*Total Post : 14704 Cybersecurity News (auto update every day)
-
CareCloud Hit by Cyberattack, Probe Into Possible Data Exposure
CareCloud disclosed a March 16 incident in which an unauthorized third party temporarily accessed one of its electronic health record environments, causing a brief operational disruption. The company restored access the same day, engaged external forensic and law enforcement teams, and is still determining whether patient data was accessed or exfiltrated….
-
CISA orders feds to patch actively exploited Citrix flaw by Thursday
CISA ordered U.S. federal agencies to patch Citrix NetScaler appliances by April 2 to address CVE-2026-3055, an actively exploited input-validation flaw that can expose sensitive SAML IDP data. Security firms reported in-the-wild exploitation soon after Citrix released fixes, warning attackers can steal admin session IDs and potentially fully compromise unpatched NetScaler/ADC and Gateway appliances. #CVE-2026-3055 #CitrixNetScaler
-
Healthcare tech firm CareCloud says hackers stole patient data
Healthcare IT firm CareCloud disclosed a March 16 intrusion that compromised one of six electronic health record environments and caused about eight hours of network disruption. The company engaged its cybersecurity carrier and a Big Four incident response team, restored affected systems, and is investigating the scope of exposed patient data. #CareCloud #EHR
-
Critical Citrix NetScaler memory flaw actively exploited in attacks
A critical CVE-2026-3055 vulnerability in Citrix NetScaler ADC and NetScaler Gateway appliances is being actively exploited to extract sensitive authentication and administrative session IDs. Researchers from watchTowr confirmed in-the-wild exploitation starting March 27 and released detection scripts while Citrix’s bulletin did not acknowledge active exploitation. #CVE-2026-3055 #CitrixNetScaler
-
New RoadK1ll WebSocket implant used to pivot on breached networks
RoadK1ll is a newly identified Node.js implant that establishes an outbound WebSocket-based reverse tunnel to convert a compromised host into a relay for lateral movement. Discovered by MDR provider Blackpoint, it forwards TCP traffic on demand using simple commands, supports multiple concurrent connections and reconnection, and lacks traditional persistence. #RoadK1ll #Blackpoint
-
3 SOC Process Fixes That Unlock Tier 1 Productivity
Many SOC delays stem less from the threat itself and more from fragmented workflows, manual triage steps, and limited early visibility that slow Tier 1. Three process fixes—unified cross-platform investigation, behavior-first triage with automated interactivity, and standardized escalation with response-ready evidence—can speed Tier 1, reduce unnecessary escalations, and improve SOC performance….
-
DeepLoad Malware Uses ClickFix and WMI Persistence to Steal Browser Credentials
Researchers found a new campaign that uses the ClickFix social engineering lure to run an undocumented loader called DeepLoad, which leverages AI-assisted obfuscation, in-memory APC injection, and immediate credential theft to evade static detection. DeepLoad hides inside legitimate Windows processes (e.g., LockAppHost.exe), compiles randomized temporary DLLs via Add-Type, uses WMI for…
-
Italian regulator fines financial giant $36 million for data protection failures
Italian regulators fined Intesa Sanpaolo €31.8 million after an investigation found an employee improperly accessed banking information for 3,573 customers between February 2022 and April 2024 and internal controls failed to detect the unauthorized queries. The Italian Data Protection Authority also faulted the bank for delayed and incomplete breach notifications and…
-
Russian court sentences notorious card fraud ringleader ‘Flint’ and 25 associates
A Russian military court sentenced 26 members of the Flint24 carding group, including alleged leader Alexei Stroganov, to prison terms of up to 15 years and fined them up to $57,000 for organizing and trafficking stolen payment card data. Investigators say the network operated from 2014 to March 2020, selling “dumps”…
-
European Commission downplays ShinyHunters cyberattack impact
The European Commission said it contained a cyberattack affecting parts of its public Europa.eu web portal and reported no evidence that its internal systems were compromised. The hacking group ShinyHunters claimed to have stolen more than 350 gigabytes of data, and the Commission is working with experts and authorities to assess…
-
Huskeys Emerges From Stealth With $8 Million in Funding
Israeli startup Huskeys emerged from stealth with $8 million in seed funding to launch an edge security management (ESM) platform that tackles complexities modern environments pose for traditional WAFs. The Tel Aviv company, founded in 2025 by former intelligence veterans Itai Gafni and Roy Weisfeld, provides an agentic control plane that…
-
Silent Drift: How LLMs Are Quietly Breaking Organizational Access Control
Organizations are increasingly using LLMs to generate policy-as-code (in languages like Rego and Cedar) to speed development, but AI-generated policies can be syntactically correct yet semantically flawed and grant unintended access. Research by Vatsal Gupta highlights recurring failure modes—missing contextual restraints, absent deny logic, hallucinated attributes, dropped temporal conditions, and action…
-
Healthcare IT Platform CareCloud Probing Potential Data Breach
CareCloud disclosed a March 16 cybersecurity incident that temporarily disrupted one of its six electronic health record environments and may have resulted in patient information compromise. The company says affected systems have been restored, believes the threat actor no longer has access, and is investigating whether any patient data was accessed…
-
Hackers now exploit critical F5 BIG-IP flaw in attacks, patch now
F5 Networks has reclassified a BIG-IP APM vulnerability from DoS to critical remote code execution (CVE-2025-53521) after discovering attackers are exploiting it to deploy webshells on unpatched devices. F5 and CISA have issued advisories with IOCs and urgent patching guidance while Shadowserver reports over 240,000 BIG-IP instances exposed online. #BIGIPAPM #CVE-2025-53521
-
How to Evaluate AI SOC Agents: 7 Questions Gartner Says You Should Be Asking
Gartner’s report warns that AI SOC agents can reduce alert backlogs and speed investigations, but most organizations will not realize measurable improvements without a structured, outcomes-driven evaluation. The framework outlines seven evaluation categories—outcomes measurement, vendor viability, analyst augmentation, autonomy boundaries, integration, and transparency—and highlights Prophet Security as an example aligned with these principles. #Gartner #ProphetSecurity
-
Apple adds macOS Terminal warning to block ClickFix attacks
Apple’s macOS Tahoe 26.4 introduces a Terminal protection that delays execution of pasted commands and displays a warning to help block ClickFix social‑engineering attacks. The prompt halts execution, reassures users no damage occurred, and advises caution while still allowing users to proceed if they understand the command. #macOSTahoe #ClickFix
-
European Commission Reports Cyber Intrusion and Data Theft
The European Commission confirmed it was targeted in a cyberattack that affected cloud infrastructure hosting its Europa.eu web presence and may have led to the theft of hundreds of gigabytes of data. Hackers claiming to be the ShinyHunters group said they stole mail server dumps, databases and confidential contracts after leveraging…
-
Russian APT Star Blizzard Adopts DarkSword iOS Exploit Kit
Russian state-sponsored hacking group Star Blizzard has adopted the DarkSword iOS exploit kit in an ongoing campaign, using GhostBlade malware to target Apple devices and iCloud accounts. Proofpoint observed a March 26 spike in link-based emails using Atlantic Council lures, and evidence from VirusTotal and URLScan links DarkSword components and a…
-
Hackers Impersonate Ukrainian CERT to Plant a RAT on Government, Hospital Networks
An unknown threat actor cloned the CERT-UA website and sent phishing emails distributing a password‑protected archive that installed AGEWHEEZE, a Go‑based remote access trojan. The campaign—claimed by CyberSerp and using OVH‑hosted WebSocket C2 infrastructure—was largely unsuccessful according to CERT‑UA, which published IOCs and mitigation guidance. #CERT-UA #AGEWHEEZE…
-
Cybersecurity Is a Calling, Not Just a Career — Dr. Priyanka Sunder (PD) on Women Leading the Charge
Dr. Priyanka Sunder is a multi-award-winning cybersecurity strategist and co-founder of CHRIO SecureMojo with two decades of leadership in GRC, cloud security, and enterprise resilience across nine countries. She describes the shift from checkbox compliance to continuous resilience, promotes Security by Design for aligning frameworks like NIST and ISO 27001, and…
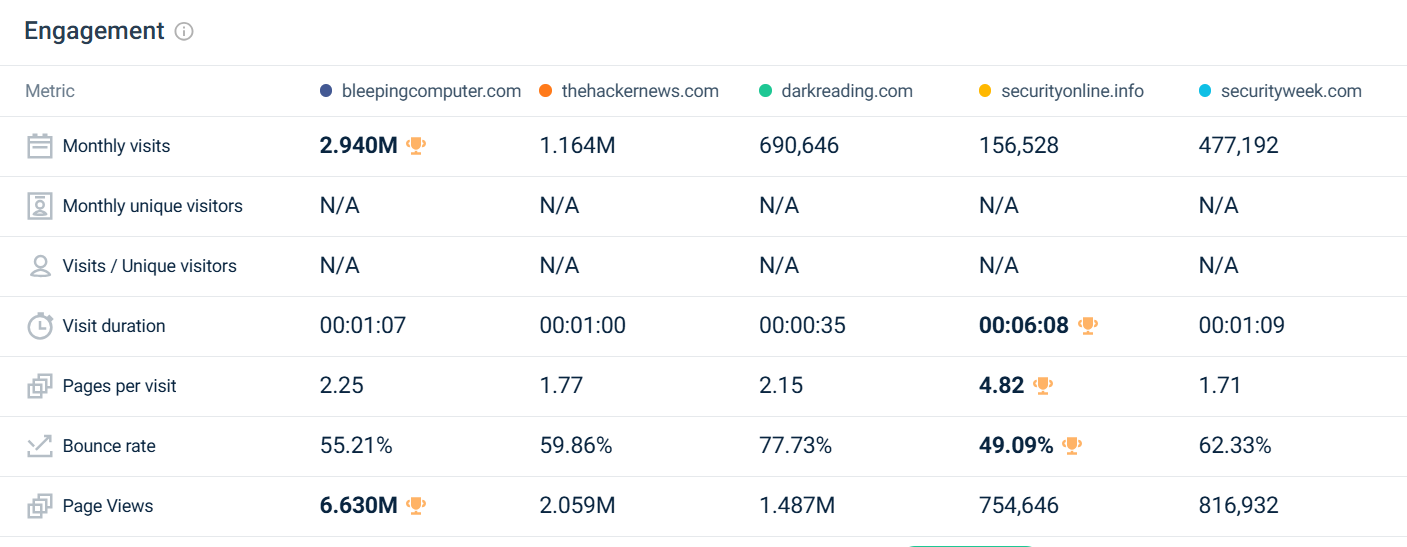
Cybersecurity News Sources
This site will aggregate Cybersecurity News from this sources:
- securityonline.info
- bleepingcomputer.com
- thehackernews.com
- darkreading.com
- + News from Cyware (Currated by Cyware)
- + Latest 100 cyberattacks referenced by Valéry Marchive
- + News from Immuniweb (Cybercrime Investigation and Prosecution)
- + Other hundreds of News Portal
Reference for Security News
Sorted by estimated “Number of Articles” per week. a/w = articles / week.
- malware.news (260 a/w)
- securityboulevard.com (140 a/w)
- ScMagazine.com (70 a/w)
- DarkReading.com (58 a/w)
- BankInfoSecurity.com (48 a/w)
- bleepingcomputer.com (47 a/w)
- CySecurity.news (40 a/w)
- SecurityWeek.com (40 a/w)
- BleepingComputer.com (40 a/w)
- Thecyberexpress.com (34 a/w)
- TheHackerNews.com.com (32 a/w)
- HelpNetSecurity.com (32 a/w)
- PacketStormSecurity.org (30 a/w)
- SecurityAffairs.com (29 a/w)
- Therecord.media (29 a/w)
- TheRegister.com (28 a/w)
- Infosecurity-Magazine.com (26 a/w)
- Securityonline.info (69 a/w)
- Csoonline.com/asean/security/ (19 a/w)
- Hackread.com (19 a/w)
- MalwareBytes.org (14 a/w)
- Cybersecuritydive.com (12 a/w)
- CyberScoop.com (11 a/w)
- Techrepublic.com/topic/security/ (11 a/w)
- ITSecurityGuru.org (9 a/w)
- Zdnet.com/topic/security/ (8 a/w)
- TripWire.com (6 a/w)
- Arstechnica.com/security/ (5 a/w)
- Latesthackingnews.com (5 a/w)
- Asec.ahnlab.com (4 a/w)
- Blog.polyswarm.io (3 a/w)
- Kroll.com/en/ (3 a/w)
- Mandiant.com (2 a/w)
- Bitdefender.com/blog/labs/ (1 a/w)
Check this also :
Update November 2024
“I have launched several social media platforms for updates on Security News”