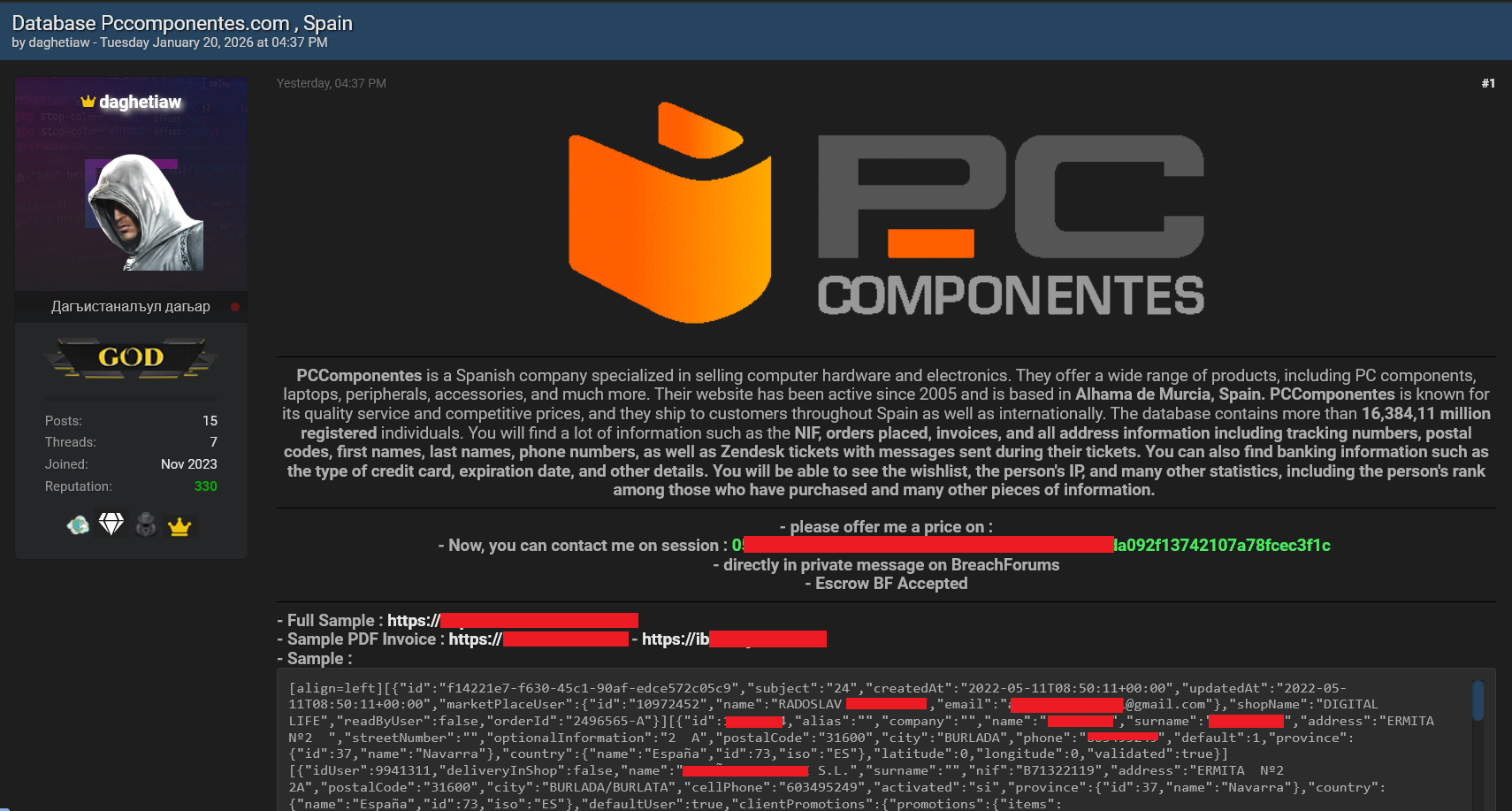
A recent incident involving Pccomponentes demonstrates how threat actors weaponize Infostealer logs to create convincing “fake breaches” that cause significant PR damage. Monitoring and early detection of credential theft from infected devices could have prevented this incident. #InfostealerLogs #CredentialStuffing
Keypoints
- The incident was a case of credential stuffing using compromised credentials from Infostealer logs.
- The attacker did not penetrate Pccomponentes’ servers directly but relied on stolen login data.
- Old infostealer logs from infected devices dating back up to two years were used to find valid credentials.
- Exposure of personal information highlights the importance of proactive Infostealer monitoring for businesses.
- Early detection and credential reset could prevent similar cybercrime tactics and reputation damage.