Device code phishing is rapidly expanding, driven by public toolkits, PhaaS offerings such as EvilTokens and Tycoon 2FA, and AI-assisted “vibe coded” kits that dynamically generate device codes on demand. Proofpoint observed campaigns targeting Microsoft 365 and Google accounts through impersonation, QR codes, PDFs, and compromised senders, with activity linked to TA4903, ODx, Kali365, ARTokens, and Storm-1167. #EvilTokens #Tycoon2FA #TA4903 #ODx #Kali365 #ARTokens #Storm1167
Keypoints
- Device code phishing is surging across the threat landscape, with new tools appearing frequently.
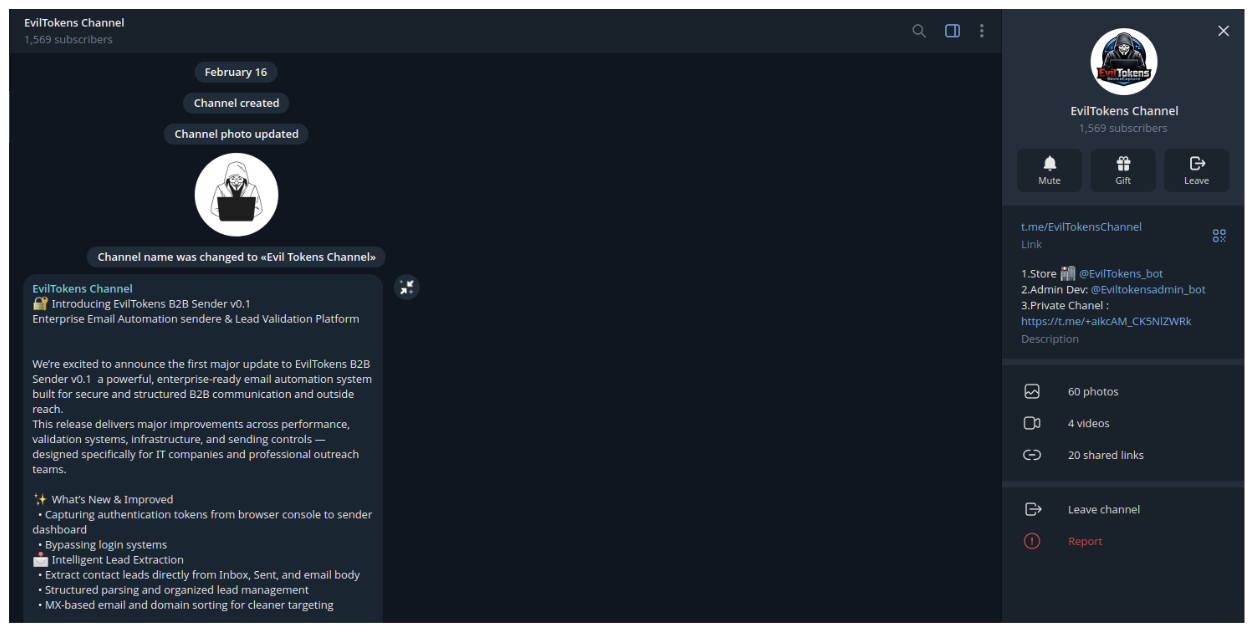
- The rise coincides with publicly released criminal toolkits and phishing-as-a-service offerings.
- Many campaigns use AI-generated or “vibe coded” kits, though it is unclear whether actors are copying public tools or generating near-identical ones.
- Attackers abuse the OAuth 2.0 device authorization flow to capture tokens and compromise Microsoft 365 and, less often, Google accounts.
- Current campaigns often generate device codes only after a victim clicks a lure, removing the old 15-minute expiration weakness.
- Observed lures include buttons, hyperlinks, documents, QR codes, and blank or poorly crafted emails, often impersonating Microsoft, DocuSign, SharePoint, Adobe, or government entities.
- Proofpoint recommends blocking device code flow where possible, requiring compliant devices, and training users not to enter device codes from untrusted sources.
MITRE Techniques
- [T1566.002 ] Phishing: Spearphishing Link – Victims receive URLs in emails, buttons, or text that lead to device code phishing pages. (’emails can include URLs… that lead to the device code phishing landing pages’)
- [T1566.001 ] Phishing: Spearphishing Attachment – Attackers use PDF attachments to deliver QR codes or links to malicious landing pages. (‘sent “salary notifications” emails containing a PDF attachment’)
- [T1204.001 ] User Execution: Malicious Link – The attack chain starts when the user clicks the phishing URL and triggers code generation or redirection. (‘when a user clicks on the initial phishing link’)
- [T1078 ] Valid Accounts – Stolen authentication tokens are used to access the victim’s Microsoft 365 or other enterprise accounts. (‘capture authentication tokens… used to access the target’s account’)
- [T1550.004 ] Use Alternate Authentication Material: Web Session Cookie – Captured authentication tokens are reused to access services without needing the original login. (‘capture authentication tokens, which can then be used to access the target’s account’)
- [T1528 ] Steal Application Access Token – The actor captures tokens from the device code flow for later use. (‘it allows the threat actor to capture authentication tokens’)
- [T1091 ] Replication Through Removable Media – The QR code prompts users to transfer information from one medium to another? Not applicable; omitted because not explicitly described in the article.
- [T1036 ] Masquerading – Threat actors impersonate Microsoft, DocuSign, SharePoint, Adobe, HR, government entities, and courts to appear legitimate. (‘landing page impersonating Microsoft and DocuSign’)
- [T1190 ] Exploit Public-Facing Application – Attackers abuse legitimate Microsoft device authorization portals and cloud-hosted infrastructure to facilitate the phishing flow. (‘legitimate Microsoft device authorization process’)
- [T1656 ] Hijack Execution Flow – The attacker-controlled device code workflow redirects the victim through a crafted sequence to capture the token. (‘initiates an attack sequence leveraging the legitimate Microsoft device authorization process’)
- [T1027 ] Obfuscated Files or Information – QR codes, shortened/redirected URLs, and layered redirections hide the final phishing destination. (‘redirected via a Cloudflare Workers URL to a custom filtering page’)
- [T1583.006 ] Acquire Infrastructure: Web Services – Threat actors host landing pages and redirectors on Cloudflare Workers and other web services. (‘hosted on actor-controlled infrastructure, but the rest of the attack chain was deployed to cloud services’)
- [T1585.001 ] Establish Accounts: Social Media Accounts – Telegram is used to advertise and distribute the kit. (‘first advertised on Telegram in February 2026’)
- [T1201 ] Password Policy Discovery – Not explicitly described; omitted because the article does not mention password policy discovery.
Indicators of Compromise
- [Domains ] EvilTokens landing domains – onedrive-7tu[.]techroboticslabmade-techie-com-s-account[.]workers[.]dev, voicemail-59f[.]admin-treyripple-com-s-account[.]workers[.]dev, and 2 more items
- [Domains ] EvilTokens landing domains – voicemail-wx7[.]mark-squires-expressrancnes-com-s-account[.]workers[.]dev, voicemail-lyr[.]nbuckley-cambek-com-s-account[.]workers[.]dev, and 2 more items
- [Domains ] Device code phishing domains – z6e43e5886fe-endpoint[.]com, 019d442e-endpoint[.]com, and other 10 items
- [Domains ] ODx device code phishing domains – stablewebsystems[.]de, marktkarree-langenfeld[.]de, and other 12 items
- [Domains ] TA4903 landing pages – audit-report-9767d3[.]fullerjp09[.]workers.dev, hti-245401512[.]hs-sites-na2[.]com
- [Domains ] ARTokens landing infrastructure – 7740f766-8d1d-46ad-a6bc-onedrive[.]p-9jluifuu[.]workers[.]dev, panel[.]hewktree[.]net
- [URLs ] Microsoft device login used in the phishing flow – https[:]//microsoft[.]com/devicelogin, hxxps://microsoft.com/devicelogin
- [Platforms/Services ] Cloud infrastructure and redirectors – Cloudflare Workers, Telegram, Microsoft 365
- [File types ] Phishing lures and attachments – PDF attachment, QR code
- [Threat kits / platforms ] Named kits and services – EvilTokens, Tycoon 2FA, ODx, Kali365, ARTokens
Read more: https://www.proofpoint.com/us/blog/threat-insight/device-code-phishing-evolution-identity-takeover