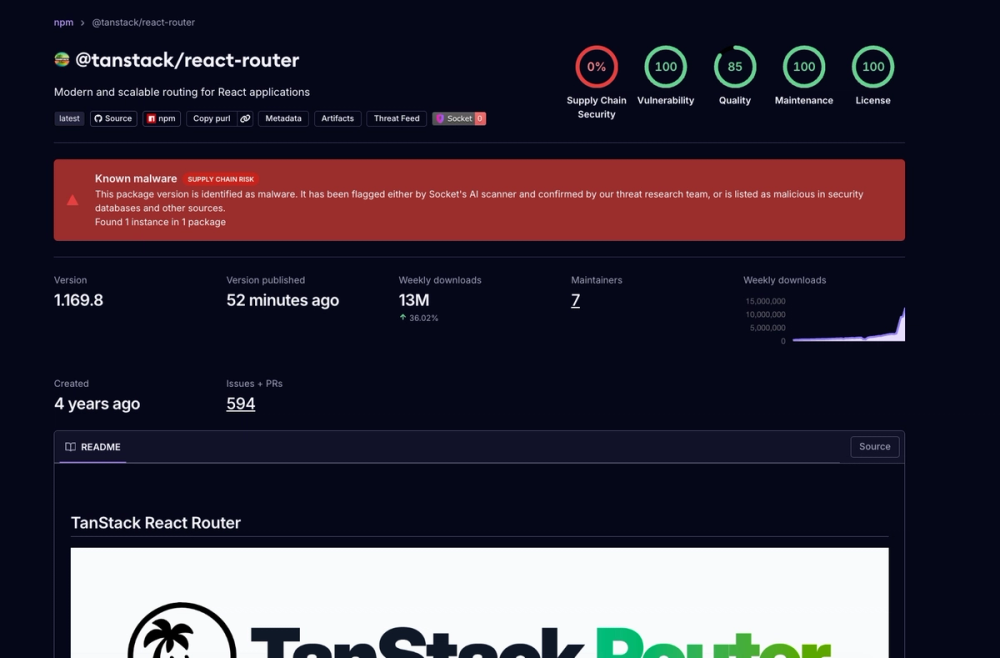
Socket researchers found a compromise in 84 npm package artifacts under the TanStack namespace that inserted a credential-stealing payload targeting GitHub Actions and other CI systems, with some malicious versions reaching more than 12 million weekly downloads. The campaign is tied to the Mini Shai-Hulud supply-chain operation and includes a malicious optional dependency, code execution during installation, and exfiltration over the Session infrastructure. #TanStack #MiniShaiHulud #GitHubActions #Session #npm
Keypoints
- Socket Threat Research detected malicious modifications across 84 npm package artifacts in the tanstack namespace.
- The compromised packages added a suspected credential stealer aimed at CI systems, including GitHub Actions.
- Malicious versions included a newly added router_init.js file with heavy obfuscation and CI secret harvesting logic.
- The payload attempted to access GITHUB* environment variables, AWS credentials, Vault secrets, Kubernetes service account data, and npm tokens.
- The campaign used a suspicious GitHub commit and a malicious prepare lifecycle hook to execute code during package installation.
- Exfiltration was routed through Session infrastructure via filev2.getsession.org, making traffic harder to distinguish from normal encrypted messaging.
- TanStack maintainers began unpublishing affected versions and shutting down publishing pipelines while investigating remediation.
MITRE Techniques
- [T1059.006 ] Command and Scripting Interpreter: JavaScript – The payload is a JavaScript implant executed in Node.js/Bun environments to harvest secrets and propagate itself (‘heavily obfuscated using the javascript-obfuscator pattern’).
- [T1027 ] Obfuscated Files or Information – The malware hides logic with string-array rotation, hex lookups, control-flow flattening, and dead-code injection (‘heavily obfuscated using the javascript-obfuscator pattern’).
- [T1105 ] Ingress Tool Transfer – Malicious code is delivered through compromised npm packages and GitHub-hosted dependencies (‘any downstream installation … will automatically execute tanstack_runner.js’).
- [T1057 ] Process Discovery – The implant checks the runtime and environment to determine whether it is in CI or on a supported OS (‘profiled the execution environment across three dimensions’).
- [T1552.001 ] Unsecured Credentials: Credentials In Files – It searches for secrets in environment variables, config files, and token paths (‘access to GITHUB* environment variables’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – It uses GitHub APIs, npm registry endpoints, and Session file services for command, validation, and exfiltration (‘GET https://api.github.com/…’, ‘https://registry.npmjs.org/-/npm/v1/tokens’).
- [T1539 ] Steal Web Session Cookie – The campaign targets GitHub Actions OIDC and tokens used to authorize publishing workflows (‘steals an npm OIDC token from GitHub Actions CI environments’).
- [T1557.001 ] Adversary-in-the-Middle: LLM or AI Tooling Hook Abuse – The implant persists by writing into Claude Code hooks and VS Code tasks to re-run on tool events (‘.claude/settings.json write is particularly insidious’).
- [T1106 ] Native API – It uses GitHub GraphQL mutations and package publication APIs to modify repositories and publish artifacts (‘createCommitOnBranch’, ‘publishPackage()’).
- [T1021 ] Remote Services – The attacker uses GitHub Actions, npm, Vault, Kubernetes, and AWS service endpoints as remote targets for harvesting and propagation (‘AWS Secrets Manager and SSM Parameter Store are queried across multiple regions’).
- [T1090 ] Proxy: External Remote Services – Exfiltration is routed through the Session decentralized network to mask attacker traffic (‘routes all harvested credentials through the Session decentralized messaging network’).
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – The payload abuses workspace task configuration to trigger execution on folder open (‘.vscode/tasks.json’).
- [T1564.005 ] Hide Artifacts: Hidden Files and Directories – It writes persistence components into hidden developer directories such as .claude and .vscode (‘writes copies of itself into two developer tooling directories’).
Indicators of Compromise
- [File names ] malicious payloads and persistence files –
router_init.js,router_runtime.js, andtanstack_runner.js - [Hashes ] known malicious file hash – SHA256
ab4fcadaec49c03278063dd269ea5eef82d24f2124a8e15d7b90f2fa8601266c, SHA112ed9a3c1f73617aefdb740480695c04405d7b4b - [Hashes ] second malicious payload hash – SHA256
2ec78d556d696e208927cc503d48e4b5eb56b31abc2870c2ed2e98d6be27fc96, SHA1e7d582b98ca80690883175470e96f703ef6dc497 - [Domain / URL ] exfiltration and Session infrastructure –
filev2.getsession.org/file/,api.github.com/repos/ - [IP addresses ] cloud metadata access –
169.254.169.254,169.254.170.2 - [Repository / commit reference ] suspicious GitHub dependency source –
tanstack/router#79ac49eedf774dd4b0cfa308722bc463cfe5885c - [Package names ] affected package family and malicious dependency –
@tanstack/setup,@tanstack/react-router - [Account / author string ] spoofed commit identity –
[email protected]
Read more: https://socket.dev/blog/tanstack-npm-packages-compromised-mini-shai-hulud-supply-chain-attack