GitHub fixed a critical vulnerability, CVE-2026-3854, affecting both cloud and on-premises GitHub Enterprise Server that allowed improper handling of git push options. An authenticated user with write permissions could inject delimiter-separated values (e.g., rails_env=nonprod) into internal metadata to achieve server-side command execution; administrators must upgrade affected GHES releases and inspect logs for anomalous push parameters. #CVE-2026-3854 #GitHubEnterpriseServer
Keypoints
- The vulnerability CVE-2026-3854 affects both GitHub cloud infrastructure and on-premises GitHub Enterprise Server due to improper sanitization of push options.
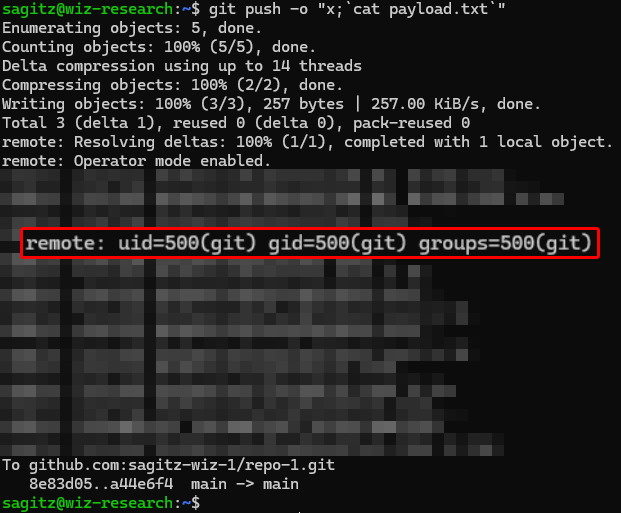
- An attacker can send a git push with crafted push options (for example: git push origin main -o “x;rails_env=nonprod”) that inject a delimiter (;) into internal metadata.
- Internal services that split metadata on ‘;’ can misinterpret injected fields as legitimate configuration, enabling injection of parameters like rails_env=nonprod into server processing.
- The flaw allows an authenticated user with write permissions to obtain server-side command execution with the privileges of the git service user, with command output returned to the client.
- GitHub applied the fix to the cloud environment on 4 March 2026 and publicly disclosed details on 28 April 2026; GHES administrators must upgrade to patched releases.
- Patched GHES releases include 3.14.25, 3.15.20, 3.16.16, 3.17.13, 3.18.7, 3.19.4, and 3.20.0; administrators are advised to update immediately and review logs.
- Recommended mitigation: search /var/log/github-audit.log for pushes containing anomalous push options or unexpected delimiter characters.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – The attacker exploited a parsing bug in GitHub’s handling of client-provided push options to trigger server-side behavior; ‘git push origin main -o “x;rails_env=nonprod”‘
- [T1078 ] Valid Accounts – Exploitation requires an authenticated user with repository write permissions, allowing misuse of legitimate credentials; ‘an authenticated user with write permissions on a repository’
- [T1059 ] Command and Scripting Interpreter – The injected options led to execution of commands on the server under the git service account, with output returned to the client; ‘execution of commands on the server during the push operation, with output returned to the client’
Indicators of Compromise
- [CVE ] vulnerability identifier – CVE-2026-3854
- [Command / Payload ] example malicious push command – git push origin main -o “x;rails_env=nonprod”
- [Header / Metadata ] manipulated internal header example – X-Stat: …;push_option_0=x;rails_env=nonprod;push_option_count=1;…
- [Affected Software Versions ] patched GHES releases to check/upgrade – 3.14.25, 3.20.0, and 5 more versions
- [Log File ] audit log path to inspect for anomalous pushes – /var/log/github-audit.log
Read more: https://cert-agid.gov.it/news/github-e-github-enterprise-server-vulnerabilita-rce-cve-2026-3854/