Summary: A critical vulnerability (CVE-2024-6500) has been identified in two popular WordPress plugins, exposing over 10,000 websites to potential takeover due to inadequate file handling. Attackers can exploit this flaw to read and delete sensitive files, including the wp-config.php file, leading to severe security implications.
Threat Actor: Malicious actors | malicious actors
Victim: WordPress users | WordPress users
Key Point :
- The vulnerability allows attackers to manipulate the ‘file’ parameter to read and delete any file on the server.
- On Windows servers, attackers can access files outside the WordPress installation directory, while on Linux servers, access is limited to files within the installation.
- Users of the affected plugins are urged to update to the latest patched version or switch to alternative plugins to mitigate risks.
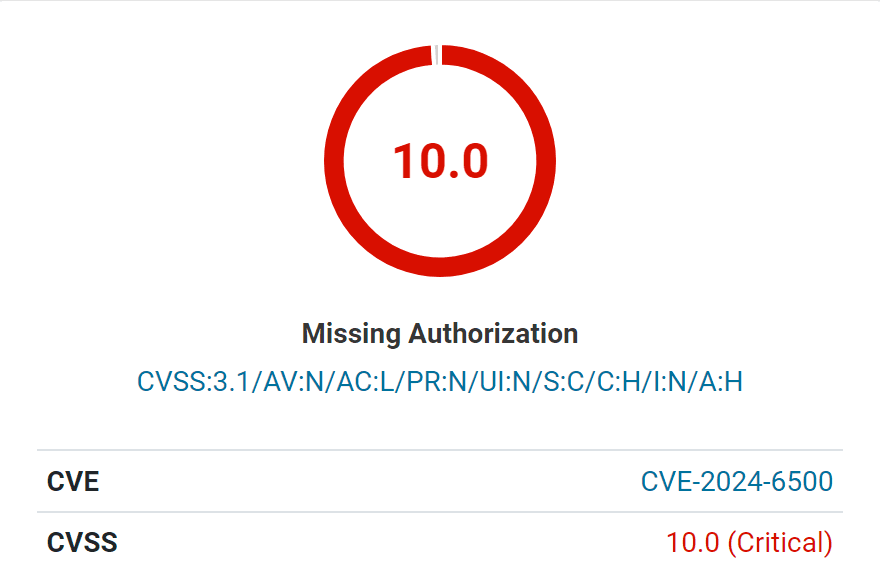
A critical vulnerability, tracked as CVE-2024-6500 (CVSS 10), has been uncovered in two popular WordPress plugins, InPost PL and InPost for WooCommerce, leaving over 10,000 websites susceptible to complete takeover. The flaw, classified as an Arbitrary File Read and Delete vulnerability, could allow attackers to read and delete sensitive files, including the crucial wp-config.php configuration file.
The vulnerability stems from a lack of proper sanitization in the plugins’ file handling procedures. The EasyPack_Helper class within the plugins employs the parse_request() function to download and delete easypack sticker files in PDF format. The ‘file’ parameter used in this process, unfortunately, is not adequately validated, opening a door for attackers to exploit it.
By manipulating the ‘file’ parameter, malicious actors can trick the plugin into reading and subsequently deleting any file on the server, even those outside the WordPress installation directory on Windows servers. On Linux servers, the damage is limited to files within the WordPress install, but they remain vulnerable to unauthorized reading.
The implications of the CVE-2024-6500 vulnerability are severe. By deleting the wp-config.php file, attackers can force the site into a setup state, making it possible to hijack the website by connecting it to a malicious database. Once in control, attackers have complete access to the WordPress instance and can further compromise the system by installing backdoors, modifying files, and maintaining persistent access.
Users of InPost PL are strongly urged to update to the latest patched version, 1.4.5, immediately. The InPost for WooCommerce plugin has been removed from the repository, and users are advised to delete it and switch to the InPost PL plugin instead.
The vulnerability was responsibly disclosed by security researcher ‘1337_Wannabe’ through the Wordfence Bug Bounty Program, earning a $450.00 bounty during the 0-day Threat Hunt Promo.