The Fulcrumsec group claims to have breached Analog Gold and its Prospector Portal subsidiary, exfiltrating 2.2 TB of data across 52 S3 buckets that allegedly include the Republic of Guyana’s GGMC IMAPS sovereign mining database. Attackers are using a 58 GB “highlights package” to extort the company amid a pending $28 million asset sale to Exter Gold Corp, with exposed data ranging from personal identifiers and proprietary NI 43-101 reports to ML models, database dumps, and cleartext AWS and Snowflake credentials. #Fulcrumsec #AnalogGold #ProspectorPortal #GGMC #ExterGoldCorp #AWS #SageMaker #Snowflake #Auth0
Keypoints
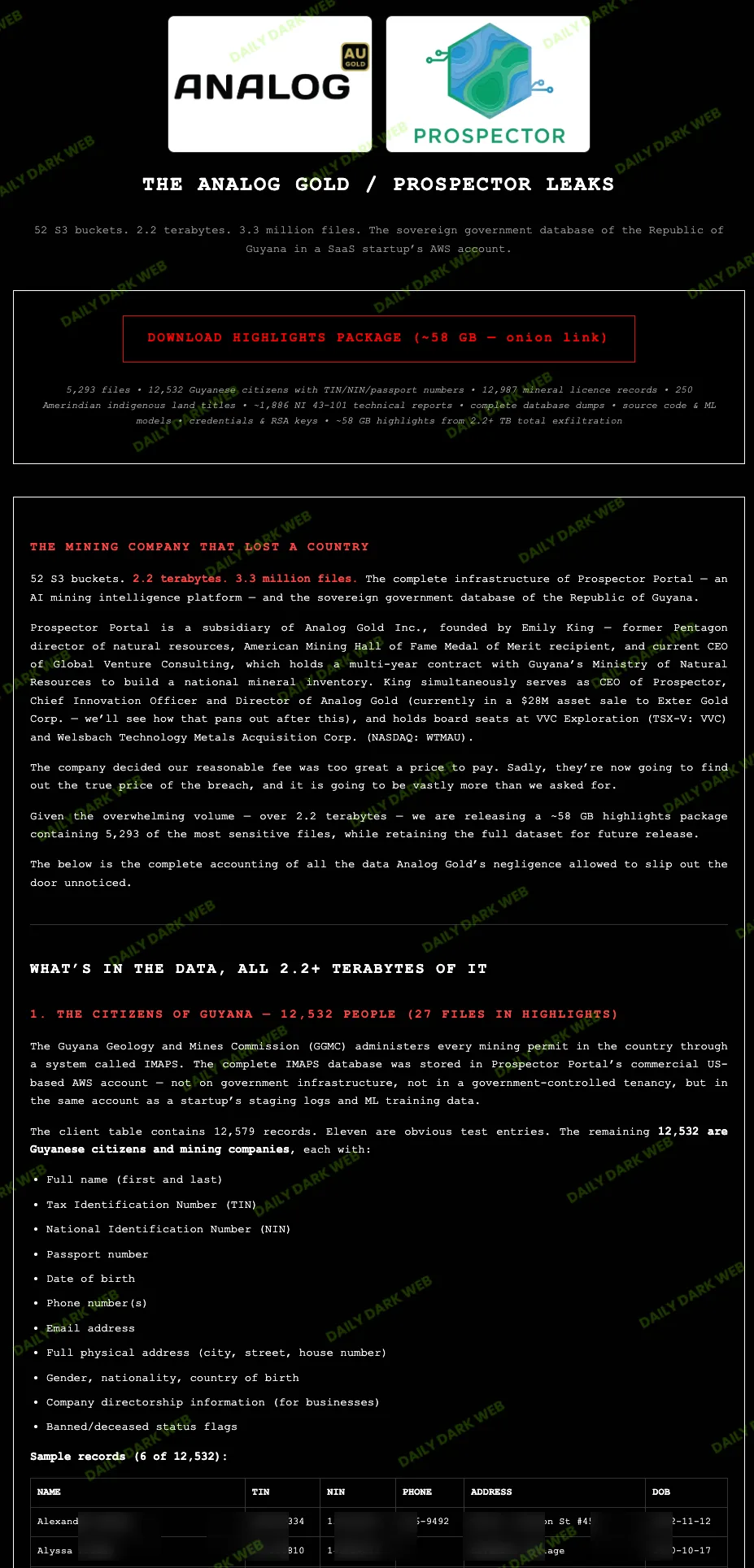
- Fulcrumsec claims a 2.2 TB breach spanning 52 AWS S3 buckets due to infrastructure misconfigurations.
- Exfiltrated personal data reportedly includes full names, TINs, NINs, passport numbers, dates of birth, phone numbers, emails, and full addresses.
- Alleged exposure of GGMC IMAPS government mining data includes 12,987 mineral license records with precise GPS polygons and 41 proposed Amerindian land extensions.
- Proprietary assets said to be compromised include 1,886+ NI 43-101 technical reports, complete MySQL/PostgreSQL/MSSQL dumps, ML models, SageMaker training data, and AI backend source code.
- Cleartext credentials—AWS access keys, Snowflake RSA private keys, Auth0 secrets, and database logins—are reportedly included and are being used to extort Analog Gold during its pending $28M sale to Exter Gold Corp.
Read More: https://dailydarkweb.net/analog-gold-data-breach-by-fulcrumsec-exposes-guyana-records/