The report analyzes DNS, WHOIS, and network IoCs tied to six of 2025’s top ransomware families—Qilin, Akira, Play, INC Ransom, Lynx, and RansomHub—and shows how they connect to domains, IPs, and emails at scale. It also highlights early malicious registration patterns, historical DNS activity, and additional artifacts linked to the broader ransomware ecosystem, including Cl0p, Babuk, SafePay, DragonForce, and Babuk2. #Qilin #Akira #INC_Ransom #RansomHub #Cl0p #Babuk #SafePay #DragonForce #Babuk2
Keypoints
- Six ransomware families from the 2025 top 10 were confirmed in Picus Security’s list: Qilin, Akira, Play, INC Ransom, Lynx, and RansomHub.
- The analysis reduced the dataset to 267 network IoCs, including 28 domains, 236 IP addresses, and 3 email addresses.
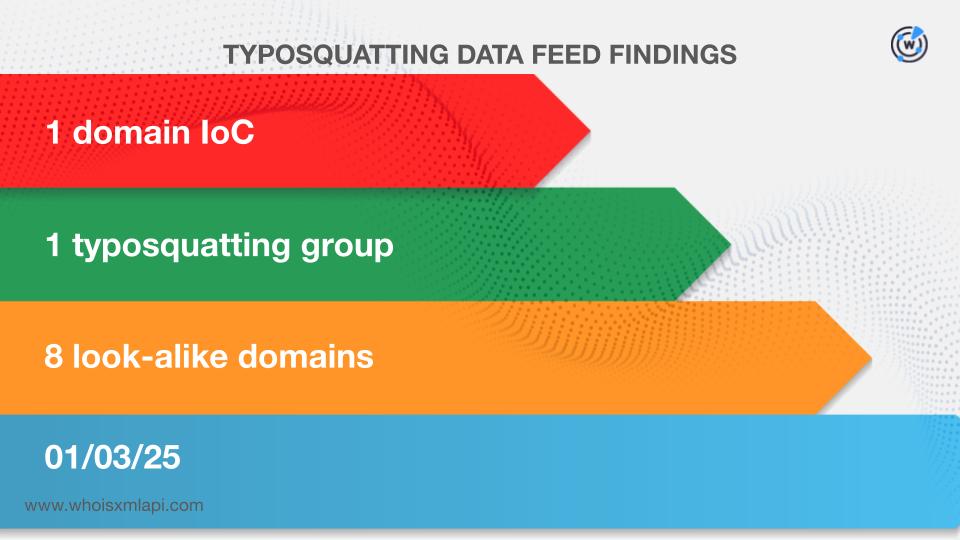
- One domain linked to INC Ransom, simplerwebs[.]world, was bulk-registered with eight look-alike domains.
- Three Akira-related domains were identified as malicious 15–37 days before they were publicly reported as such.
- DNS Chronicle data showed 2,728 historical domain-to-IP resolutions for the 28 domains and 25,643 IP-to-domain resolutions for the IP set.
- Traffic analysis found 2,626 unique potential victim IPs across 166 ASNs communicating with 40 of the IP IoCs.
- Email and WHOIS enrichment produced thousands of additional related artifacts, including 8,491 email-connected domains and 36 malicious ones.
MITRE Techniques
- [T1583.001 ] Acquire Infrastructure: Domains – Threat actors used domains as part of their infrastructure and registration activity, including bulk-registration and look-alike registrations (‘bulk-registered with eight look-alikes’ and ‘three domains… likely registered with malicious intent from the get-go’).
- [T1583.004 ] Acquire Infrastructure: Server – Infrastructure included IP-based assets and hosting endpoints associated with ransomware operations (‘236 IP addresses as IoCs’ and ’40 distinct IP addresses tagged as IoCs’).
- [T1585 ] Establish Accounts – Email artifacts were associated with the ransomware ecosystem, indicating account creation or use for operational purposes (‘three email addresses affiliated with three ransomware’ and ’email-connected domains’).
- [T1595.001 ] Active Scanning: Scanning IP Blocks – Sample traffic showed many potential victim IPs communicating with tagged IPs, consistent with broad infrastructure interaction (‘2,626 unique potential victim IP addresses… communicated with 40 of the IP IoCs’).
- [T1584.001 ] Compromise Infrastructure: Domains – Historical and registered domains were used to support ransomware activity (‘historical WHOIS records’ and ‘DNS Chronicle API queries for the 28 domains’).
Indicators of Compromise
- [Domains ] ransomware-related domains and look-alikes – simplerwebs[.]world, 2rxyt9urhq0bgj[.]org, and other domain IoCs
- [IP Addresses ] tagged network endpoints observed in DNS and traffic analysis – 46[.]161[.]27[.]113, 212[.]83[.]137[.]94, and other 234 IPs
- [Email Addresses ] WHOIS and investigation-related mailboxes – qilin@exxxxxx[.]im, plus 2 other email IoCs
- [Domain-to-IP Resolutions ] historical DNS records linking domains to IPs – in2pay[.]com, pubstorm[.]com, and 2,726 more resolutions
- [IP-to-Domain Resolutions ] historical DNS records linking IPs to domains – 46[.]161[.]27[.]113, 212[.]83[.]137[.]94, and 25,641 more resolutions
- [ASNs ] network origin data for observed victim communication – 166 distinct ASNs associated with 2,626 potential victim IP addresses
Read more: https://circleid.com/posts/a-look-back-at-the-top-10-ransomware-of-2025