CloudSEK uncovered a large IPL fraud ecosystem involving more than 600 fake ticketing domains and over 400 fake free-streaming sites used to scam fans and deliver malware. The campaigns impersonate trusted platforms, harvest personal and payment data, and deploy the SHub Stealer through malicious streaming redirects that target macOS users. #SHubStealer #BookMyShow #District #IPL #WebCric #Crictime
Keypoints
- CloudSEK identified over 600 fraudulent domains impersonating IPL ticketing platforms to deceive fans.
- More than 400 fake “free streaming” sites were found, many acting as malware delivery channels rather than legitimate stream providers.
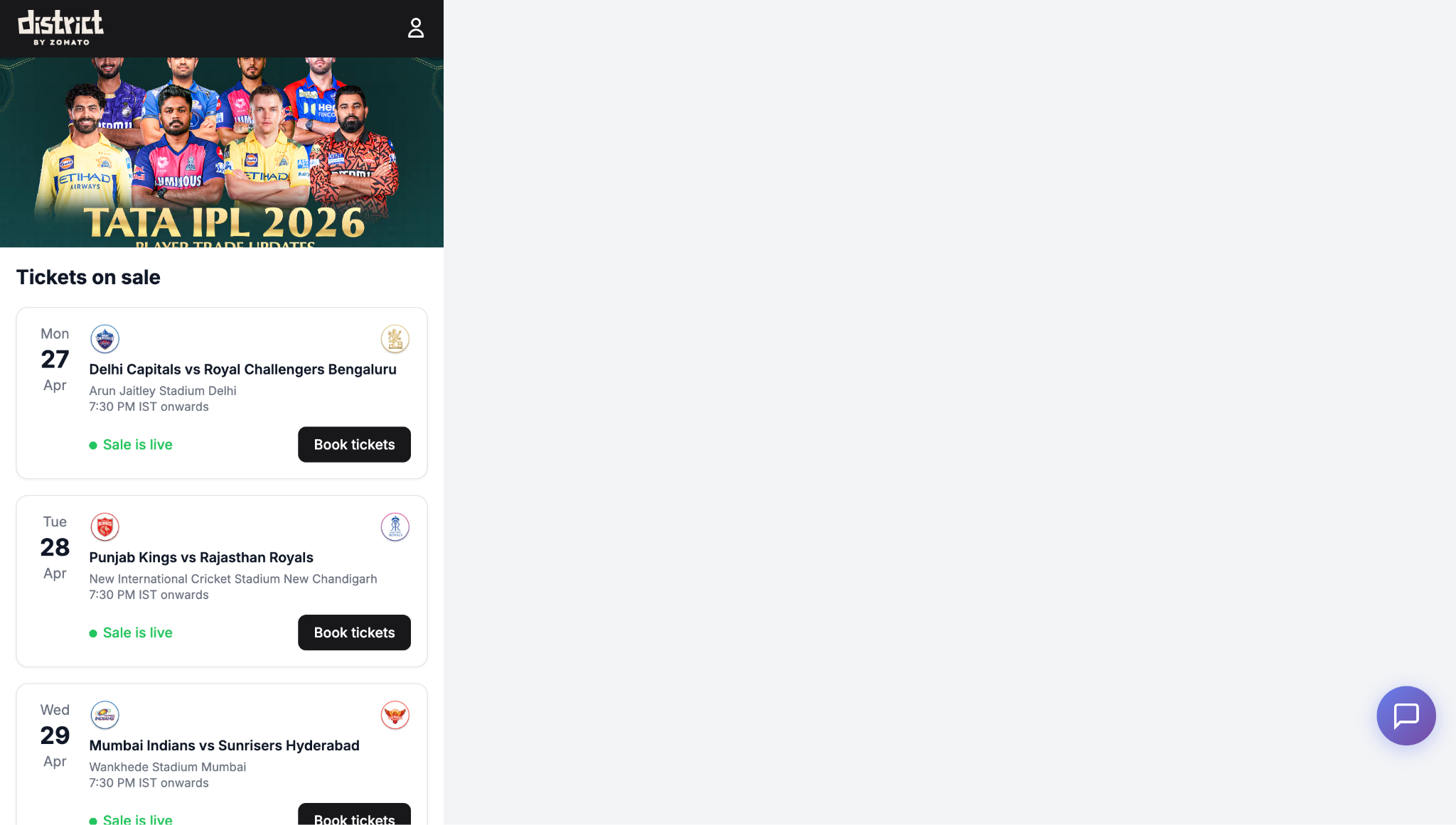
- The fake ticketing sites mimic trusted brands such as BookMyShow and District, using urgency tactics like countdown timers and limited-seat banners.
- An exposed admin panel revealed real-time booking management, manual payment verification, dynamic price controls, and automated fake ticket generation.
- Victim data such as names, phone numbers, and email addresses is collected and may be reused or sold for secondary scams.
- Streaming-related redirects can lead macOS users into ClickFix-style lures that deploy the SHub Stealer infostealer.
- The SHub Stealer targets passwords, browser data, crypto wallets, Telegram sessions, keychains, and other sensitive files while maintaining persistence.
MITRE Techniques
- [T1566.002] Spearphishing Link – Victims are lured through deceptive links in social media posts, ads, and messages that lead to fake ticketing or streaming pages [‘users are pushed through Instagram and Facebook’, ‘posted as helpful “free stream” links’]
- [T1204.001] User Execution: Malicious Link – The attack relies on users clicking buttons, links, or installer pages that start the malicious redirect chain [‘the moment you click anything’, ‘paste the command to complete the installation’]
- [T1059.004] Command and Scripting Interpreter: Unix Shell – A malicious command is pasted into Terminal and piped to zsh to execute the loader [‘paste the command’, ‘retrieved from the C2 and piped directly to zsh for execution’]
- [T1027] Obfuscated Files or Information – The payload is Base64-encoded and Gzip-compressed to hide its purpose before execution [‘Base64-encoded, Gzip-compressed second-stage loader’]
- [T1057] Process Discovery – The malware fingerprints the victim system by checking host and system details before proceeding [‘collecting the hostname, macOS version, external IP address’]
- [T1082] System Information Discovery – The loader gathers device and OS information, including keyboard layout and macOS version [‘collecting the hostname, macOS version, external IP address, and keyboard layout information’]
- [T1016] System Network Configuration Discovery – The malware checks the external IP address as part of environment profiling [‘external IP address’]
- [T1036] Masquerading – The campaign impersonates legitimate brands and system pages, including ticketing sites, GitHub installers, and Apple security updates [‘impersonating District’, ‘impersonating a legitimate GitHub application installer or an Apple macOS security update page’]
- [T1110.001] Brute Force: Password Guessing – The stealer repeatedly prompts for the macOS login password through a fake system dialog [‘asks the user to enter their password up to 10 times’]
- [T1555.001] Credentials from Password Stores – The malware attempts to extract the Chrome master password and access stored credentials [‘tries to extract the Chrome master password’]
- [T1005] Data from Local System – The malware collects browser files, documents, keychains, notes, and other local data [‘copies sensitive files such as Login Data, Cookies, Web Data, History’, ‘steals the entire Keychain directory’]
- [T1185] Browser Session Cookie Theft – It specifically targets cookies from browsers and Safari to hijack sessions [‘Cookies’, ‘Safari cookies’]
- [T1119] Automated Collection – The file grabber automatically collects documents and images from common user folders [‘collects documents … and PNG images from Desktop and Documents folders’]
- [T1560.001] Archive Collected Data: Archive via Utility – Stolen files are compressed into a zip archive before exfiltration [‘The script creates a zip archive’]
- [T1041] Exfiltration Over C2 Channel – Collected data is uploaded to the command-and-control server [‘The archive is uploaded to C2’]
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Persistence is achieved through a LaunchAgent and a fake Google Update service that runs periodically [‘installing a LaunchAgent (com.google.keystone.agent.plist)’, ‘runs every 60 seconds’]
- [T1055] Process Injection – The malware executes the AppleScript in memory with redirected streams to remain hidden [‘executed directly in memory’, ‘all standard input, output, and error streams redirected to /dev/null’]
- [T1090] Proxy: External Proxy – The infrastructure uses ad brokers, redirects, and routing logic to move victims through multiple intermediary domains [‘redirect chain through several shady ad broker domains’]
Indicators of Compromise
- [Domains ] fake IPL ticketing and streaming infrastructure – bookmyshow-ipl-ticket[.]com, ipl2026-ticket[.]online, and 18 more suspicious domains
- [Domains ] unofficial streaming and redirect destinations – go.webcric.com, crictime[.]com, and similar platforms mentioned in the analysis
- [File names ] malicious macOS payload and persistence artifacts – com.google.keystone.agent.plist, /tmp/.c.sh
- [File paths ] temporary storage and collected-data staging – /tmp/shub_/, /tmp/.c.sh
- [File hashes ] obfuscated payloads and second-stage loaders – the article references multiple payload files, including a Base64-encoded loader and a large AppleScript payload, but does not provide hashes
- [Email / PDF artifacts ] fake ticket delivery objects – fraudulent PDF tickets sent by email after payment