This article explains the CISSP security models in Domain 3 as scenario-based tools rather than memorization lists, helping candidates map confidentiality or integrity requirements to the right model on exam day. It highlights Bell-LaPadula, Biba, Clark-Wilson, and Brewer-Nash as the most useful models to recognize quickly, especially by identifying whether the threat is leakage or corruption. #BellLaPadula #Biba #ClarkWilson #BrewerNash #CISSP
Keypoints
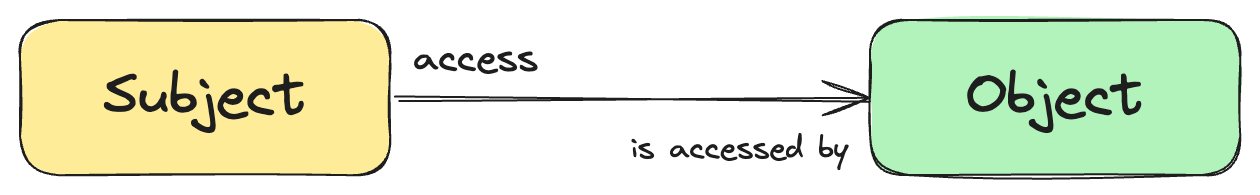
- Security models are formal representations of security policy.
- Bell-LaPadula focuses on confidentiality and prevents information leakage.
- Biba focuses on integrity and prevents bad data from flowing upward.
- Clark-Wilson protects transactions through well-formed procedures.
- Brewer-Nash blocks access to conflicting datasets within the same organization.
Read More: https://www.decodedsecurity.com/p/stop-memorizing-security-models-use