SEQRITE Labs uncovered “Operation Silent Rotor,” a spear-phishing campaign targeting the Eurasian unmanned aviation sector with Russian-language lures tied to the Unmanned Aviation 2026 forum in Moscow. The malicious archive delivers a Rust-based executable that fingerprints victims, exfiltrates system data to cdn.kleymarket.ru, and downloads a second-stage payload. #OperationSilentRotor #UnmannedAviation2026 #SOMONTRANSLATIONS #kleymarket.ru #ЦАИ
Keypoints
- The campaign targets professionals and organizations in the Eurasian unmanned aviation sector, with geographic interest spanning Russia, Tajikistan, Central Asia, the Middle East, and Europe.
- The lure material is timed around the Unmanned Aviation 2026 forum in Moscow to increase credibility and victim engagement.
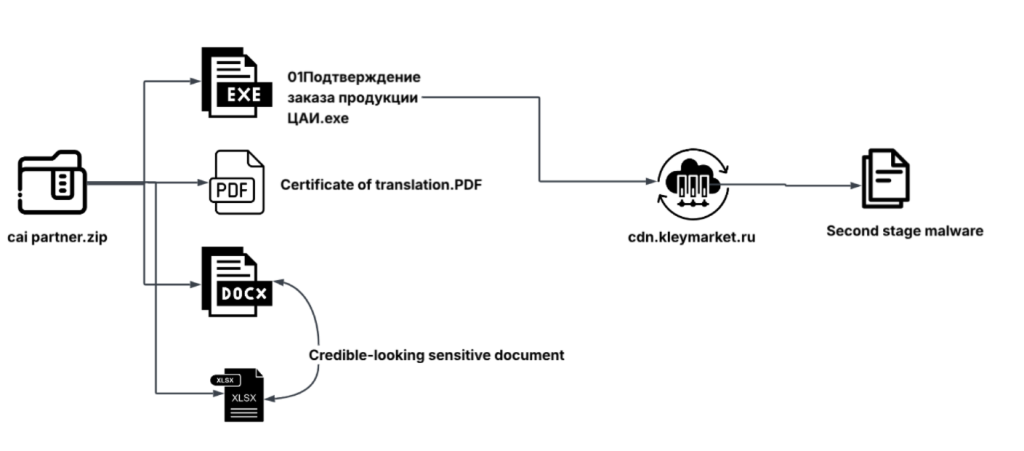
- Attackers distribute a ZIP archive containing a malicious Rust-based Windows executable alongside PDF, DOCX, and XLSX decoy documents.
- The executable displays an embedded decoy document, then collects hostname, volume serial number, usernames, domain data, and network adapter information.
- Victim data is serialized, XOR-encrypted, and exfiltrated over HTTPS to cdn.kleymarket.ru using an HTTP POST request.
- The malware decrypts a second-stage payload from the C2 server, drops it as a randomly named EXE in a user document directory, and launches it.
- The infrastructure centers on the newly registered domain kleymarket.ru and the active IP 45.142.36.76 hosted in Moscow, Russia.
MITRE Techniques
- [T1566.001] Phishing: Spearphishing Attachment – Malicious email attachments were used to deliver the ZIP archive containing the lure files and executable (‘The campaign distributes malicious suspected email attachments through spear phishing’).
- [T1204.002] User Execution: Malicious File – The victim must open the attached archive and run the disguised executable to trigger infection (‘Immediately after execution, this document is displayed on the user’s screen’).
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – The sample is mapped to command execution behavior on Windows during staging and launching of the payload (‘executing it on the victim machine’).
- [T1106] Native API – The malware uses Windows APIs such as GetComputerNameExW, GetVolumeInformationW, NtWriteFile, and CreateProcessA to perform its actions (‘The malware retrieves the machine hostname using GetComputerNameExW’).
- [T1036.004] Masquerading: Match Legitimate Name or Location – The executable and documents are disguised as legitimate CAI/order-confirmation and business files (‘disguised as a legitimate order confirmation document’).
- [T1027] Obfuscated Files or Information – The payload and victim data are encrypted or otherwise obscured using XOR and multi-step decryption (‘encrypts it using a simple XOR method’).
- [T1140] Deobfuscate/Decode Files or Information – The malware decrypts the received payload and extracts it before execution (‘decrypts the payload using AES-256 in blocks’).
- [T1082] System Information Discovery – The malware gathers hostname, volume serial, and other system details to profile the victim (‘collecting system information to build a unique victim profile’).
- [T1016] System Network Configuration Discovery – It enumerates adapters and network addresses to learn the victim’s network environment (‘scans all network adapters using GetAdaptersAddresses’).
- [T1033] System Owner/User Discovery – The malware collects environment variables tied to the logged-in user and domain (‘USER – the currently logged-in username’).
- [T1083] File and Directory Discovery – The malware writes the dropped payload into user document locations and operates on file paths (‘saves the file either in one of these locations’).
- [T1071.001] Application Layer Protocol: Web Protocols – C2 communication and exfiltration occur over HTTPS and HTTP POST (‘sent to the server cdn.kleymarket.ru over HTTPS’).
- [T1090.001] Proxy: Internal Proxy – The use of an intermediary network path is indicated by the mapped proxy-related behavior in the infrastructure and ATT&CK mapping (‘Proxy: Internal Proxy’).
- [T1041] Exfiltration Over C2 Channel – Victim data is sent to the C2 server as JSON over the same channel used for command and control (‘This encrypted data is then sent to the server’).
- [T1105] Ingress Tool Transfer – The malware downloads a second-stage payload from the server and writes it to disk for execution (‘downloads a second-stage payload for execution’).
Indicators of Compromise
- [SHA-256 hashes] malicious executable and associated archives/documents – 5936f42ffd7fa7896eeae725b60a5d26bbf3e584712671ef5da0138ee5d58f60, fdef9e489f773319f55f92f712d1b7b5447d59a632b8f4173d1b161d3759ad92, and 4 more hashes
- [File names] lure archive and embedded documents – cai partner.zip, cai partner (1).zip, and other 4 items
- [Domain] C2 / download infrastructure – kleymarket.ru, cdn.kleymarket.ru
- [IP addresses] active C2 hosting and passive DNS history – 45.142.36.76, 92.62.113.232, and 89.108.110.154
- [Executable / document names] disguised payload and lure files – Подтверждение заказа продукции ЦАИ.exe, Certificate of translation.PDF, and summary_order_cai_final.xlsx
Read more: https://www.seqrite.com/blog/operation-silent-rotor-rust-malware-unmanned-aviation-sector/