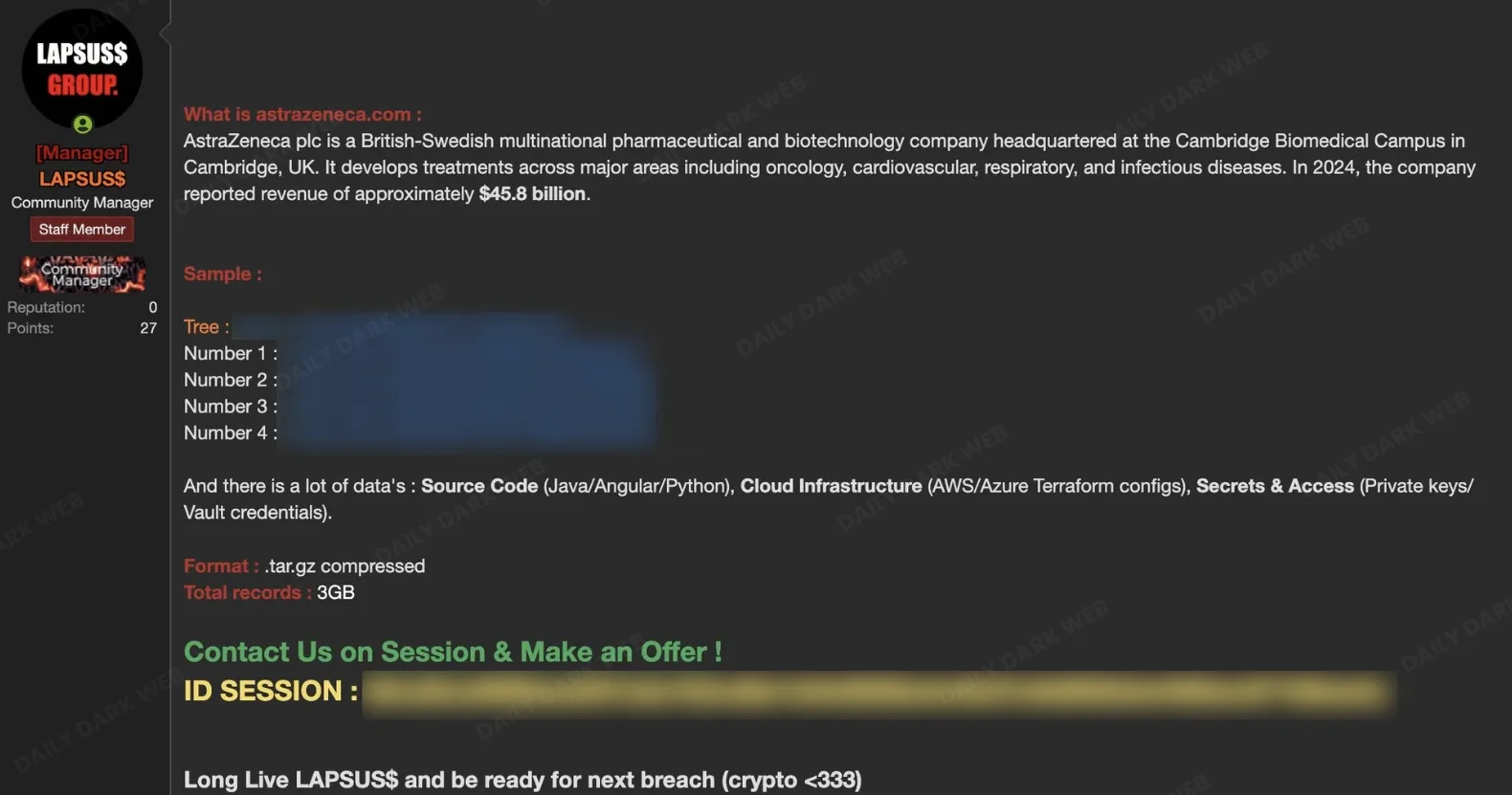
The LAPSUS$ group claims to have breached AstraZeneca and is offering a compressed 3GB internal data dump for sale on illicit forums. Rather than public extortion, the actor appears to be shifting to a pay-to-access model and is instructing potential buyers to negotiate via the Session messaging app; the archive allegedly contains source code, cloud configurations, secrets, and supply-chain data. #LAPSUS$ #AstraZeneca
Keypoints
- LAPSUS$ claims to have accessed AstraZeneca’s internal systems and is selling a 3GB compressed data dump.
- The group is reportedly shifting from public extortion to a pay-to-access sales model and directing buyers to Session.
- Allegedly exposed source code includes Java Spring Boot applications, Angular frontends, and various Python scripts.
- Cloud infrastructure artifacts listed include Terraform configurations for AWS and Azure and Ansible automation roles.
- Sensitive items reportedly include private cryptographic keys, Vault credentials, GitHub and Jenkins tokens, and supply-chain data such as SAP integrations and OTIF metrics.
Read More: https://dailydarkweb.net/astrazeneca-alleged-data-breach-by-lapsus-group/