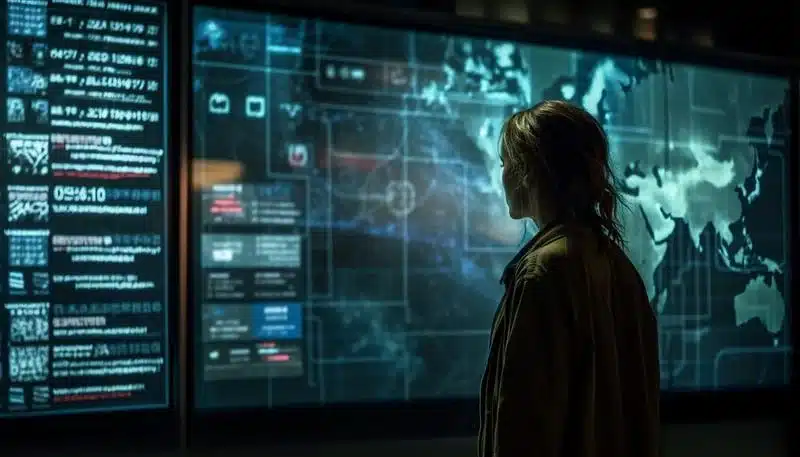
This week’s roundup covers state-sponsored DNS hijacking campaigns, a $285 million exploit of Drift Protocol on Solana, regulatory uncertainty around EU CSAM detection, and findings that deleted Signal data can persist on iPhones. It also highlights the U.S. Treasury’s new Digital Asset Cybersecurity Initiative and a pattern of attackers combining infrastructure compromise, social engineering, and long-term strategic targeting. #APT28 #DriftProtocol
Keypoints
- APT28 exploited vulnerable routers for DNS hijacking and AITM attacks to intercept credentials from targets like Microsoft Outlook.
- Attackers stole $285 million from Drift Protocol in a rapid exploit that drained the Solana-based decentralized exchange.
- The expiration of the EU’s temporary CSAM framework on April 3, 2026, has created legal uncertainty for voluntary scanning techniques such as hash-matching.
- An FBI finding showed deleted Signal messages can remain partially recoverable on iPhones due to iOS notification storage, not Signal encryption failure.
- The U.S. Treasury launched a Digital Asset Cybersecurity Initiative through OCCIP to strengthen defenses across the cryptocurrency ecosystem.
Read More: https://thecyberexpress.com/weekly-roundup-cybersecurity-global-threats/