Microsoft researchers observed a large, multi-wave AiTM phishing campaign (April 14–16, 2026) that used realistic internal‑looking emails and PDF attachments to redirect over 35,000 recipients to attacker-controlled sites that proxied authentication and captured tokens to gain immediate account access. Organizations are advised to deploy email protections (Defender for Office 365, ZAP, Safe Links/Attachments), enable network protection and SmartScreen, and adopt phishing-resistant or password-less authentication to mitigate these attacks. #AiTM #MicrosoftDefender
Keypoints
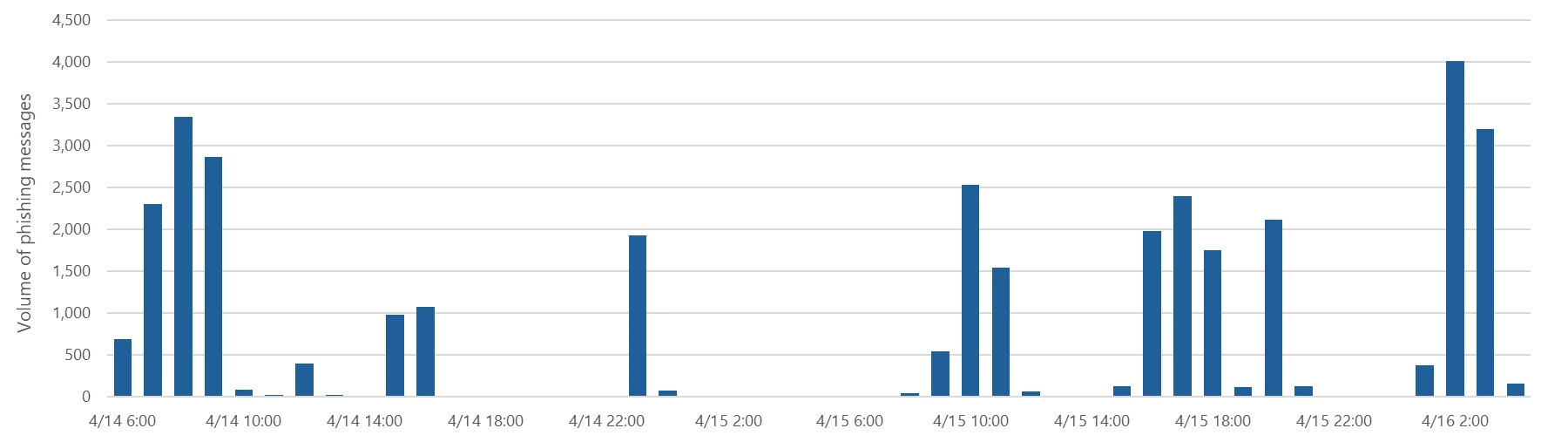
- Between April 14–16, 2026, attackers sent multi-wave phishing messages to more than 35,000 users across 13,000+ organizations in 26 countries, primarily in the United States.
- Emails impersonated internal compliance/regulatory communications and included PDF attachments that directed recipients to attacker-controlled domains hosting CAPTCHA-gated landing pages.
- The campaign used an adversary‑in‑the‑middle (AiTM) authentication proxy flow that intercepted authentication traffic and captured tokens, allowing account takeover despite non-phishing-resistant MFA.
- Attack infrastructure included legitimate-looking sending domains and cloud-hosted virtual machines; attackers used CAPTCHAs to hinder automated analysis and sandboxing.
- Final pages redirected users to a “Sign in with Microsoft” flow that initiated the AiTM session hijack; behavior varied by device (mobile vs desktop).
- Microsoft recommends defenses including Defender for Office 365 settings (ZAP, Safe Links, Safe Attachments), network protection, SmartScreen-enabled browsers, password-less auth, and attack disruption via Defender XDR.
- Microsoft Defender provides detections and hunting queries (email sender filtering, Threat Explorer, advanced hunting) and integrates with Microsoft Security Copilot and Defender XDR for response and investigation.
MITRE Techniques
- [T1566 ] Phishing – Attackers distributed malicious emails and PDF attachments that lured users to credential-harvesting pages (‘phishing campaigns targeting more than 35,000 users’).
- [T1557 ] Adversary-in-the-middle – The campaign proxied authentication sessions to capture tokens and enable immediate account access (‘adversary‑in‑the‑middle (AiTM) phishing flow, which allowed the attackers to proxy the authentication session and capture authentication tokens that could provide immediate account access’).
- [T1078 ] Valid Accounts – Threat actors used stolen valid entities to sign in and maintain persistence (‘Threat actors sign in with stolen valid entities’).
- [T1204 ] User Execution – The flow relied on user interaction with email attachments and links (PDF-contained ‘Review Case Materials’ link) to initiate the compromise (‘Recipients were directed to click a “Review Case Materials” link within the PDF’).
- [T1497 ] Virtualization/Sandbox Evasion – Attackers employed Cloudflare CAPTCHAs as a gating mechanism to impede automated analysis and sandbox detonation (‘This CAPTCHA likely served as a gating mechanism to impede automated analysis and sandbox detonation’).
Indicators of Compromise
- [Domain ] landing and hosting domains used in the campaign – compliance-protectionoutlook[.]de, acceptable-use-policy-calendly[.]de (and other attacker-controlled domains).
- [Domain ] domains used for sender addresses – cocinternal[.]com, gadellinet[.]com (and harteprn[.]com).
- [Email address ] sender addresses used to deliver campaign messages – cocpostmaster[@]cocinternal.com, nationaladmin[@]gadellinet.com.
- [Filename ] PDF attachments containing the phishing link – “Awareness Case Log File – Tuesday 14th, April 2026.pdf”, “Disciplinary Action – Employee Device Handling Case.pdf”.
- [SHA-256 ] file hashes of campaign PDFs – 5DB1ECBBB2C90C51D81BDA138D4300B90EA5EB2885CCE1BD921D692214AECBC6, B5A3346082AC566B4494E6175F1CD9873B64ABE6C902DB49BD4E8088876C9EAD (and 1 more hash).