Kent District Library has closed all of its branches following a ransomware attack. The library is working with external specialists to investigate the incident and will notify patrons if their personal data were compromised. #KentDistrictLibrary #KDL
Category: Cyber Attack

M3rx is a newly observed ransomware strain with a public leak site, a Tox contact, and a Windows Go-based encryptor tied to multiple claimed victims across the US, Canada, Australia, the UK, and Switzerland. The encryptor uses per-run X25519 ECDH with AES-CTR for file content and AES-GCM to wrap per-file keys, appends a 0x400-byte footer, renames files to random 16-character names with the .8hmlsewu extension, and staging footers can enable narrow recovery opportunities. #M3rx #anvilarts

A threat actor using the handle Spirigatito publicly leaked three datasets from Den kulturelle skolesekken (DKS), exposing 1,389,534 rows of records including performer and user PII, internal county-council messages, and programme planning data. The breach, posted on an open cybercrime forum, creates high risk of targeted social engineering and operational disruption…

A threat actor known as Spirigatito has leaked the customer database of LCBO (Liquor Control Board of Ontario), exposing 165,840 customer records containing account IDs, full names, email addresses, phone numbers, and account types. Although the sample lacks payment or address data, the exposed name‑email‑phone combinations tied to verified LCBO accounts…

Medtronic plc announced that an unauthorized third party accessed data from some of its computer systems on April 24, 2026. The company says it immediately contained the incident, engaged external experts to investigate, and has identified no impact to its products, patient safety, or financial operations, nor does it expect a material impact to its business. #Medtronic #ComputerSystems

BlackSexFinder, an adult entertainment and dating platform, has allegedly been compromised in a recent data leak affecting its forum, galleries, adult movies, and online store. The report from Daily Dark Web notes the claims are unverified and recommends caution while the scope and specifics of the exposed data are investigated. #BlackSexFinder…

Murata Manufacturing Co. disclosed an unauthorized intrusion into its IT environment but said its day-to-day operations were not affected. Approximately 73,000 employee records and 15,000 customer or partner records — containing personal and professional information — may have been compromised, and the company is working with authorities and cybersecurity experts to monitor and strengthen defenses. #Murata #DataExposure

Generation Development Group reported a contained cybersecurity incident affecting its subsidiary Generation Life following unauthorized access via a third‑party vendor. The company says the issue was quickly detected and controlled with no evidence of impact to core systems or fraudulent transactions, and regulators including APRA and the ACSC have been notified. #GenerationLife #APRA
The Family Federation for World Peace and Unification (FFWPU) and its Tongil Group affiliates are alleged to have been breached, with a dark web post offering extensive internal databases and personal records for sale. The seller claims the data was exfiltrated between January and March 2026 via an IDOR vulnerability and…
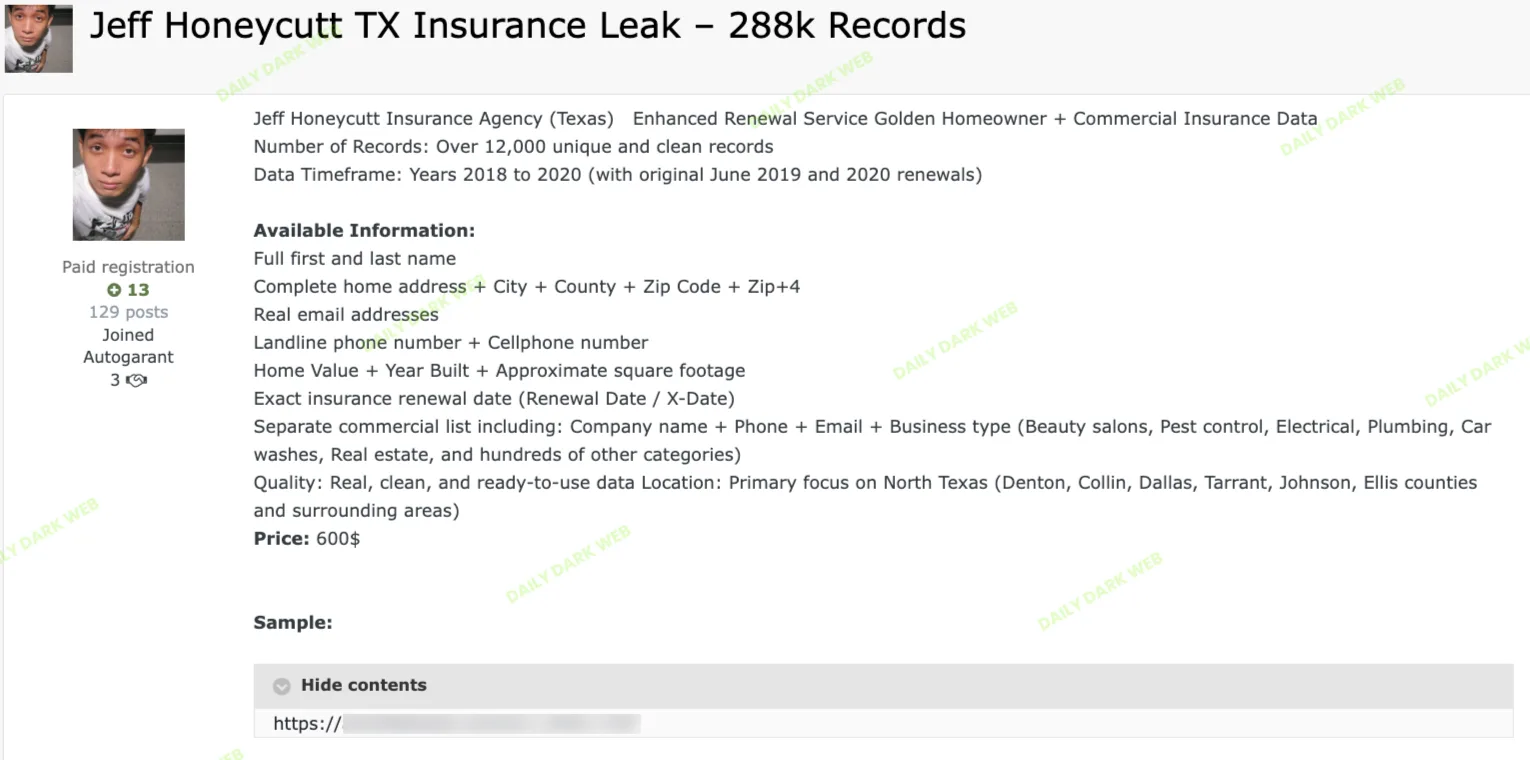
Jeff Honeycutt Insurance Agency, a Texas-based provider, was allegedly breached, resulting in the unauthorized extraction and sale of sensitive client records. The actor claims over 12,000 unique records were taken from a larger 288,000-record dataset covering 2018–2020 and affecting homeowner and commercial clients across North Texas counties. #JeffHoneycuttInsurance #NorthTexas…

Generation Development Group’s subsidiary Generation Life Limited quickly contained a cyber incident detected in a limited part of its network via a third‑party provider, with no evidence of unauthorised transactions or impact on core systems. The company has engaged leading cyber security experts, notified regulators including APRA, OAIC, ACSC and NOCS, and will update the ASX and any affected advisers or clients after the investigation. #GenerationLife #GenerationDevelopmentGroup
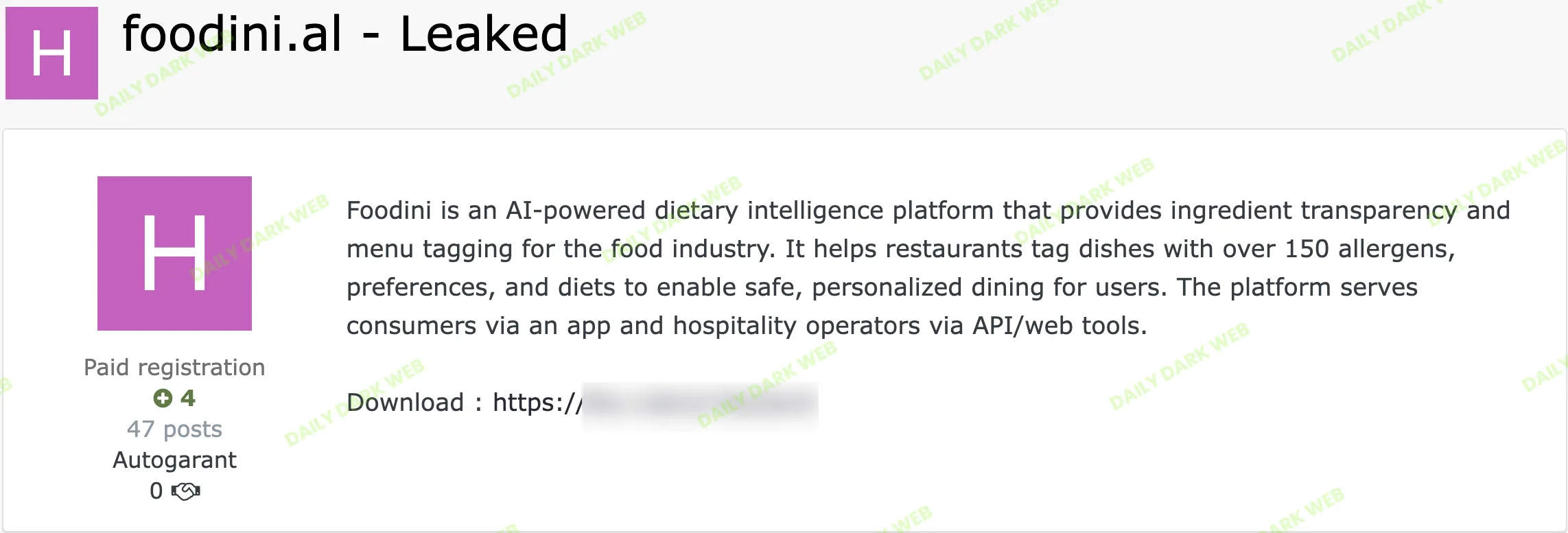
Foodini, an AI-powered dietary intelligence platform that provides ingredient transparency and menu tagging for the food industry, was allegedly breached and had its data leaked online. An unauthorized party reportedly published a compressed archive containing application archives, platform system files, binary data, and internal operational files to a public file-sharing service….

Padanama Publication, Sri Lanka’s largest book printing company, has allegedly suffered a data breach with a comprehensive client database listed for sale on a dark web forum for $50. The leaked sample reportedly contains highly sensitive personal and system data including National Identity Card numbers, one-time passwords (OTP), names, contact details,…
CL-CRI-1116 campaigns combine SSO-style phishing pages with antidetect browsers and residential proxies to harvest credentials. Attackers use vishing from spoofed VoIP/CNAM to capture credentials and TOTPs, bypass MFA, abuse Microsoft Graph API and SaaS search to collect sensitive files, exfiltrate data via APIs or file-sharing services, and pressure victims with seven-figure ransom demands and SWATting. #CL-CRI-1116 #MicrosoftGraphAPI

A threat actor named kittykatkrew posted an exfiltration of the Arkansas State Crime Lab claiming to have stolen court calendars and a full personnel directory via the agency’s public LASSO portal. The leak was distributed as a free .rar download linked from spear.cx and biteblob.com, creating acute risks of witness intimidation,…