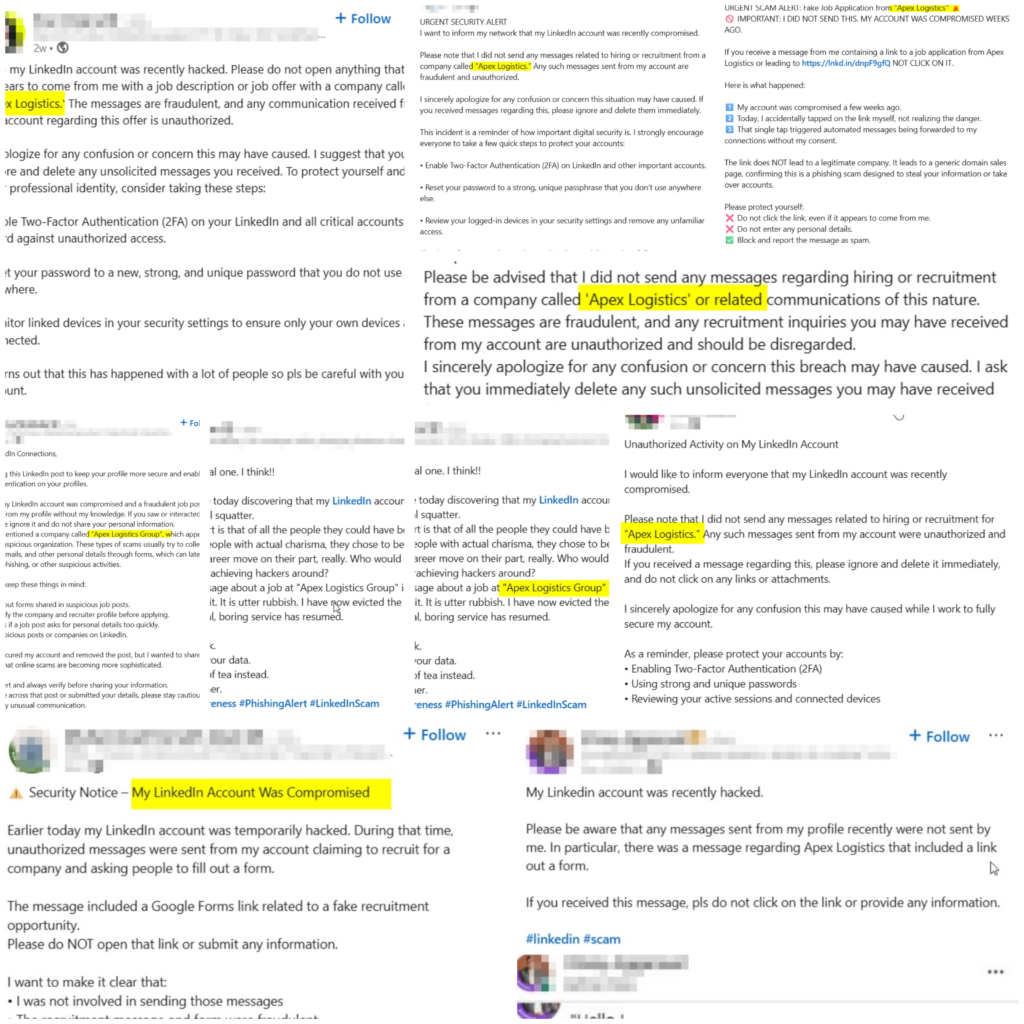
A newly exposed global campaign shows Vietnam‑linked actors using LinkedIn and spoofed recruiter accounts such as Apex Logistics Group to distribute PXA Stealer and siphon credentials, crypto wallet data, and other sensitive information from professionals across multiple countries. The multi‑stage operation leverages Google Forms, URL shorteners, cloud‑hosted ZIPs with oversized DLLs, DLL sideloading and memory‑only execution, and exfiltration over encrypted Telegram channels, enabling large‑scale account compromise and regulatory and reputational risk for victims. #PXAStealer #ApexLogisticsGroup #LinkedIn #Cyble
Keypoints
- Vietnam‑linked actors used compromised or spoofed LinkedIn recruiter accounts to lure job seekers and professionals.
- Targets are asked to complete Google Forms and are redirected to cloud‑hosted ZIPs containing a malicious Word executable.
- The campaign abuses DLL sideloading with oversized binary padding and executes PXA Stealer in memory to evade detection.
- PXA Stealer harvests browser credentials, cookies, crypto wallet identifiers, 2FA secrets, and desktop/email client credentials and exfiltrates via encrypted Telegram channels.
- Researchers estimate over 94,000 infected systems globally, creating risks including account takeover, BEC, regulatory breaches, and reputational harm.
Read More: https://thecyberexpress.com/pxa-stealer-vietnam-linked-actors-linkedin/