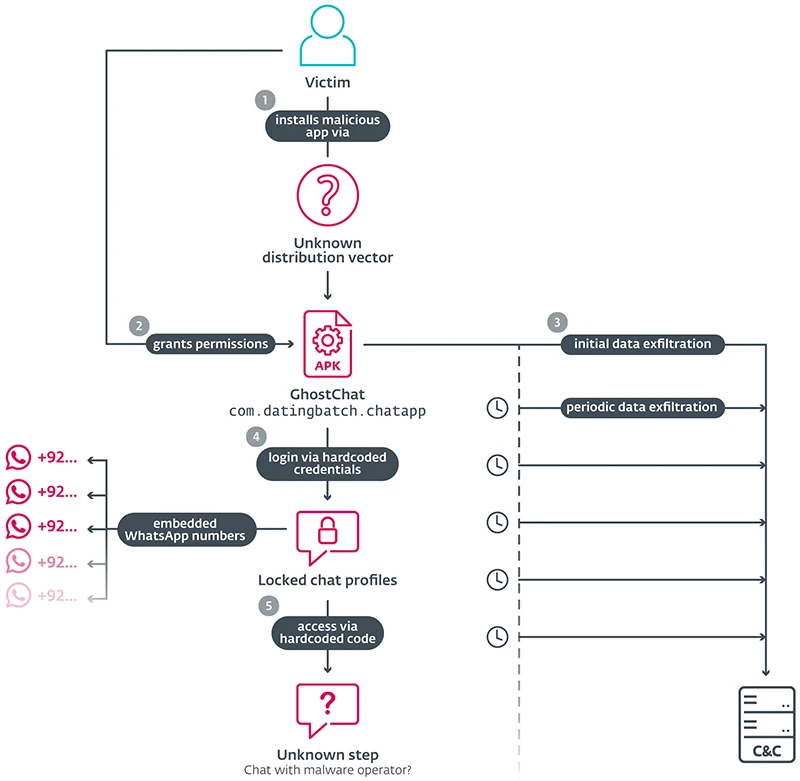
ESET researchers uncovered an Android spyware campaign called GhostChat that uses fake dating/chat profiles and romance-scam tactics to trick users in Pakistan into installing a malicious app disguised as a chat service. The app runs silent surveillance—exfiltrating images and documents—while the wider infrastructure uses ClickFix social engineering and WhatsApp QR device-linking (GhostPairing) tied to sites impersonating Pakistani government bodies. #GhostChat #GhostPairing
Keypoints
- GhostChat impersonates a legitimate dating app and uses locked female profiles with hardcoded passcodes as a social-engineering lure.
- The malicious app was distributed off Google Play and is blocked by Google Play Protect when present.
- GhostChat runs continuously in the background, uploading new images and checking for documents every five minutes.
- The campaign is part of a broader operation that uses ClickFix social engineering and fake government websites to deliver malware.
- Attackers also use WhatsApp QR device-linking (GhostPairing) to access victims’ chat history and contacts.
Read More: https://www.helpnetsecurity.com/2026/01/29/ghostchat-android-romance-spyware/