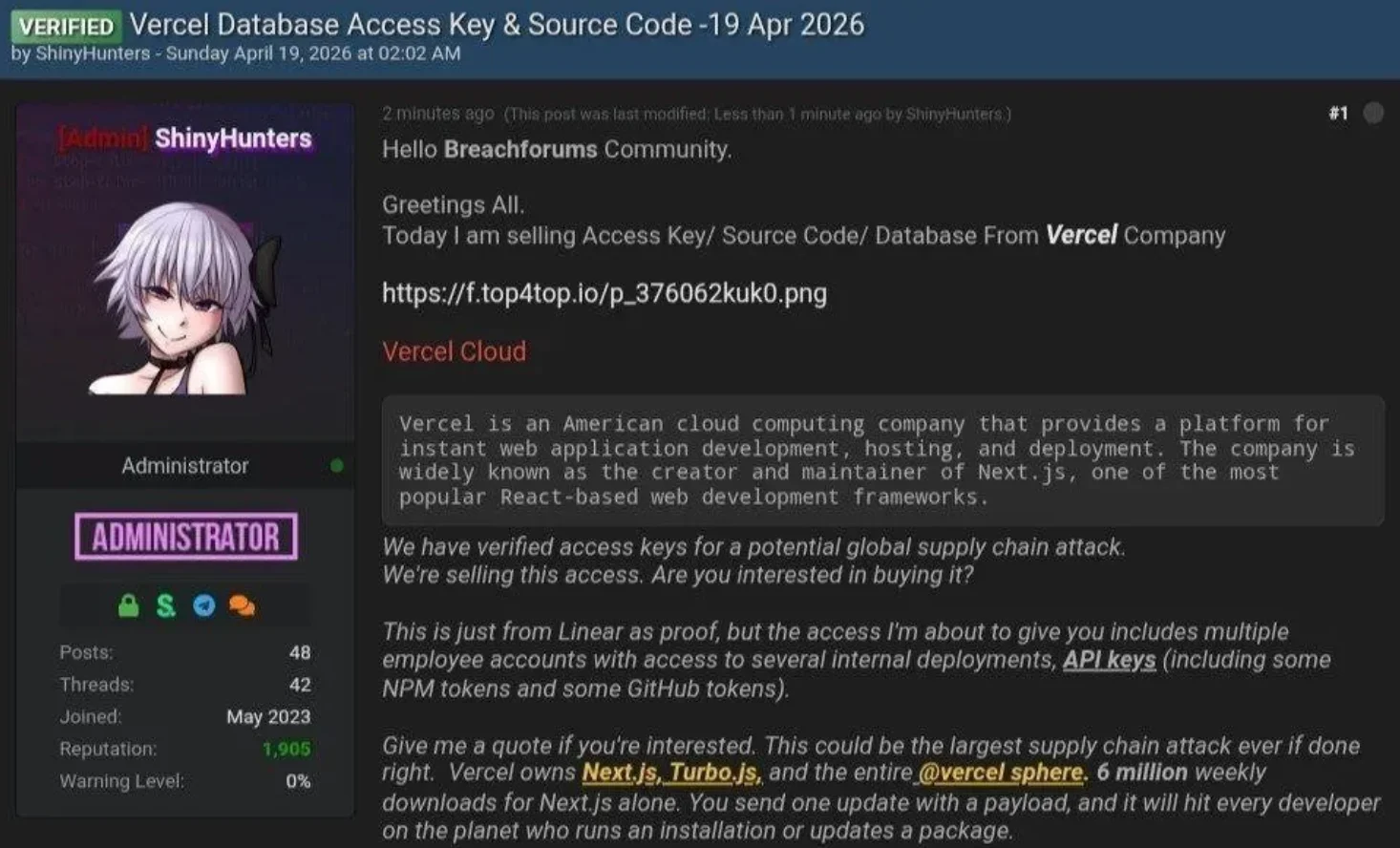
Vercel suffered a security breach after a third-party AI tool compromise (Context.ai) allowed attackers to hijack a Vercel employee’s Google Workspace account and access some internal environments and environment variables. A limited subset of customers had credentials compromised, and Vercel has notified affected users, advised rotating secrets, engaged Google Mandiant and other experts, and deployed additional protections. #Vercel #ContextAI #GoogleWorkspace #ShinyHunters #BreachForums #NextJS #Turbopack
Keypoints
- The breach began when a third-party AI tool (Context.ai) compromise exposed a Google Workspace OAuth token.
- Attackers used that token to take over a Vercel employee’s Google Workspace account and enumerate environments and non-sensitive environment variables.
- A limited subset of Vercel customers had credentials or environment variables compromised and were notified directly.
- Affected customers were advised to rotate credentials and environment variables, rotate Deployment Protection tokens, and review activity logs and deployments for suspicious activity.
- Vercel engaged Google Mandiant and other experts, notified law enforcement, deployed additional protections, and audited its supply chain including Next.js and Turbopack.
Read More: https://www.helpnetsecurity.com/2026/04/20/vercel-breached/