A large credential stuffing campaign targeted F5 BIG-IP devices using credentials harvested from Infostealer infections rather than from direct F5 breaches. Attackers bought or scraped Infostealer logs, then stuffed ADFS/STS SSO credentials against edge devices—often via compromised Fortinet appliances—to bypass MFA and gain network access. #Infostealer #F5_BIG_IP
Keypoints
- Threat actors performed credential stuffing against F5 BIG-IP using seemingly legitimate corporate credentials.
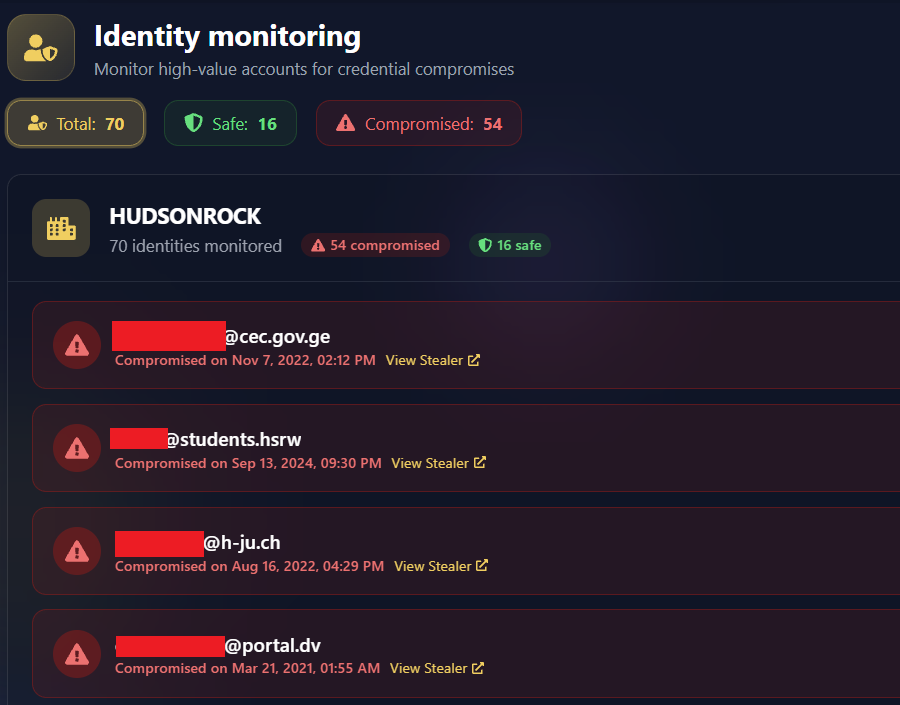
- 54 of 70 credentials (77%) matched Infostealer logs, showing harvested SSO credentials were reused.
- The stolen credentials were primarily ADFS/STS SSO credentials rather than F5-specific passwords.
- Attackers used a compromised Fortinet FortiGate as a proxy to launch attacks against other edge devices.
- Infostealer logs are filtered and sold to initial access brokers, creating a “Log-to-Lead” pipeline for access.