The article analyzes DNS and WHOIS footprints tied to eight Iran-affiliated APT groups, uncovering extensive infrastructure, historical resolutions, and additional artifacts linked to their domains, IPs, and email records. It highlights coordinated impersonation campaigns, maliciously registered domains, and persistent activity across groups such as APT42, APT34, Pioneer Kitten, MuddyWater, and Void Manticore. #APT42 #APT34 #PioneerKitten #MuddyWater #VoidManticore #CyberAv3ngers #BladedFeline #PeachSandstorm #IranAPT
Keypoints
- The investigation focused on eight Iran-affiliated APT groups listed in S2W’s Iran APT Landscape Report.
- The researchers processed 190 network IoCs into 191 unique IoCs, including subdomains, domains, and IP addresses.
- Traffic and DNS analysis linked thousands of client IPs and victim-owned IPs to APT-related domain and IP infrastructure.
- Pioneer Kitten was the only group with subdomain IoCs, and all four subdomains appeared tied to a coordinated impersonation campaign.
- APT42, APT34, and Pioneer Kitten accounted for all domain IoCs found in the article, with many showing historical domain-to-IP resolutions.
- Multiple domain and IP IoCs remained active in 2026, indicating long-lived infrastructure.
- WHOIS history revealed 148 unique email addresses across 121 domains, including 15 public email addresses.
MITRE Techniques
- [T1583.001 ] Acquire Infrastructure: Domains – Domains were registered and used as attacker infrastructure, including bulk-registered look-alikes and maliciously intended domains (‘work-meeting[.]info was bulk-registered with its look-alikes workmeeting[.]info and workmeeting[.]online’).
- [T1583.003 ] Acquire Infrastructure: Virtual Private Server – IP and domain infrastructure was maintained over time through persistent hosting and resolution patterns (‘all were confirmed active malware distributors that shared identical infrastructure fingerprints’).
- [T1584.001 ] Compromise Infrastructure: Domains – Infrastructure was set up to impersonate trusted vendors and blend into enterprise traffic (‘part of a coordinated, multibrand impersonation campaign targeting Sophos and Fortinet, among others’).
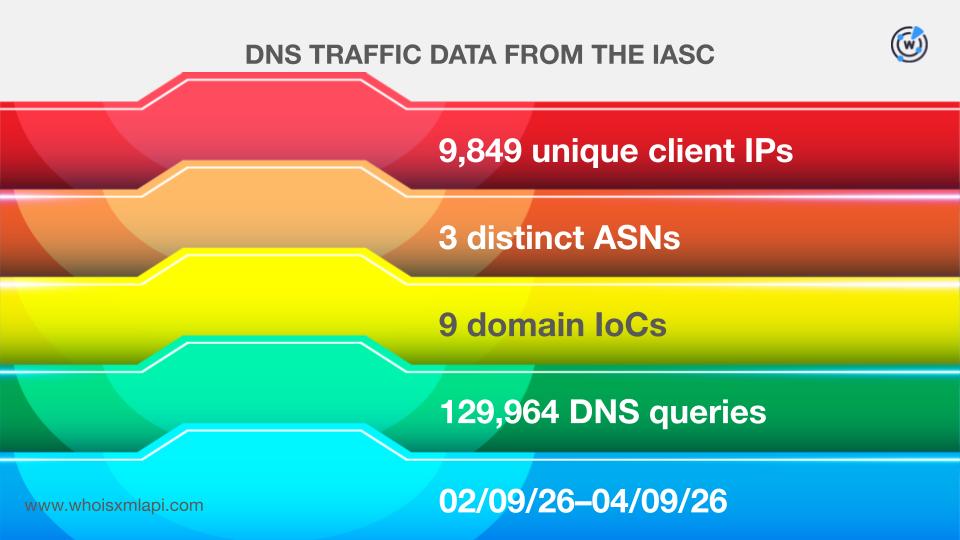
- [T1071.004 ] Application Layer Protocol: DNS – DNS queries and historical domain-to-IP resolutions were central to the observed activity (‘9,849 unique client IP addresses… communicated with nine domain IoCs’ and ‘recorded 5,202 historical domain-to-IP resolutions’).
- [T1588.001 ] Obtain Capabilities: Malware – The subdomains were tied to malware distribution infrastructure (‘all were confirmed active malware distributors’).
- [T1598.003 ] Phishing for Information: Spearphishing Link – The use of look-alike domains and vendor impersonation suggests lure-based access collection (‘chosen to blend in as a legitimate cloud/API service from trusted brand Sophos’).
- [T1565.001 ] Data Manipulation: Stored Data Manipulation – DNS and WHOIS records were used to conceal or alter attribution through infrastructure changes (‘domain extraction from subdomains, legitimate domain filtering, and weeding out of inactive domains’).
Indicators of Compromise
- [Domain ] suspicious and maliciously intended domains – work-meeting[.]info, workmeeting[.]online, and workmeeting[.]info
- [Subdomain ] impersonation infrastructure – cloud[.]sophos[.]one, fortigate[.]forticloud[.]online
- [IP Address ] infrastructure and victim communication – 146[.]19[.]254[.]238, 91[.]132[.]95[.]117, and 2 more IPs
- [Domain ] domains with historical resolutions – backback[.]info, rap-art[.]info, and arrow-click[.]info
- [IP Address ] IPs tied to repeated domain resolutions – 162[.]0[.]230[.]185, 185[.]82[.]73[.]162, and 2 more IPs
- [Email Address ] historical WHOIS contacts – 148 unique email addresses, including 15 public email addresses
- [Domain ] examples of likely malicious registrations – world-shop[.]online, live-meet[.]cloud, top-game[.]online
- [Domain ] APT34 and Pioneer Kitten infrastructure – iqwebservice[.]com, asiacall[.]net, sophos[.]one
Read more: https://circleid.com/posts/a-network-ioc-analysis-for-8-iran-affiliated-apt-groups