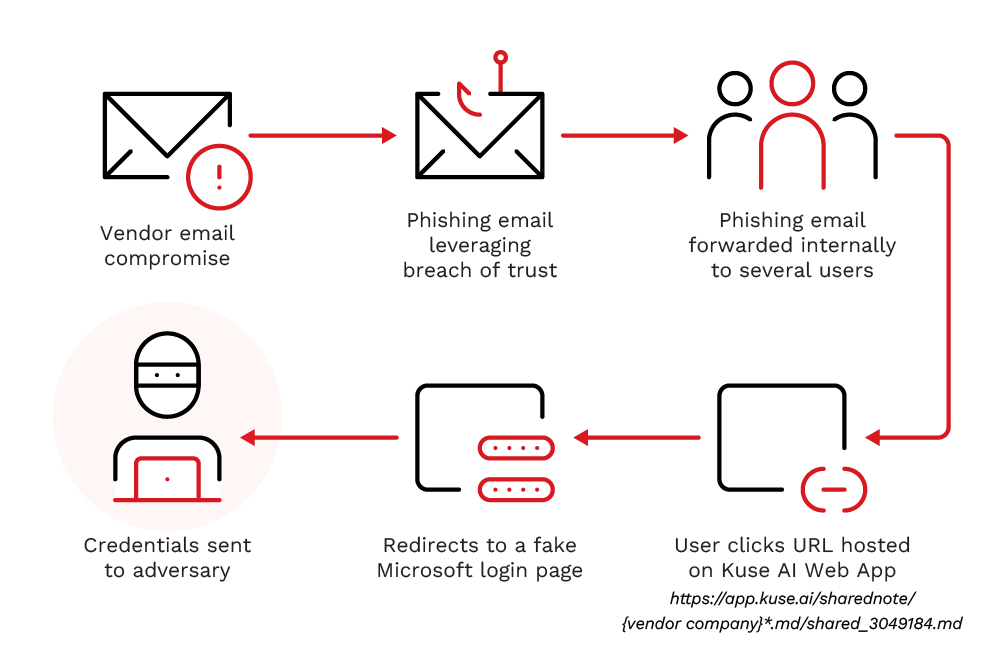
Threat actors abused Kuse.ai’s sharing and storage features and a compromised vendor mailbox to host a blurred Markdown document that redirected recipients to a fake Microsoft login page to harvest credentials. The multi-layered attack combined a Vendor Email Compromise supply-chain tactic with spearphishing links hosted under app.kuse.ai to evade filters and exploit user trust. #KuseAI #Ooraikaoo
Keypoints
- On April 9, 2026, TrendAI detected a phishing campaign that leveraged Kuse.ai’s shareable links to host malicious content.
- Attackers used a compromised vendor mailbox (Vendor Email Compromise) to send trusted-looking emails containing a Kuse-hosted .md link.
- The shared Markdown (.md) file displayed a blurred document preview with a Spanish call-to-action that redirected users to a fake Microsoft login page to harvest credentials.
- Use of the legitimate domain app.kuse.ai and the uncommon .md extension helped the attackers evade automated filters and take advantage of user trust.
- The campaign is categorized as a supply chain-style attack that weaponized platform legitimacy and vendor trust to increase success rates.
- TrendAI recommends enhanced user training, URL scrutiny beyond domains, treating VEC as a persistent threat, enforcing phishing-resistant MFA, and monitoring/restricting AI platform sharing features.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – The campaign leveraged a vendor relationship to deliver the phishing chain via a trusted vendor mailbox: ‘a Supply Chain Attack, particularly a Vendor Email Compromise (VEC)’.
- [T1566.002 ] Phishing: Spearphishing Link – Attackers sent links that redirected users to a hosted .md page and then to a credential-harvesting page: ‘a fake Microsoft login page to collect user credentials’.
- [T1566.003 ] Phishing: Spearphishing via Service – The compromised vendor mailbox was used as the delivery mechanism to exploit existing trust between organizations: ‘a compromised mailbox from a trusted vendor was used to send a specifically crafted phishing email’.
- [T1078 ] Valid Accounts – Threat actors abused a legitimate vendor account/mailbox to send phishing messages and establish trust at delivery: ‘a compromised mailbox from a trusted vendor was used to send a specifically crafted phishing email’.
- [T1204.002 ] User Execution: Malicious Link – The blurred document lure employed a deceptive call-to-action in Spanish that enticed users to click a link: (‘HAZ CLIC AQUÍ PARA VER EL DOCUMENTO’ → ‘CLICK HERE TO VIEW THE DOCUMENT’).
Indicators of Compromise
- [IP Address ] suspected phishing infrastructure – 91.92.41[.]64
- [Domain / URL ] credential harvesting and hosting – hxxps://onlineapp[.]ooraikaoo[.]info/?auth2=8rf22euu-2nxkebabDjjILlzldhQq2Pz, hxxps://app[.]kuse[.]ai/sharednote/%20S.L..md/shared_3049184.md
- [File name / extension ] hosted phishing document – shared_3049184.md, use of the .md Markdown extension to bypass common filters
Read more: https://www.trendmicro.com/en_us/research/26/d/kuse-web-app-abused-to-host-phishing-document.html