eSentire TRU analyzed a late-April 2026 phishing campaign that reused the Tycoon 2FA PhaaS kit to deliver OAuth Device Authorization Grant phishing against Microsoft 365 accounts. The operators abused Trustifi, Cloudflare Workers, Microsoft Authentication Broker, and Alibaba Cloud infrastructure to harvest device-code consents and issue tokens tied to #Tycoon2FA #MicrosoftAuthenticationBroker #AS45102 #Trustifi #CloudflareWorkers #Entra
Keypoints
- Tycoon 2FA operators repurposed the same kit codebase after the March 2026 takedown, shifting from credential-relay phishing to OAuth device-code phishing.
- The lure began with a Trustifi click-tracking URL in a fake vendor invoice reminder email and redirected through Cloudflare Workers before reaching the malicious content.
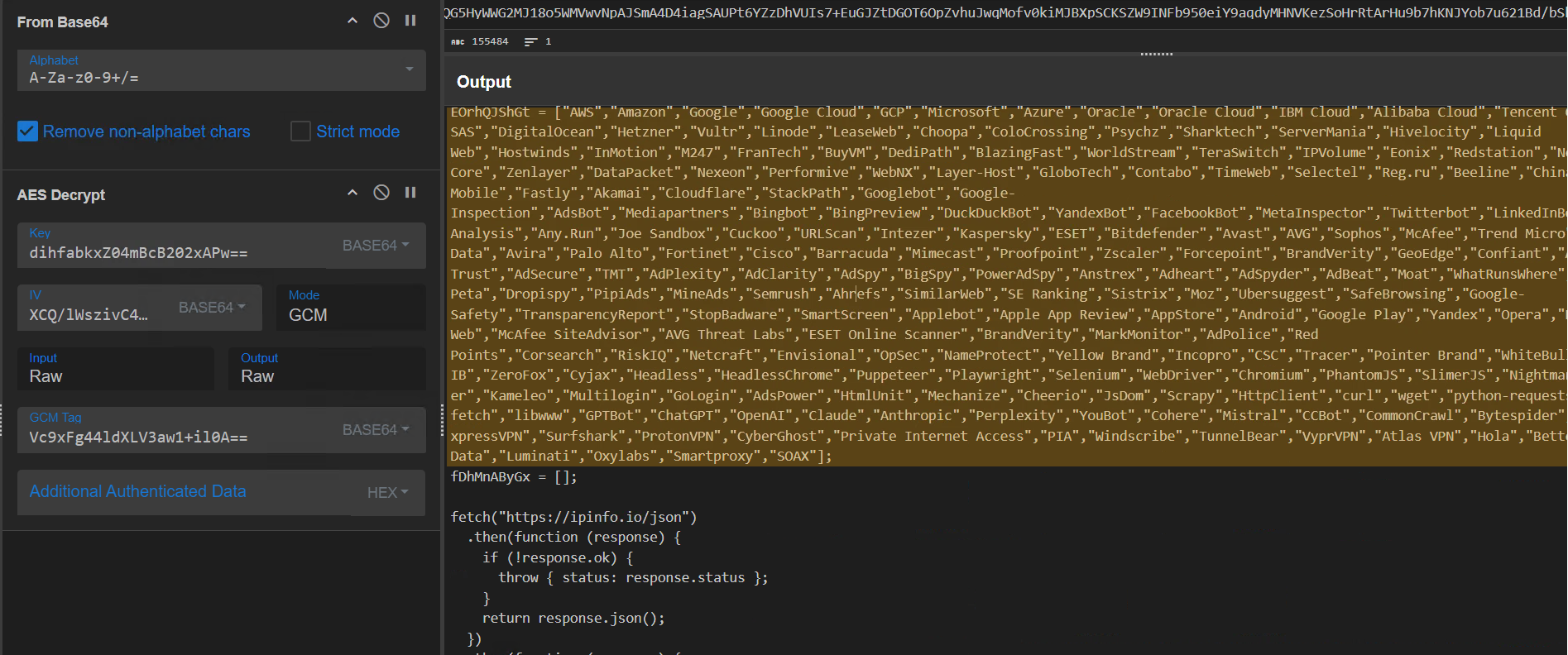
- The kit used layered in-browser delivery, AES encryption, anti-debug checks, headless/browser detection, and ASN-based filtering to evade analysts and sandboxes.
- The phishing flow impersonated Microsoft Authentication Broker and relied on Microsoft’s legitimate device-login and consent process to obtain tokens for Microsoft 365 services.
- Operator-side telemetry showed polling and token activity from AS45102 (Alibaba Cloud) with Node.js user-agent strings such as “node” and “undici”.
- A decoy-on-detection response, NexusCore branding, and a time-bounded expiry date were used to reduce analyst visibility and shorten the sample’s useful window.
- TRU recommended blocking OAuth device-code flows, restricting user consent, enabling CAE, and hunting for suspicious Microsoft Authentication Broker sign-ins and revocation-related events.
MITRE Techniques
- [T1566.002] Phishing: Spearphishing Link – The victim clicked a Trustifi click-tracking URL embedded in an email lure (‘the lure was delivered via a Trustifi click-tracking URL embedded in an email themed as a forwarded vendor invoice reminder’).
- [T1090.001] Internal Proxy – The campaign chained legitimate services and redirects through Trustifi and Cloudflare Workers to launder reputation and deliver payloads (‘Trustifi issues an HTTP 307 redirect to a Cloudflare Workers throwaway subdomain’).
- [T1027] Obfuscated Files or Information – The kit used AES wrapping, Base64/XOR wrapping, and string-fragment reconstruction to hide code and content (‘eval’ and ‘atob’ are reconstructed from .slice() calls; ‘CryptoJS AES-CBC encryption layer’).
- [T1497.001] Virtualization/Sandbox Evasion: System Checks – The script checked navigator.webdriver, callPhantom, _phantom, and Burp user-agent strings to detect automated analysis (‘On any positive result, the page is replaced with about:blank’).
- [T1497.003] Virtualization/Sandbox Evasion: Time Based Evasion – A debugger timing trap measured pauses and redirected if execution was delayed (‘If a debugger is attached, the debugger statement pauses execution’).
- [T1610] Deploy Container – Not applicable; no container activity was described in the article.
- [T1583.001] Acquire Infrastructure: Domains – The operators used multiple domains for delivery and backend control, including the Check Domain and C2 endpoints (‘shivacrio[.]com/bytecore~tx1j8’, ‘fijothi[.]com/…’).
- [T1583.004] Acquire Infrastructure: Server – The backend and polling infrastructure were hosted on external cloud infrastructure, including Alibaba Cloud AS45102 (‘Operator polling activity originated from AS45102 (Alibaba Cloud)’).
- [T1557.003] Adversary-in-the-Middle – The campaign did not use a classic AiTM proxy, but it did abuse a legitimate device-login flow to interpose token issuance (‘The phish does not bypass MFA – it changes what MFA is being used to authorize’).
- [T1528] Steal Application Access Token – The operators obtained OAuth access and refresh tokens after victim consent (‘Microsoft issues access and refresh tokens via /organizations/oauth2/v2.0/token to the device that initiated the device-code grant’).
Indicators of Compromise
- [Domains/URLs ] initial lure and redirection chain – events.trustifi[.]com/api/o/v1/click///…, cookies[.]28gholland[.]workers[.]dev, shivacrio[.]com/bytecore~tx1j8, fijothi[.]com/dhkjCVBfLnfbhFjpYPoDKNMmLIQjNkGLMQPMQUBJFWELKIYHJHWDIESXVUZHHJNFTNMW
- [IP addresses ] operator-side infrastructure and polling activity – 47.90.180.205, 47.252.11.99, and other Alibaba Cloud addresses
- [ASNs ] operator hosting and filtering – AS45102 (Alibaba US Technology Co., Ltd.), plus ASN blocklist entries covering cloud, security, VPN, and AI crawler providers
- [App IDs ] impersonated and related Microsoft OAuth clients – 29d9ed98-a469-4536-ade2-f981bc1d605e (Microsoft Authentication Broker), 4765445b-32c6-49b0-83e6-1d93765276ca (OfficeHome), and 9199bf20-a13f-4107-85dc-02114787ef48 (One Outlook Web)
- [User-Agent strings ] operator automation fingerprints – node, undici, and axios/1.13.x
- [File/route names ] kit routes and backend logic – codeemailtoken, emailtokencookie, emailtoken, checkemailtoken, checkemailtokencookie
- [Tokens/Codes ] session and device-code artifacts observed in backend responses – device_code, user_code, uid, and rotating token values such as 23753b42022ddd08f5c738b54d6c50931b95278d993dd6c4a305a4c0c9ab5e5d
Read more: https://www.esentire.com/blog/tycoon-2fa-operators-adopt-oauth-device-code-phishing