WhoisXML API expanded on Cisco Talos’s research into the UAT-8099 campaign, identifying 27 IoCs (10 domains and 17 subdomains), DNS resolution histories, WHOIS history artifacts, and thousands of email-connected domains with several malicious ties. The actor exploited vulnerable IIS servers—using web shells, PowerShell, BadIIS variants, and the GotoHTTP remote-access tool—primarily targeting hosts in Thailand and Vietnam. #UAT-8099 #GotoHTTP
Keypoints
- WhoisXML API expanded Cisco Talos’s original 17 network IoCs to 27 IoCs after apex domain extraction and filtering, comprising 10 domains and 17 subdomains.
- UAT-8099 targeted vulnerable IIS servers in Asia (notably Thailand and Vietnam) deploying web shells, PowerShell scripts, BadIIS variants, and the GotoHTTP tool to gain remote access.
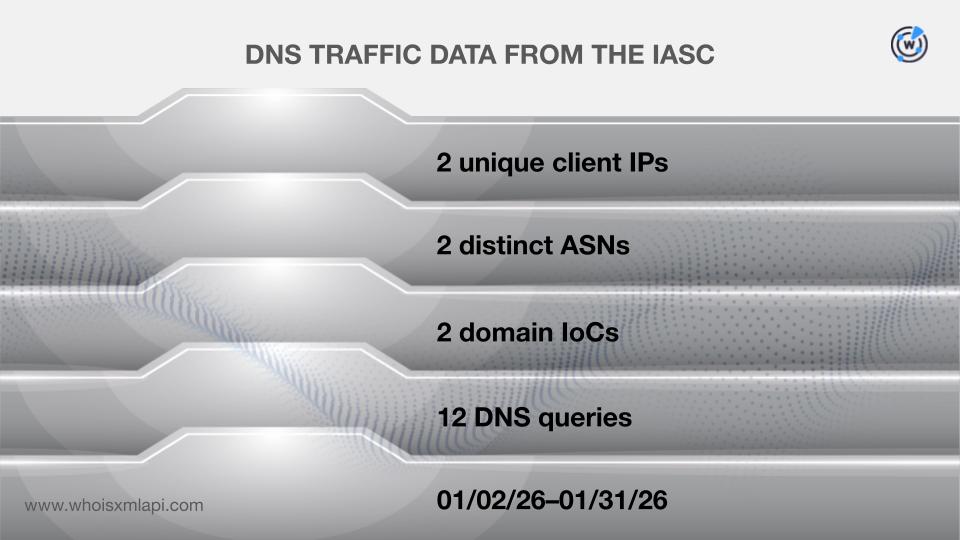
- Analysis found two unique client IPs communicating with two domain IoCs via 12 DNS queries between 2 and 31 January 2026, and seven of the IoC domains had hundreds of historical domain-to-IP resolutions.
- Three domains were flagged as likely to become malicious 545–569 days before being named IoCs (example: gtwql[.]com) and WHOIS history queries revealed eight unique WHOIS emails for three domains.
- Reverse WHOIS and Threat Intelligence queries on public emails uncovered 12,787 email-connected domains (four already weaponized) and 13 resolved IPs (12 previously associated with malicious campaigns).
- Of the 17 subdomains queried, 13 belonged to recently registered domains with several using random-character names and one mimicking Google—indicative of potential phishing infrastructure.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Used to compromise vulnerable IIS servers in the targeted region ( ‘targeted vulnerable IIS servers across Asia specifically focusing on Thailand and Vietnam’ ).
- [T1505.003 ] Web Shell – Deployed web shells on compromised IIS hosts to execute commands and scripts ( ‘They used web shells and PowerShell to execute scripts’ ).
- [T1059.001 ] PowerShell – Leveraged PowerShell to execute scripts and deploy tooling on compromised servers ( ‘They used web shells and PowerShell to execute scripts and deploy the GotoHTTP tool’ ).
- [T1105 ] Ingress Tool Transfer – Transferred and installed the GotoHTTP remote-access tool onto victim IIS servers ( ‘deploy the GotoHTTP tool, granting them remote access to vulnerable IIS servers’ ).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Used HTTP-based communications and web-accessible tooling (GotoHTTP) to provide remote access and control ( ‘deploy the GotoHTTP tool, granting them remote access to vulnerable IIS servers’ ).
- [T1566 ] Phishing – Infrastructure included a subdomain mimicking Google, consistent with phishing-lure usage ( ‘Only one … merited complete avoidance since it seemed to be mimicking Google, typical of sites designed for phishing campaigns.’ ).
- [T1583.001 ] Acquire Infrastructure: Domains – Adversary registered and used domains and subdomains (some newly registered/random) as infrastructure; some domains were likely malicious long before being flagged ( ‘three of the domains tagged as IoCs were deemed likely to turn malicious 545—569 days prior’ ).
- [T1568 ] Dynamic Resolution – Observed extensive domain-to-IP historical resolutions and DNS query activity for IoC domains ( ‘seven recorded 566 domain-to-IP resolutions over time’ ).
Indicators of Compromise
- [Domain ] IoC domains and examples from analysis – gtwql[.]com (identified as likely malicious 569 days before being named an IoC), ceye[.]io, jmfwy[.]com, hunanduodao[.]com, and 6 other domains (10 total).
- [Subdomain ] Subdomain IoCs and context – 17 subdomains analyzed (13 under recently registered domains, several random-character names), including one subdomain mimicking Google used for phishing-like activity.
- [IP Address ] Client and resolved IPs observed – two unique client IPs communicated with IoC domains via DNS queries (specific IPs not disclosed in summary), and seven domains resolved to 13 unique IP addresses (12 of which were previously tied to malicious campaigns).
- [Email addresses ] WHOIS email artifacts – 8 unique WHOIS email addresses found in historical records for three IoC domains (7 were public addresses; specific addresses not listed in the article).
- [Email-connected domains ] Domains linked to WHOIS emails – 12,787 unique email-connected domains discovered after filtering; example domain associated with malware distribution: dmnsg[.]com (and 12,786 others).
- [Tool / Malware Names ] Deployed or observed artifacts – GotoHTTP (remote-access tool), BadIIS variants (region‑hardcoded variants), and web shells were identified as deployed artifacts.
- [String-connected domains ] Additional domain links – 76 string-connected domains identified during analysis (examples not enumerated in the summary).
Read more: https://circleid.com/posts/unearthing-dns-facts-about-uat-8099