Researchers identified ClipXDaemon, a Linux clipboard hijacker that targets cryptocurrency users by monitoring X11 clipboards and replacing copied wallet addresses with attacker-controlled ones to redirect funds. The loader resembles ShadowHS samples due to use of the open-source bincrypter framework, but ClipXDaemon operates C2-less, persists via ~/.profile, and uses process masquerading and Wayland checks to remain stealthy. #ClipXDaemon #ShadowHS
Keypoints
- ClipXDaemon monitors X11 clipboards and swaps copied cryptocurrency wallet addresses with attacker-controlled addresses.
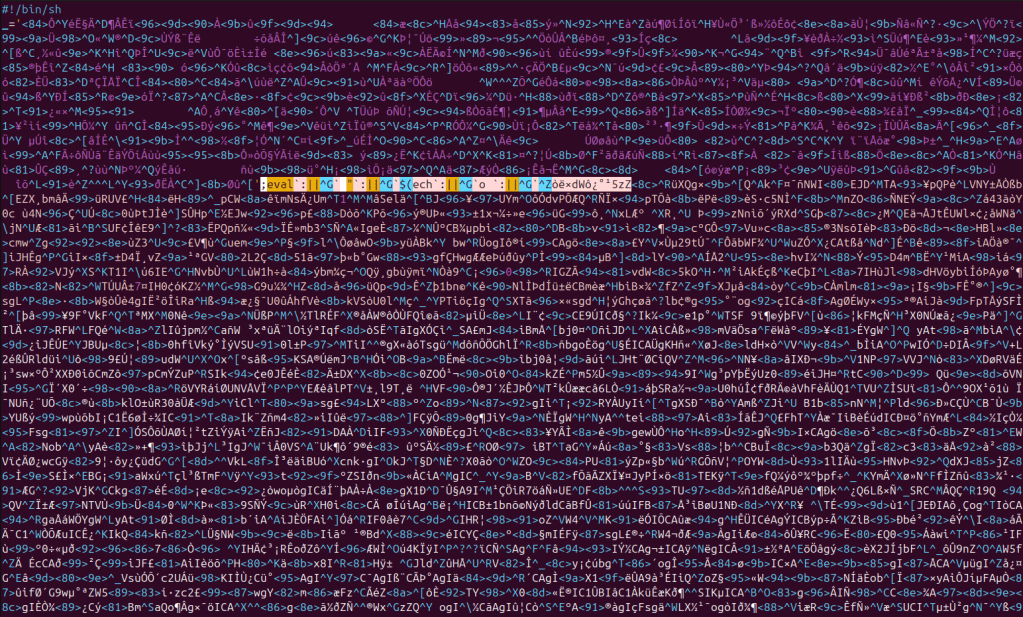
- It is deployed through a three-stage chain: an encrypted bincrypter loader, a memory-resident AES-256-CBC dropper, and an on-disk ELF daemon.
- The malware stores encrypted regex patterns and replacement addresses (decrypted with ChaCha20) and polls the clipboard every 200 milliseconds without any network activity.
- Persistence is achieved by writing the binary to ~/.local/bin and appending an execution line to ~/.profile, targeting desktop Linux users without requiring root.
- ClipXDaemon stealthily daemonizes, renames its process to mimic “kworker/0:2-events,” and terminates when a Wayland session is detected to avoid clipboard access restrictions.
Read More: https://thecyberexpress.com/clipxdaemon-linux-malware/