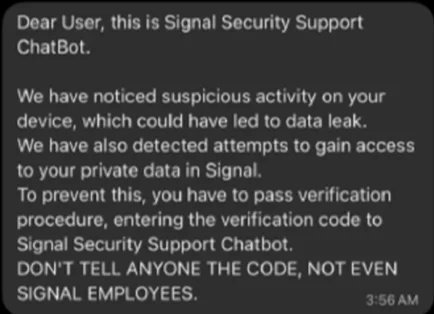
German security authorities warn that a likely state-backed hacking group is using Signal to phish senior politicians, military officials, diplomats, and investigative journalists across Germany and Europe. The alert describes two attack variants—fake Signal support requests for PINs or codes and QR-code prompts that link an attacker’s device—and urges users to block/report fake support accounts, never share PINs, enable registration locks, and review linked devices. #Signal #BSI
Keypoints
- A likely state-backed actor is targeting senior political figures, military officials, diplomats, and investigative journalists via Signal.
- Attackers use two variants: impersonating Signal support to request PINs or one-time codes, and tricking victims into scanning QR codes to link an attacker device.
- Providing a PIN or code lets attackers register the account on their device and take control; scanning a QR code gives silent, ongoing access.
- Compromise exposes private chats, group conversations, and contact lists, enabling network mapping and impersonation for further intelligence or criminal activity.
- Authorities advise blocking and reporting fake support accounts, never sharing PINs, enabling registration locks, regularly reviewing linked devices, and reporting suspected compromises to BfV/BSI.
Read More: https://www.helpnetsecurity.com/2026/02/06/state-linked-phishing-europe-journalists-signal/