Kimsuky has evolved its PebbleDash and AppleSeed malware clusters with new variants, legitimate tooling like VSCode Tunneling and DWAgent, and infrastructure that hides C2 activity across South Korea and beyond. The campaign used spear-phishing, droppers, and post-exploitation tools to maintain persistence, steal information, and expand access while targeting government, defense, medical, and other sectors. #Kimsuky #PebbleDash #AppleSeed #HelloDoor #httpMalice #httpTroy #HappyDoor #DWAgent #VSCode
Keypoints
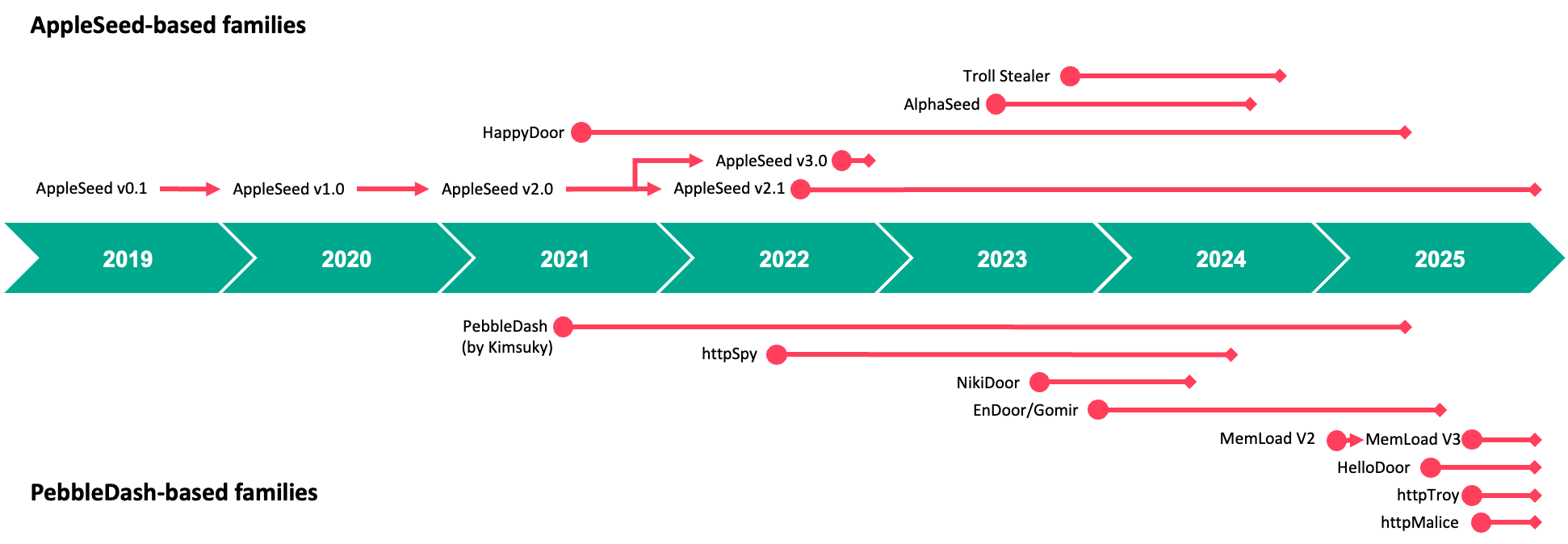
- Kimsuky refined its campaigns through multiple phases, introducing tactical shifts and new malware variants based on the PebbleDash platform.
- The group used spear-phishing emails, malicious attachments, and sometimes messenger contacts to achieve initial access.
- Droppers in formats such as JSE, SCR, PIF, and EXE delivered PebbleDash and AppleSeed malware families.
- Post-exploitation activity increasingly relied on legitimate tools, including Visual Studio Code Remote Tunneling and DWAgent, to reduce detection.
- Infrastructure frequently used free South Korean hosting, hacked websites, and tunneling services such as Cloudflare Quick Tunnels and Ngrok.
- Targets were concentrated in South Korea, but PebbleDash activity was also observed in Brazil and Germany, with strong interest in defense and government sectors.
- Evidence suggests the PebbleDash and AppleSeed clusters are operated by a common Kimsuky-affiliated actor with overlapping tradecraft and infrastructure.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – Initial access was achieved by sending malicious attachments disguised as documents (‘delivering spear-phishing emails containing malicious attachments disguised as documents’).
- [T1598 ] Phishing for Information – Targets were also contacted via messengers to lure them into opening malicious content (‘they also contact targets via messengers in some cases’).
- [T1059.007 ] JavaScript – JSE droppers were used to decode and launch embedded payloads (‘JSE droppers contain a minimum of two Base64-encoded blobs’).
- [T1027 ] Obfuscated Files or Information – Droppers hid payloads with Base64, XOR, dummy data, and encrypted strings (‘fully obfuscated using dummy data and encrypted strings’).
- [T1204.002 ] Malicious File – Malicious attachments were crafted to look like legitimate documents, installers, and photos (‘disguised as documents’, ‘product quotations, job offers, information guides’).
- [T1059.001 ] PowerShell – PowerShell was used to decode content and gather system details (‘powershell.exe -windowstyle hidden certutil -decode’).
- [T1140 ] Deobfuscate/Decode Files or Information – Base64, RC4, ChaCha20, and XOR were used to decode or decrypt payloads (‘Base64-decoded and then decrypted using RC4’).
- [T1105 ] Ingress Tool Transfer – Payloads and tools such as VSCode CLI and DWAgent were downloaded from remote servers (‘downloads a legitimate Visual Studio Code (VSCode) CLI onto the infected device’).
- [T1053.005 ] Scheduled Task – MemLoad created scheduled tasks for persistence (‘schtasks /create /tn /tr “regsvr32 /s “‘).
- [T1547.001 ] Registry Run Keys / Startup Folder – Persistence was established by adding values under Run keys (‘registering itself to the HKCUSoftwareMicrosoftWindowsCurrentVersionRun key’).
- [T1543.003 ] Windows Service – httpMalice created a service named CacheDB for persistence (‘creating a service named CacheDB’).
- [T1218.010 ] Regsvr32 – Multiple droppers and implants executed code through regsvr32 (‘execute the malware using regsvr32.exe’).
- [T1059.003 ] Windows Command Shell – Commands were executed through cmd.exe with redirected output (‘execute the provided command using chcp 65001 > nul & cmd /U /C [command]’).
- [T1106 ] Native API – httpMalice and other implants used Windows-native behaviors and services to run commands and manage persistence (‘If elevated, a service named CacheDB is created’).
- [T1021.005 ] Remote Services: VNC – VSCode tunneling and DWAgent enabled remote interactive access to infected hosts (‘establish covert remote access to the victim’s device’).
- [T1090 ] Proxy – Cloudflare Quick Tunnels, VSCode Tunneling, and Ngrok were used to conceal infrastructure (‘actively leverage tunneling services’).
- [T1071.001 ] Web Protocols – C2 traffic used HTTP/HTTPS and POST requests (‘communicates with the C2 server over the HTTP protocol’).
- [T1005 ] Data from Local System – AppleSeed collected documents, screenshots, keystrokes, and USB drive lists (‘gathers sensitive information such as documents, screenshots, keystrokes’).
- [T1057 ] Process Discovery – The malware collected process and execution context details such as current directory and privilege level (‘gathers critical information from the compromised system’).
- [T1082 ] System Information Discovery – Host profiling included MAC address, computer name, volume serial number, IP address, and token status (‘collecting device information, such as the MAC address, computer name’).
- [T1113 ] Screen Capture – httpMalice captured screenshots and sent them to C2 (‘Capture the screen’).
- [T1041 ] Exfiltration Over C2 Channel – Stolen data and screenshots were sent back through the command channel (‘Send the captured screenshot’).
- [T1102.001 ] Web Service: Web Service – VSCode tunnel URLs were sent to external services and Slack webhooks (‘sent to a Slack channel via a WebHook’).
Indicators of Compromise
- [File hashes ] Malicious droppers and implants – 995a0a49ae4b244928b3f67e2bfd7a6e, 52f1ff082e981cbdfd1f045c6021c63f, and other hashes including 08160acf08fccecde7b34090db18b32194faed9af49c98a89c8acc55e97276c9
- [File names ] Lure and dropper filenames – security_20260126.scr, 노현정님.pdf.jse, and xipbkmaw.exe
- [Domains ] C2 and tunneling infrastructure – female-disorder-beta-metropolitan.trycloudflare[.]com, file.bigcloud.n-e[.]kr, and opedromos1.r-e[.]kr
- [Domains ] Additional C2 endpoints – hxxps://www.yespp.co[.]kr/common/include/code/out[.]php, hxxp://newjo-imd[.]com/common/include/library/default.php, and hxxps://www.pyrotech.co[.]kr/common/include/tech/default.php
- [Files ] Payloads and staging artifacts – c:programdataconfig.db, jhsakqvv.dat, and 1.zip
- [Registry keys ] Persistence locations – HKCUSoftwareMicrosoftWindowsCurrentVersionRun, HKCUSoftwareMicrosoftWindowsCurrentVersionRunvalue names like tdll and Everything 1.9a-[filesize]
- [Certificates ] Stolen legitimate certificates were used to evade detection – South Korean organization certificates were referenced as reused signing material
Read more: https://securelist.com/kimsuky-appleseed-pebbledash-campaigns/119785/