration.
- Infrastructure includes domains and tools for maintaining persistence on victim systems.
- Attribution suggests connections to a Kazakhstan-based group known as YoroTrooper.
MITRE Techniques :
- Reconnaissance (T1589.002): Gather Victim Identity Information: Email Addresses.
- Initial Access (T1204.002): User Execution: Malicious File.
- Initial Access (T1078.002): Valid Accounts: Domain Accounts.
- Execution (T1059.001): Command and Scripting Interpreter: PowerShell.
- Persistence (T1547.001): Registry Run Keys / Startup Folder.
- Credential Access (T1056.001): Input Capture: Keylogging.
- Credential Access (T1552.001): Unsecured Credentials: Credentials In Files.
- Discovery (T1087): Account Discovery.
- Discovery (T1083): File and Directory Discovery.
- Collection (T1560.001): Archive Collected Data: Archive via Utility.
- Exfiltration (T1567.002): Exfiltration to Cloud Storage.
Indicator of Compromise :
- [file name] 147.exe
- [file hash] efb700681713cd50a2addd1fea6b7ee80c084467d3e87668688b9f06642062ba
- [file name] Xerox_Scan17510875802718752175.exe
- [file hash] e6f76a73180b4f2947764f4de57b52d037b482ece1a88dab9d3290e76be8c098
- [domain] hxxps://pweobmxdlboi[.]com
- Check the article for all found IoCs.
Full Research: https://www.seqrite.com/blog/silent-lynx-apt-targeting-central-asian-entities/