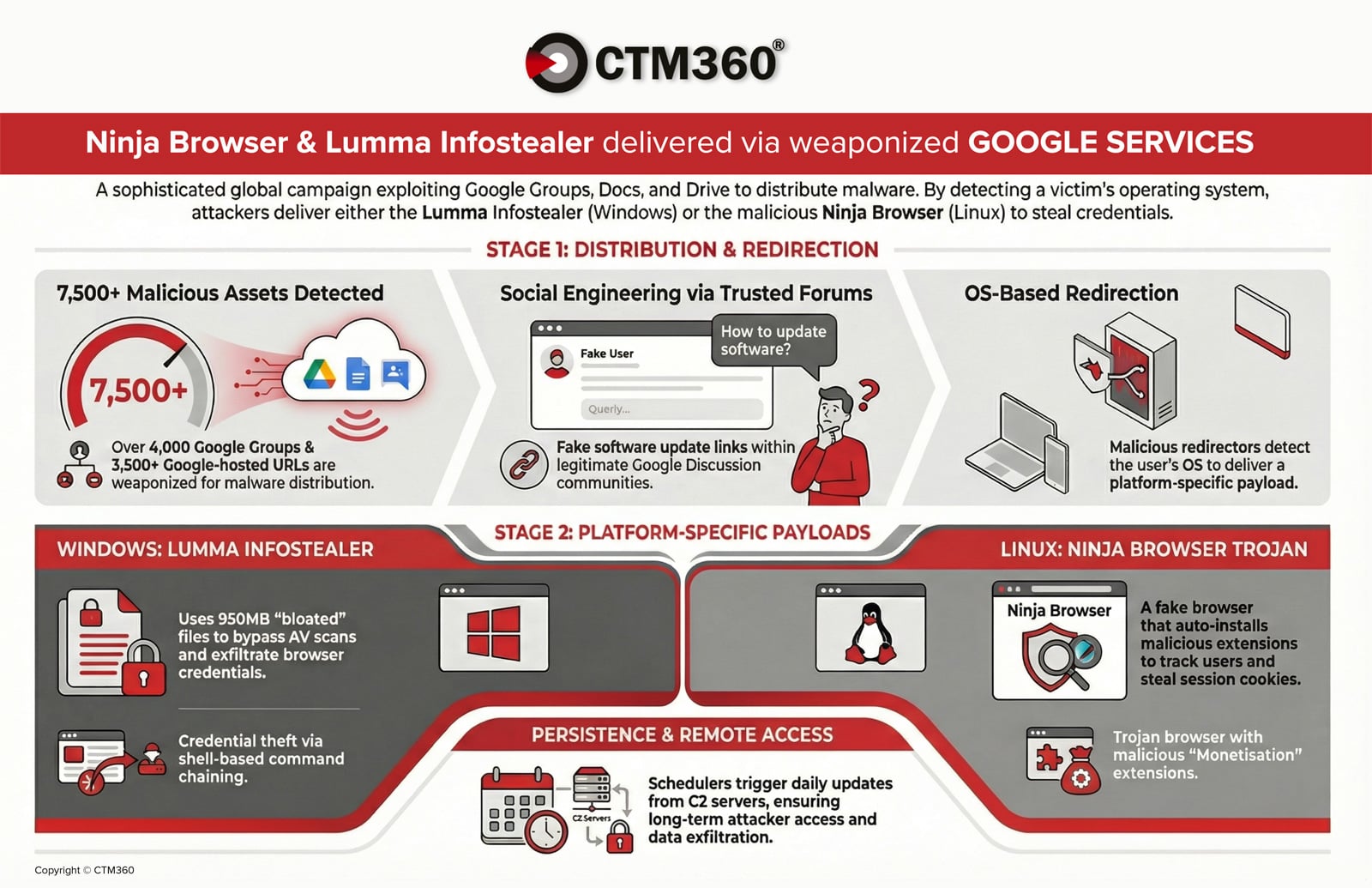
CTM360 reports an active global campaign abusing over 4,000 malicious Google Groups and 3,500 Google-hosted URLs to distribute credential‑stealing malware and establish persistent access on compromised devices. Windows users are targeted with an oversized, password‑protected archive delivering the Lumma infostealer, while Linux users are redirected to a trojanized Chromium “Ninja Browser” that silently installs malicious extensions and persistence mechanisms. #LummaStealer #NinjaBrowser
Keypoints
- Attackers abuse Google Groups and Google-hosted redirectors to increase credibility and drive malicious downloads.
- Windows infections use oversized, padded archives and an AutoIt-based loader to deploy the Lumma infostealer for credential and cookie theft.
- Linux victims are served a trojanized “Ninja Browser” that installs the “NinjaBrowserMonetisation” extension to track users, inject scripts, and exfiltrate data.
- Observed infrastructure includes C2 domain healgeni[.]live and IPs such as 152.42.139[.]18 and 89.111.170[.]100, with multiple associated SHA-256 hashes.
- Defensive actions include inspecting shortened URLs and Docs/Drive redirects, blocking IoCs at firewall/EDR, auditing extensions, monitoring scheduled tasks, and user education.