The Doppelgänger campaign, linked to the Social Design Agency (SDA) and Structura, uses spoofed media sites, Telegram channels, and coordinated X/Twitter bot clusters to spread pro-Kremlin narratives at scale. Its modular infrastructure supports rapid domain regeneration, disposable accounts, and narrative saturation designed to influence Western audiences and shape public discourse. #Doppelgänger #SocialDesignAgency #Structura #Telegram #XTwitter
Keypoints
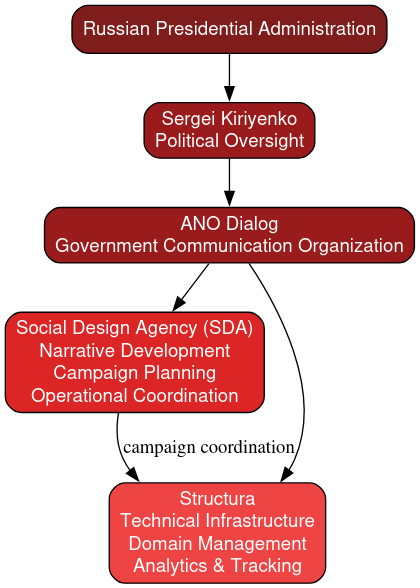
- The Doppelgänger campaign is attributed to Russian-linked actors and associated with SDA and the technical operator Structura.
- It uses a feeder-and-amplifier model: spoofed websites host narratives, Telegram boosts them, and X/Twitter reply swarms inject them into active discussions.
- The operation relies on disposable social media accounts, rapid domain rotation, and reusable website templates to resist disruption.
- Representative infrastructure includes domains such as rrn[.]world, memhouse[.]online, truemaps[.]info, tribunalukraine[.]info, and avisindependent[.]eu.
- Major Telegram amplifiers named in the report include Readovka, SolovievLive, IntelSlava, Ukraina[.]ru, and OstashkoNews.
- Typical narrative waves may expose about 1.5 to 2.7 million users, while larger event-driven campaigns may reach 3 to 5 million users.
- The campaign is designed for narrative saturation and environmental influence rather than direct persuasion.
MITRE Techniques
- [T1583.001] Acquire Infrastructure: Domains – The operators register and administer domains used for pseudo-media websites and can rapidly replace them after disruption (‘replacement domains can appear with rapidity after a disruption event’).
- [T1608.001] Stage Capabilities: Upload Malware / Content? – The campaign stages narrative content on controlled feeder websites before wider distribution (‘controlled domains used to host and disseminate campaign content’).
- [T1036] Masquerading – Websites are designed to resemble legitimate news organizations, and accounts use generic identities to appear authentic (‘mimic legitimate media outlets’, ‘designed to resemble independent media outlets’).
- [T1056.001] Input Capture: Keylogging – Not mentioned.
- [T1090] Proxy – Redirect chains and intermediary links are used to obscure source relationships and route users to final destinations (‘route users through multiple intermediary links’, ‘obscures the relationship between the original distribution platform and the hosting domain’).
- [T1071.001] Web Protocols – Content is distributed through websites and links that move users across web infrastructure (‘links to the feeder websites’).
- [T1095] Non-Application Layer Protocol – Not mentioned.
- [T1114.001] Local Email Collection – Not mentioned.
- [T1584.001] Compromise Infrastructure: Domains – Cybersquatted and cloned domains are used to imitate known media brands (‘cybersquatted sites designed to resemble well-known Western news organizations’).
- [T1587.004] Develop Capabilities: Malware? – The ecosystem appears to use reusable templates and prebuilt deployment packages to regenerate infrastructure (‘shared layouts, visual elements, and backend configurations suggest the use of prebuilt deployment packages’).
- [T1534] Internal Spearphishing – Not mentioned.
- [T1204] User Execution – Audience members are induced to click and follow links from Telegram/X into controlled sites (‘repost links to feeder websites’, ‘insert replies containing links’).
- [T1078] Valid Accounts – The campaign uses coordinated social media accounts and established Telegram channels to amplify content (‘clusters of disposable social media profiles’, ‘established channels within the broader pro-Kremlin Telegram ecosystem’).
- [T1498] Network Denial of Service – Not mentioned.
- [T1219] Remote Access Software – Not mentioned.
Indicators of Compromise
- [Domains ] Controlled feeder and spoofed media sites used to publish narratives – rrn[.]world, memhouse[.]online, and other domains such as truemaps[.]info, tribunalukraine[.]info, avisindependent[.]eu
- [Domains ] Additional known SDA sites from the infrastructure map – militarblatt[.]net, politiquedelombre[.]org, geheimtor[.]com, lesentiers[.]org, and other listed domains
- [Telegram channels ] Major amplification nodes that repost campaign narratives – Readovka, SolovievLive, IntelSlava, Ukraina[.]ru, and OstashkoNews
- [Social media accounts ] Disposable X/Twitter reply-swarm accounts used to inject narratives – newly created low-follower profiles with generic usernames and stock or AI-generated avatars
- [Traffic-management software ] Redirect and tracking infrastructure used for link routing and analytics – Keitaro, and other redirect systems
Read more: https://dti.domaintools.com/research/sda-structura-doppelganger-influence-ops