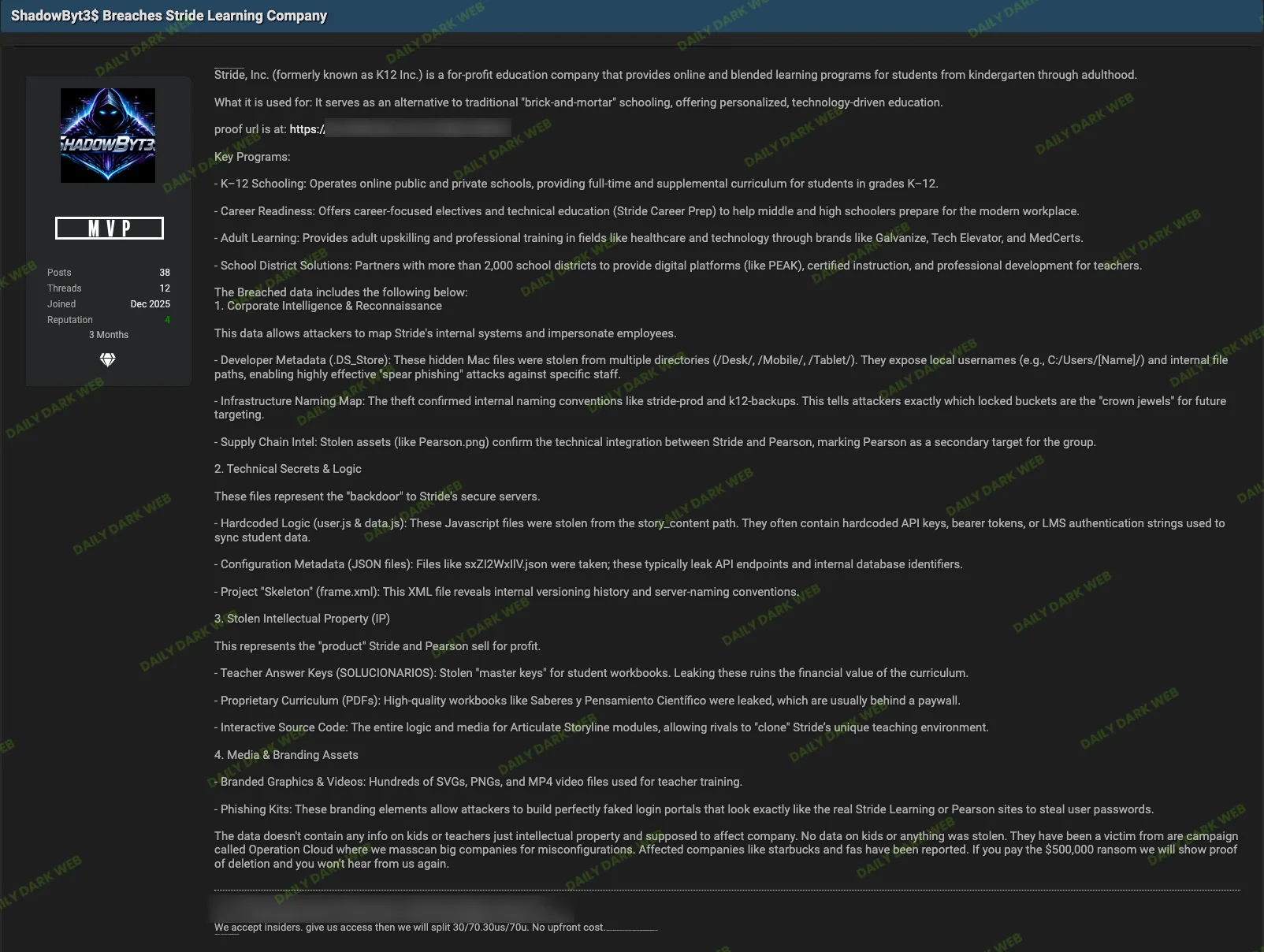
Stride Learning Company was reportedly compromised by threat actor ShadowByt3$ as part of a mass-scanning campaign called “Operation Cloud” that targets misconfigurations in large organizations. The attacker is demanding $500,000 and claims to have exfiltrated corporate assets—including developer metadata, technical secrets, intellectual property, and media/branding assets—while asserting no student or teacher information was taken. #ShadowByt3$ #StrideLearning
Keypoints
- Threat actor ShadowByt3$ allegedly targeted Stride Learning via the Operation Cloud mass-scanning campaign exploiting misconfigurations.
- The attacker is demanding a $500,000 ransom in exchange for proof of data deletion.
- Claimed stolen corporate assets include developer metadata, internal infrastructure naming maps, and supply chain intelligence linking to Pearson.
- Technical secrets alleged to be exposed include hardcoded logic files, configuration JSONs leaking API endpoints, and project “skeleton” XML files.
- Stolen intellectual property and media assets reportedly include teacher answer keys, proprietary curriculum PDFs, interactive source code, branded graphics, training videos, and phishing kits, with the actor insisting no student or teacher data were compromised.
Read More: https://dailydarkweb.net/stride-learning-company-data-extortion-and-breach/