A Pakistan-based hacking group, APT36, is flooding Indian government networks with a new wave of low-quality, AI-generated malware—what Bitdefender calls “Vibeware”—to overwhelm defenders by sheer volume. The campaign uses niche languages like Nim, Zig, and Crystal, leverages Google Sheets and Discord for C2, and deploys intrusive tools such as LuminousCookies and BackupSpy to steal credentials and documents. #APT36 #LuminousCookies
Keypoints
- APT36 is mass-producing AI-generated “Vibeware” to overwhelm defenders by quantity rather than sophistication.
- Many samples are sloppy or broken, but sheer volume increases the chance some will bypass detection.
- Attackers use niche languages (Nim, Zig, Crystal) to evade traditional antivirus scanners.
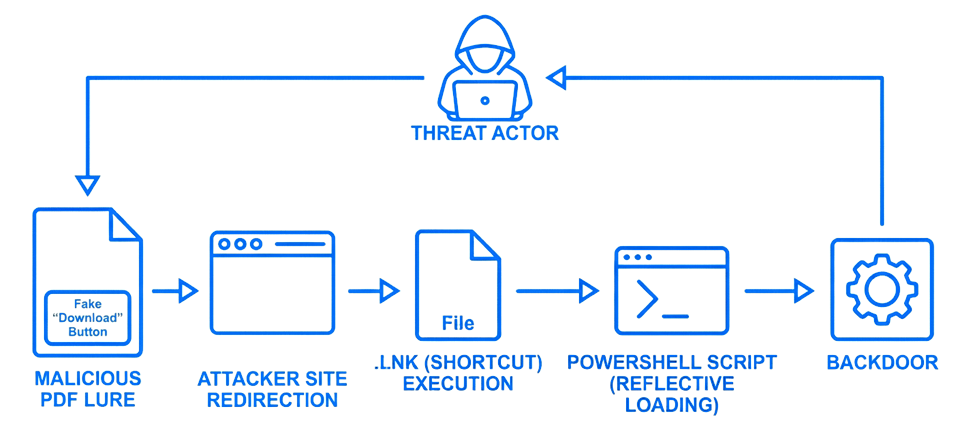
- LuminousCookies tries to bypass App-Bound Encryption by injecting into browser memory, and attackers use PDF lures and modified browser shortcuts to deliver spyware.
- Command-and-control and exfiltration use Google Sheets, Slack, and Discord, while BackupSpy scans 16 file types and keeps a manifest of stolen files.
Read More: https://hackread.com/pakistan-apt36-indian-govt-networks-ai-vibeware/