Researchers uncovered a campaign using a fake VS Code extension impersonating the Moltbot AI assistant to distribute a payload that enables credential and context theft. The operation illustrates “Cognitive Context Theft,” where attackers harvest agent memories, transcripts, and plaintext configuration files from local-first AI agents like ClawdBot, risking breaches similar to the Change Healthcare incident. #ClawdBot #ChangeHealthcare
Keypoints
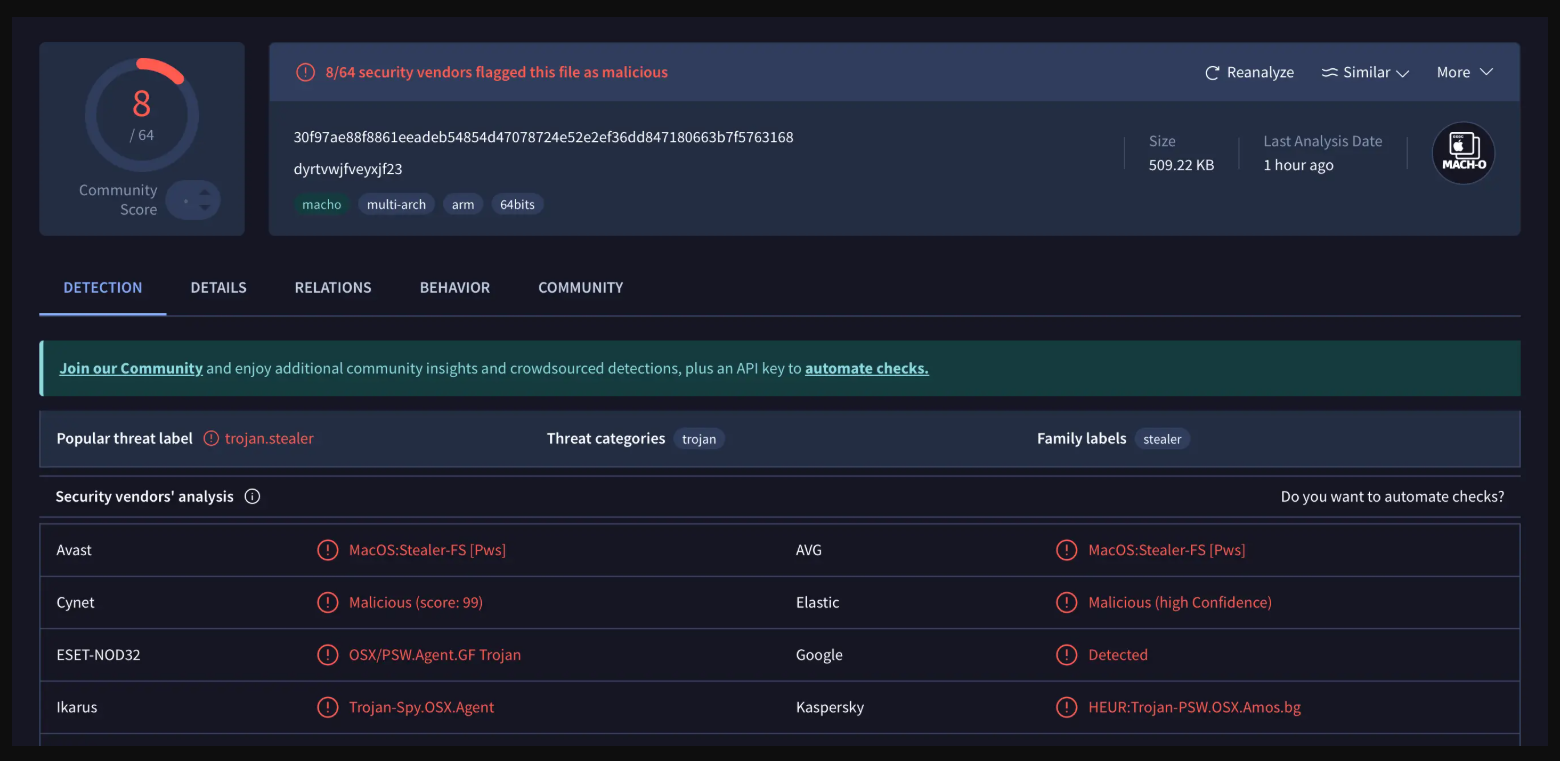
- A fraudulent VS Code extension impersonating “Moltbot” is being used to deliver a malicious payload to developers and AI power-users.
- Researchers describe the new tactic as “Cognitive Context Theft,” focused on stealing agent memories, transcripts, and environment configurations.
- Local-first AI agents such as ClawdBot often store sensitive tokens and memories in plaintext files like MEMORY.md, creating a honey pot for infostealers.
- Major MaaS families like RedLine and Lumma have adapted to scan AI directories and exfiltrate tokens, configs, and session logs.
- Real-world breaches—exemplified by the Change Healthcare VPN credential compromise—show the high impact, and Hudson Rock offers tools to detect exposed credentials.