SURXRAT is an Android Remote Access Trojan sold as a commercial MaaS on Telegram with reseller and partner licensing that centralizes infrastructure while enabling affiliates to generate and distribute customized builds. Code links to ArsinkRAT and more than 180 identified samples show rapid evolution, and unusual features—like the conditional download of a >23GB LLM from Hugging Face triggered by Free Fire titles—signal AI experimentation for automation, evasion, and hybrid monetization. #SURXRAT #ArsinkRAT
Keypoints
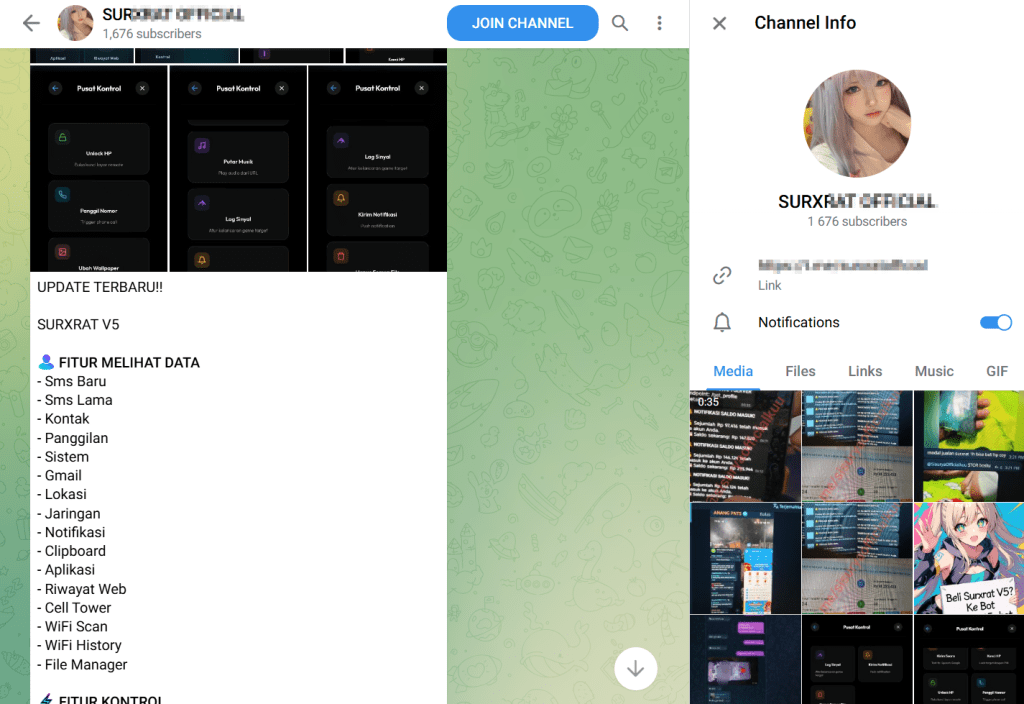
- SURXRAT is marketed via a Telegram-based MaaS with Reseller (200k) and Partner (500k) one-time license tiers and tiered daily build limits.
- Cyble identified over 180 related samples and a Telegram channel dating to late 2024, pointing to development beginning in early 2025 by a suspected Indonesian actor.
- Code references and a Firebase database label (“arsinkRAT”) indicate SURXRAT evolved from the ArsinkRAT codebase.
- Recent samples conditionally download a >23GB LLM from Hugging Face when specific Free Fire game apps run, suggesting AI-assisted cheating, evasion, or experimentation.
- Capabilities include Accessibility abuse, extensive data exfiltration, real-time Firebase C2 control, audio/camera capture, remote commands, and a ransomware-style screen locker for extortion.
Read More: https://thecyberexpress.com/surxrat-arsinkrat-llm-android-rat-analysis/