Remcos and NetSupport Manager were deployed via a multi-stage infection chain that relied exclusively on Windows built-in utilities (LOLBins) to evade detection and persist. The attack used forfiles, mshta, PowerShell curl and tar, scripting engines, and stealthy registry persistence before Malwarebytes detected and blocked the intrusion. #Remcos #NetSupportManager
Keypoints
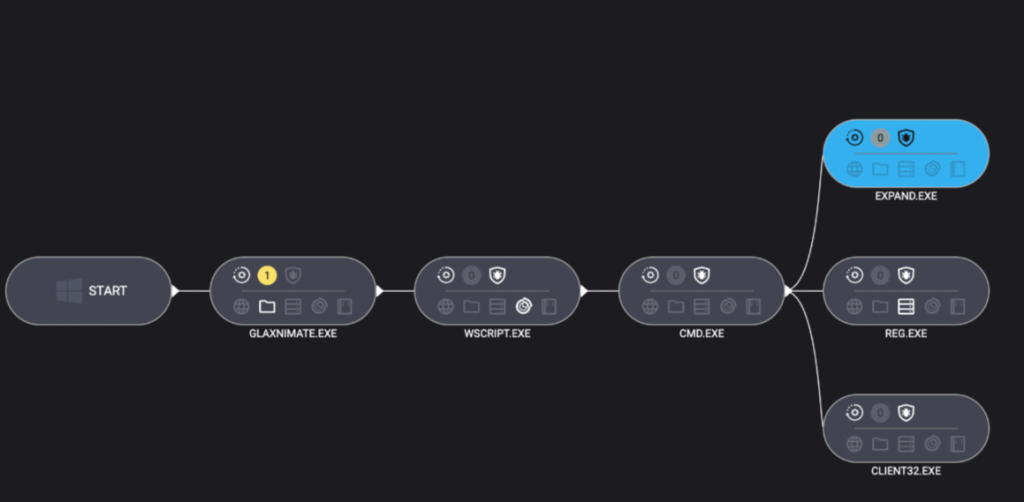
- Attackers abused multiple Windows LOLBins to execute each stage without traditional droppers.
- The initial access used forfiles to stealthily launch mshta, obscuring the execution chain.
- mshta triggered a PowerShell one-liner that downloaded a TAR-disguised payload and extracted a trojanized glaxnimate.exe.
- Staging used .PART files, a VBScript to run a hidden batch, and expand.exe to extract NetSupport components.
- Persistence was achieved via the uncommon UserInitMprLogonScript registry value, and Malwarebytes ultimately detected the Remcos and NetSupport implants and blocked the attacker IP.
Read More: https://www.malwarebytes.com/blog/news/2026/01/can-you-use-too-many-lolbins-to-drop-some-rats