An infostealer infection on a compromised workstation produced definitive forensic evidence linking a North Korean state‑aligned operator to the Funnull CDN and the Polyfill.io supply‑chain attack while also revealing deep operational ties to transnational organized crime. The recovered telemetry and credentials (including LummaC2 exfiltrated data) show the actor administered weaponized CDN infrastructure, infiltrated Gate.us KYC workflows, exfiltrated NIMS air‑gapped blueprints, and operated an automated Telegram crypto‑laundering gateway. #LummaC2 #Polyfillio
Keypoints
- Forensic evidence from an infected endpoint establishes a direct operational link between a DPRK actor and the Polyfill.io supply‑chain compromise via the Funnull CDN.
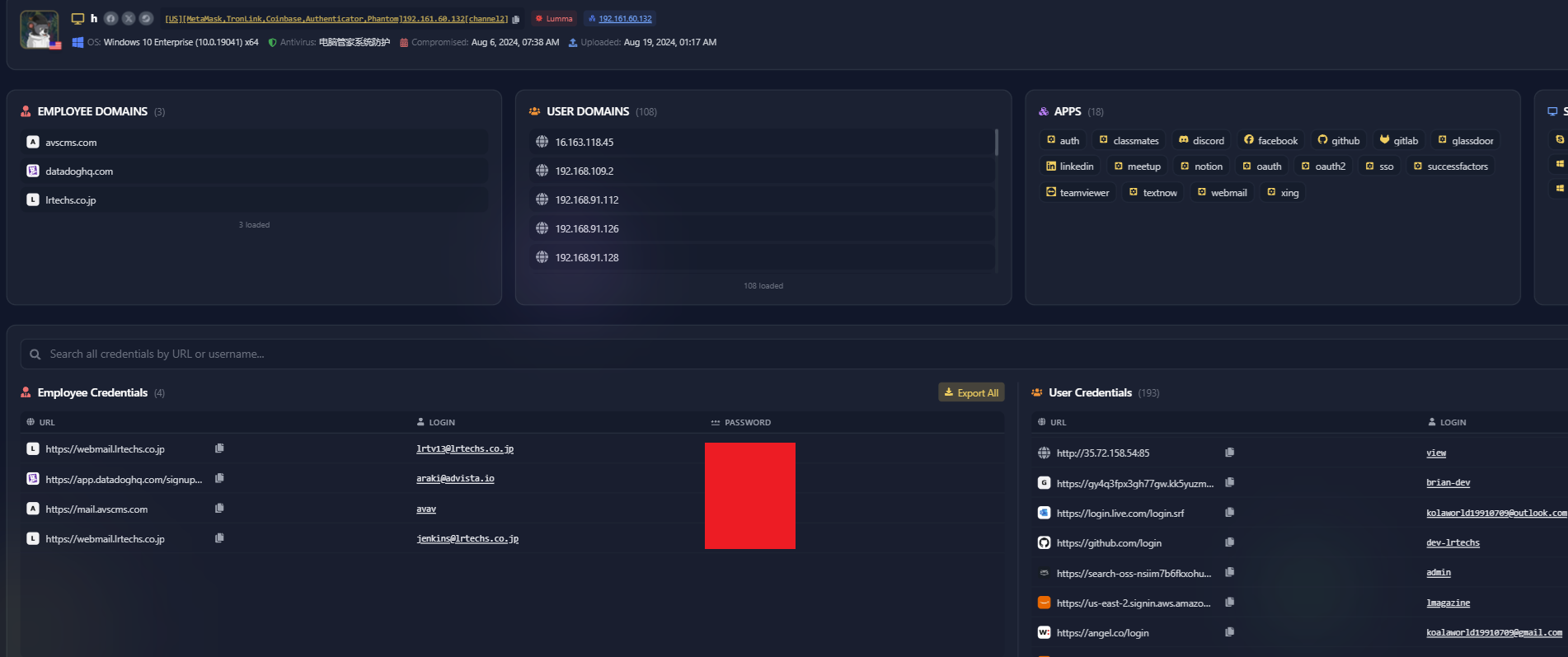
- The LummaC2 infection yielded 100+ credentials, 7,000+ browsing logs, Cloudflare admin access, and browser autofill telemetry exposing operational tradecraft.
- The actor infiltrated Gate.us under the persona “Ariel Cruz,” participating in Sumsub KYC meetings to map AML/KYC blind spots and test real fugitive profiles against detection logic.
- Telemetry proves strategic espionage: the operator exfiltrated air‑gapped network blueprints from NIMS and gained downstream access through LR Techs’ supply‑chain accounts.
- The operation included an automated Telegram‑based USDT laundering gateway, use of bulletproof hosting (Stark Industries), and credential tiering that linked the actor to the Lazarus/Suncity laundering pipeline.