Keypoints
- The paper offers an insider perspective on CISA KEV and introduces KEV Collider for exploration and validation of KEV enrichment data.
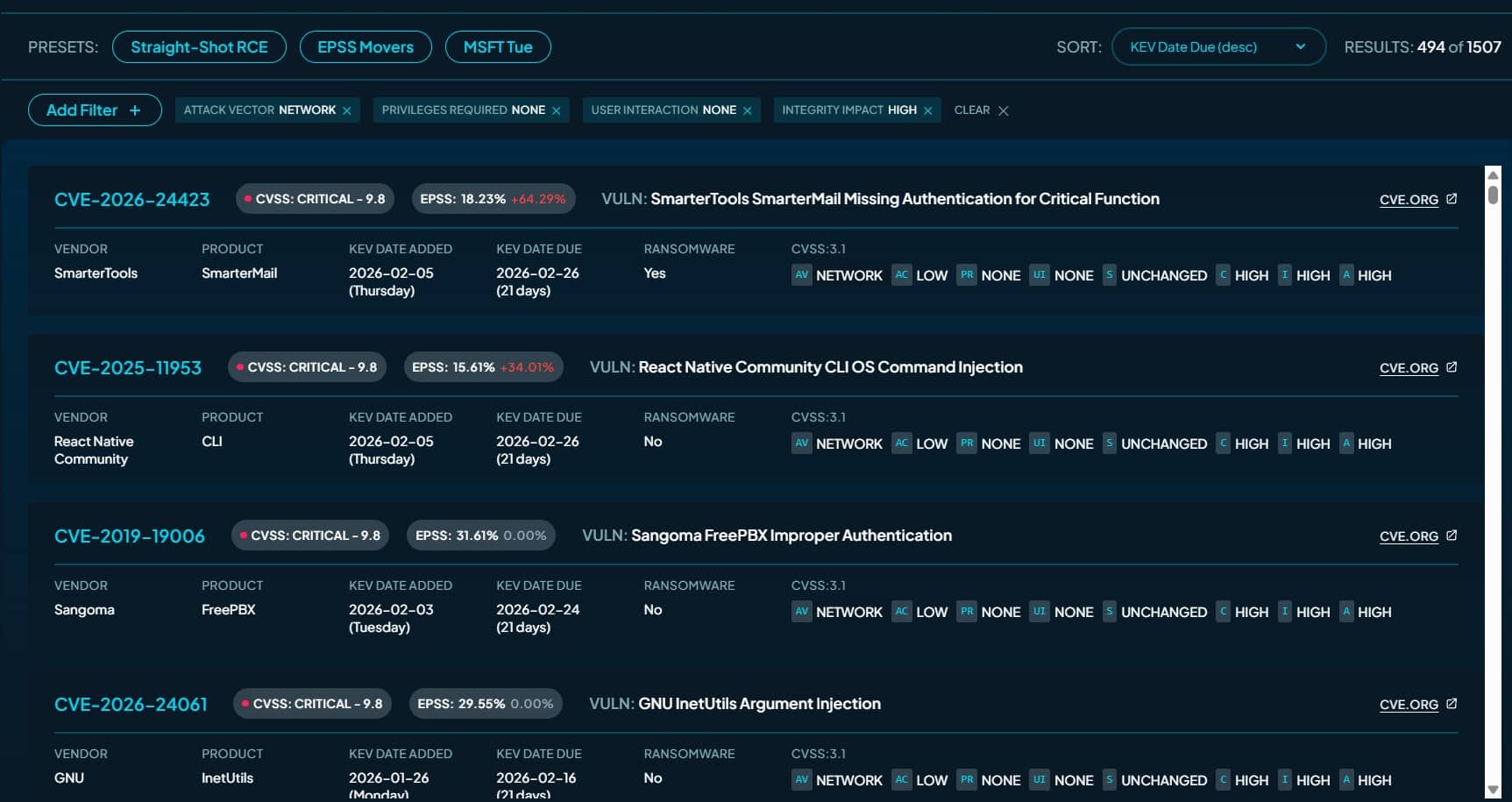
- Enrichment signals used include CVSS, EPSS, SSVC, Metasploit, Nuclei, MITRE ATT&CK mappings, and time-sequenced relationships.
- Only about 32% of KEV vulnerabilities are useful for immediate initial access, and straight-shot RCEs are a minority.
- Many KEVs have public exploit tooling: 464 linked to Metasploit modules, 398 to Nuclei templates, and 235 with both.
- KEV is an operational prioritization list with narrow inclusion criteria: CVE, mitigation path, observed exploitation, and FCEB relevance.
Read More: https://thecyberexpress.com/what-is-cisa-kev-tool-to-guide-security-teams/