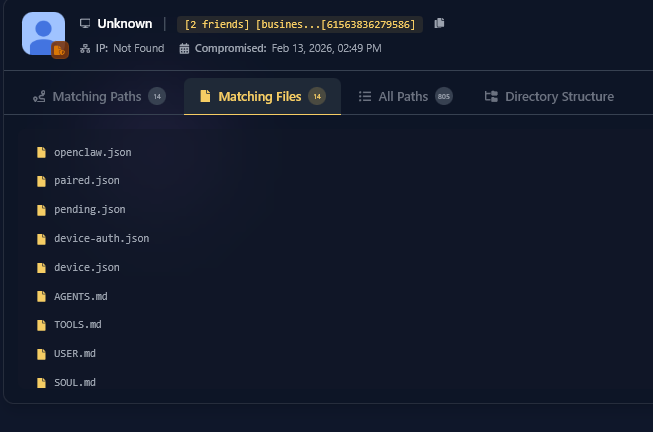
Hudson Rock detected a live ClawdBot infection that exfiltrated an OpenClaw user’s workspace and configuration, demonstrating a shift from stealing browser credentials to harvesting AI agent identities. The attacker obtained openclaw.json, device.json (including a private key), and soul.md/memory files, enabling impersonation, unauthorized access, and a comprehensive view of the victim’s personal context. #ClawdBot #OpenClaw #HudsonRock
Keypoints
- ClawdBot’s infostealer retrieved an OpenClaw workspace using a broad file-grabbing routine rather than a dedicated module.
- openclaw.json exposure revealed gateway tokens and partial user identity that can enable remote or authenticated access.
- device.json theft included the privateKeyPem, allowing attackers to sign messages and impersonate the victim’s device.
- soul.md and memory files disclose the AI agent’s personality and personal context, creating deep privacy and security risks.
- Researchers expect a rise in specialized “AI-stealer” modules designed to decrypt and parse agent files as adoption grows.